A powerful set of hacking tools originally developed for government surveillance has leaked into cybercriminals’ hands, targeting vulnerable iPhones. Security experts warn this marks the rise of a “secondhand” exploit market, amplifying risks for everyday users.
What is the Coruna Exploit Kit?
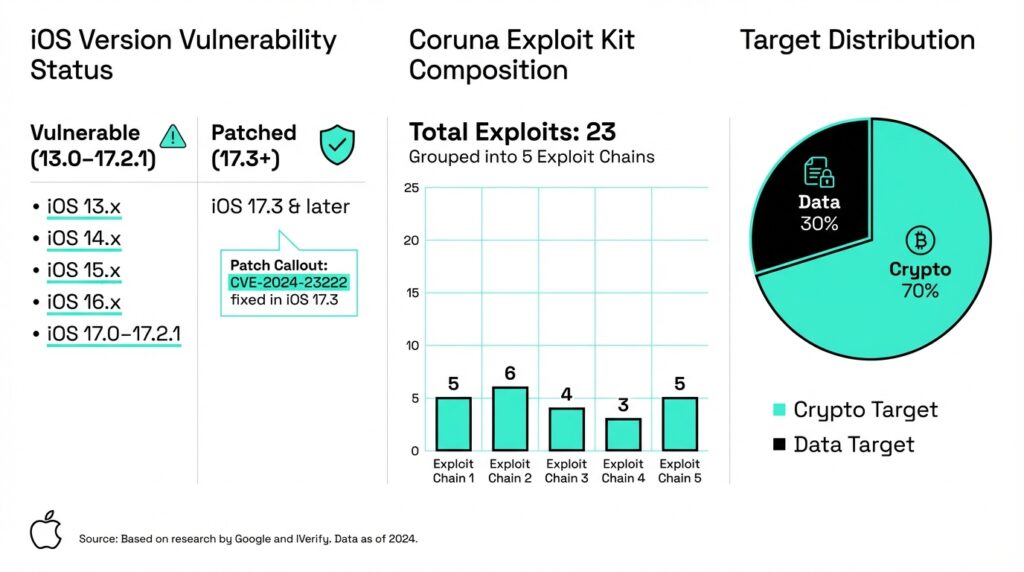
The Coruna exploit kit, named by its developers, packs five full iOS exploit chains using 23 vulnerabilities to breach iPhones from iOS 13.0 (September 2019) to 17.2.1 (December 2023). It activates via “watering hole” attacks malicious sites like fake crypto or porn pages that inject hidden iFrames with exploit code upon visit, no clicks needed.
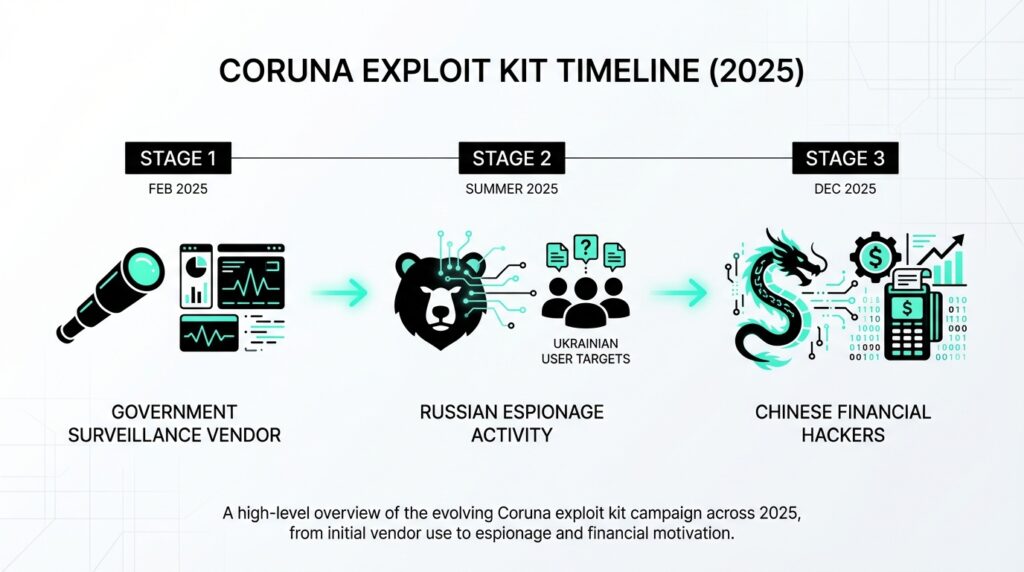
Google’s Threat Intelligence Group first spotted it in February 2025 during a spyware vendor’s government backed hack. Later, Russian group UNC6353 used it against Ukrainians on compromised sites, and by late 2025, Chinese financially motivated UNC6691 deployed it broadly on scam sites targeting crypto users worldwide.
Mobile security firm iVerify reverse engineered it, dubbing one sample CryptoWaters, and linked it to U.S. government tools due to code similarities with prior frameworks. They note its mass deployment on non-geo-fenced sites shows a shift from elite nation state ops to opportunistic crime.
How the Attack Works
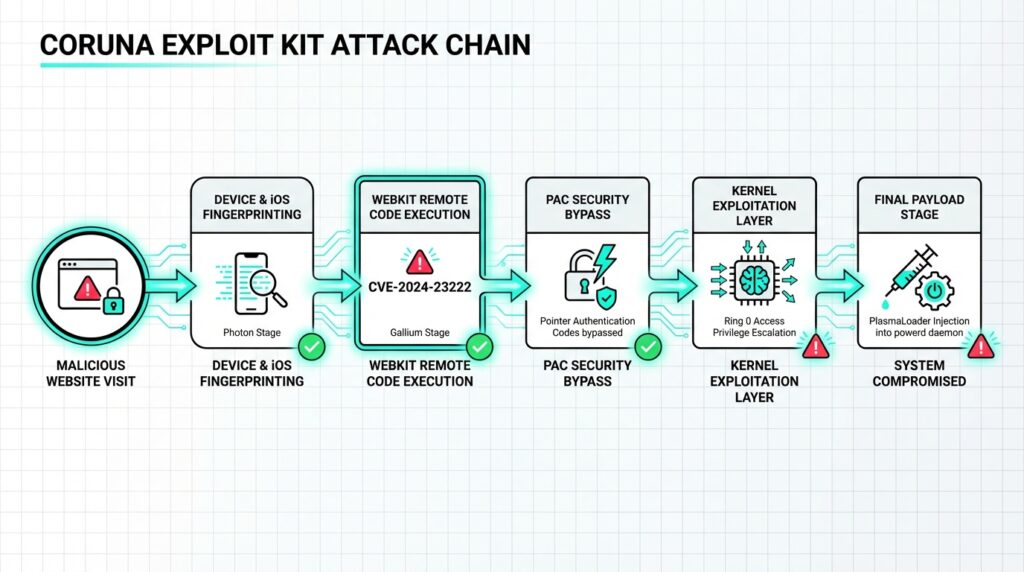
Coruna’s JavaScript framework fingerprints devices checking model, iOS version, Lockdown Mode then serves tailored exploits like WebKit RCEs (CVE-2024-23222, CVE-2022-48500). It chains them with PAC bypasses, kernel vulns, and modules like rwx_allocator to dodge mitigations, granting root access.
Once in, PlasmaLoader (PLASMAGRID) injects into root daemon powerd, stealing crypto wallet data from 17+ apps (MetaMask, Phantom, Uniswap), QR codes, BIP39 phrases from Notes/Memos, photos, emails. It fetches modular payloads via 7-Zip configs from C2 servers, using AES encrypted HTTPS with DGA fallbacks seeded on “lazarus.”
Exploits include never-before-seen techniques; 11 lack CVE IDs yet, some possibly unpatched even in older iOS. Native English comments and docstrings suggest high end origins, with LLM like emojis in Chinese logs hinting at modern dev.
Affected Devices and Patches
Vulnerable: iPhone XS/XR and later on iOS 13-17.2.1. Apple patched many chains in iOS 17.3+; full protection needs latest iOS 19.x (as of March 2026). Enable Lockdown Mode for high-risk users it bails out Coruna early.
Leak Origins and Proliferation Risks
iVerify ties Coruna to U.S. frameworks, echoing Operation Triangulation (2023 Kaspersky discovery), where U.S. allegedly hit Kaspersky iPhones via SoC hardware flaws up to iOS 16.6. Leaks happen via poor oversight, profit-driven sales, or theft once sold, control vanishes.
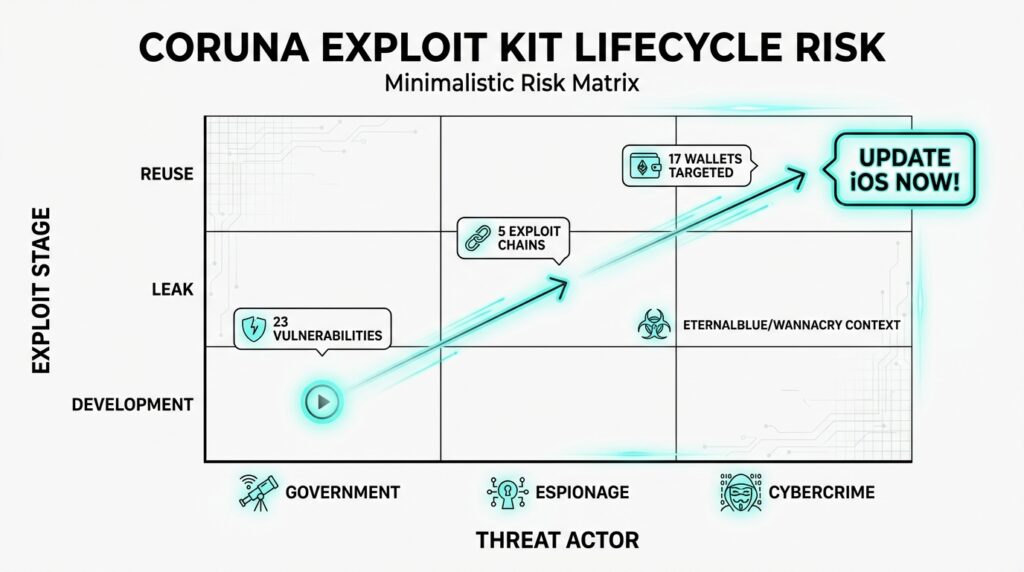
Google warns of booming “secondhand” zero day markets: surveillance vendors resell to governments, then brokers to spies or crooks. Economic pressures widen buyers, fueling Pall Mall Process talks for spyware norms.
Past parallels: NSA’s EternalBlue (2017 Shadow Brokers leak) powered WannaCry ransomware (hit 200k+ systems, $4B damage), NotPetya. Recently, ex-L3Harris exec Peter Williams got 7+ years for selling 8 zero-days to Russian/South Korean brokers, capable of hacking millions no patch confirmation.
Real World Impacts
Financially motivated hackers drain crypto wallets silently; no geo limits mean global risk, especially on scam/finance/porn sites. iVerify calls it the first mass iOS attack by criminals using nation state tools, urging daily restarts (kills non persistent malware).
Broad proliferation shares advanced primitives (e.g., Triangulation’s Photon/Gallium zero days), letting actors swap in new vulns. Enterprises lack iOS EDR; iVerify pushes Apple for security APIs like macOS.
Protect Yourself Now
Update to latest iOS immediately patches block all known chains. Use Lockdown Mode if targeted; restart daily to evict implants. Avoid sketchy links/sites; enable 2FA, reset passwords post exposure. Tools like iVerify Basic (free temporarily) scan for IOCs.
For pros: Hunt YARA rules for framework strings, monitor C2s/DGAs. Google added sites to Safe Browsing; report suspicions to CERTs. Stay vigilant leaks like Coruna show elite tools now empower street level crime
How can users check if their iPhone was infected by Coruna
Users cannot definitively detect Coruna infections on iPhones due to its stealthy root level persistence in system daemons like powerd and imagent, evading standard iOS indicators. However, security firms like iVerify and Google provide targeted checks based on their analysis.
Check with iVerify App
Download iVerify Basic (free until May 2026) from the App Store it scans for Coruna IOCs like PlasmaLoader artifacts without jailbreak. Run a full scan; it flags anomalies in sysdiagnostics, crashlogs, and process behaviors linked to the 23 exploits.
Manual Forensic Signs
- Safari History: In encrypted backups (via iTunes/Finder), search for Coruna watering hole URLs (e.g., fake crypto sites); visible in Browser History SQLite DB.
- Logs: Hunt OSAnalyticsDaily.plist, DataUsage.db, NetUsage.db, Powerlogs for powerd/imagent spikes or IPC errors like “failed lookup: com.plasma.springboard.ipc”.
- Network Traffic: Proxy HTTP shows anomalous User Agents from locationd (mismatched iOS versions); non-standard for imagent/powerd.
General iPhone Health Checks
Update to iOS 19.x+ (patches all chains) and enable Lockdown Mode first these block Coruna outright. Monitor for crypto wallet drains (MetaMask, Phantom), battery drain, or data spikes; restart daily to kill non-persistent implants.
If suspicious, factory reset after backup (excludes encrypted data), change Apple ID password via Safety Check, and scan with tools like Norton 360. Report to Apple or CERT if confirmed.
Key Additional Points on Coruna iPhone Exploits
Google’s analysis highlights Coruna’s engineering excellence, with reusable modules like rwx_allocator for RWX memory bypass and kernel PAC evasion, linking Photon/Gallium exploits to 2023’s Operation Triangulation zero days.
iVerify released IOCs via YARA rules and free scans in their Basic app (iOS until May 2026, Android briefly), detecting PlasmaLoader’s crypto theft from 17+ wallets without root checks.
Eleven of 23 exploits remain unassigned CVEs; five non public ones may lack patches even post-iOS 17.2.1, as attacks hit older versions via Safari/WebKit flaws like Sparrow (CVE-2024-23225).
No new infections or patches reported as of March 4, 2026; experts predict more leaks as vendor sales fuel criminal reuse, urging vigilance on untrusted sites.
Check out more on our blog page now → AI, Tech, Cybersecurity





