The UK’s National Health Service (NHS) has issued a clear, firm open letter to its suppliers: if you provide systems and services to the NHS, your cybersecurity cannot be an afterthought anymore. In a move to strengthen the entire health and social care ecosystem, NHS leaders are now planning direct, risk‑focused conversations with suppliers, pushing them to meet stronger security standards to protect patient care and essential services.
This is not just advice it’s a real shift in how the NHS will engage with its tech and IT partners, driven by the growing threat of ransomware and cyberattacks on healthcare.
Why the NHS is acting now
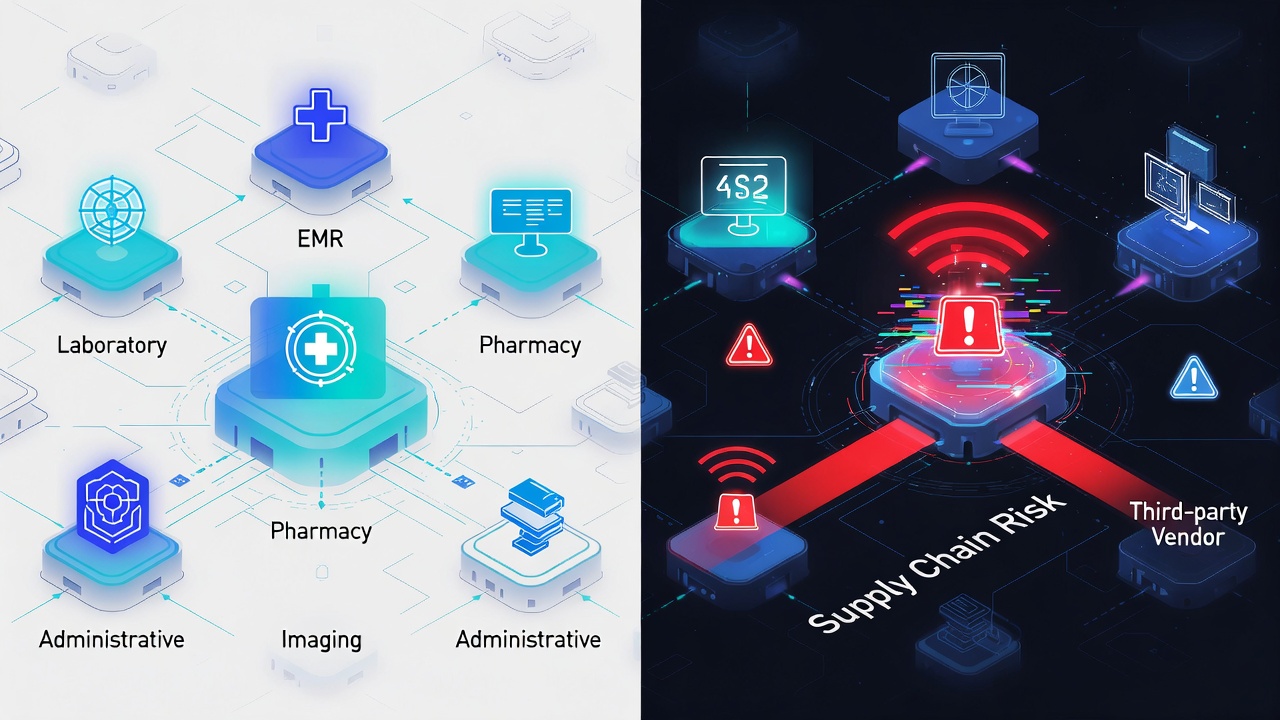
Cyberattacks are no longer isolated incidents; they are a “persistent and system‑wide risk” across the UK, and the health and care sector is a prime target, the NHS open letter warns. Ransomware, data breaches, and supply chain attacks have already disrupted hospitals, clinics, and care providers, putting patient safety and operations at risk.
The NHS’s move comes right after the UK government passed the Cyber Security and Resilience Bill and launched its Government Cyber Action Plan. Both of these national efforts demand stronger, proactive risk management across critical sectors including the NHS and its complex web of suppliers.
In simple terms: if a cyberattack takes down a hospital’s scheduling system, payroll, or patient records, the consequences are real. The NHS can’t afford weak links in its supply chain.

Building on the voluntary charter
Last year, NHS England and the Department of Health and Social Care (DHSC) already introduced a voluntary cybersecurity supply chain charter. That charter set baseline expectations for securing IT systems in the health and care sector, asking suppliers to adopt essential controls.
The new open letter makes it clear: that voluntary foundation is important, but not enough anymore. Because the threat is so large and long lasting, the NHS now needs to go beyond paperwork and drive more direct, proportionate engagement with suppliers.
Instead of waiting for a major breach, the NHS will now proactively reach out NHS England or the relevant commissioning bodies will contact suppliers to:
- Discuss key cybersecurity controls.
- Identify and understand supply chain risks that could affect patient care or operations.
- Agree on realistic, tailored actions to fix gaps and strengthen resilience.
This isn’t about a one‑size fits all audit or a “pass/fail” test. The NHS calls it a partnership: “identifying risk and working in partnership to agree proportionate remediation that strengthens resilience for everyone.”
What the NHS now expects from its suppliers
The NHS open letter lists specific actions that health and social care organisations and their suppliers must take to build stronger cyber resilience. These are not new ideas, but they are now being treated as essential minimums.
Key expectations include:
- Keep systems patched and supported Operating systems, servers, and applications must be kept up to date, with security patches applied quickly to fix known vulnerabilities. Unsupported software (like old Windows versions or end of life databases) is a major red flag.
- Maintain ‘Standards Met’ in the DSPT All NHS bodies and many suppliers must stay at “Standards Met” in the Data Security and Protection Toolkit (DSPT) the NHS’s own security and data protection framework. Falling below that will raise serious concerns.
- Apply multi‑factor authentication (MFA) wherever possible MFA must be enforced on all NHS facing systems and products. This is a basic but extremely effective way to stop account takeovers, and the NHS is making it a non negotiable for suppliers.
- Monitor and log critical infrastructure effectively Suppliers must have strong monitoring and logging in place for critical systems. This means being able to detect suspicious activity quickly and respond before an attack spreads.
- Keep unchangeable backups and test recovery plans Backups must be immutable (so they can’t be encrypted or deleted by ransomware) and stored separately from production systems. On top of that, recovery plans must be tested regularly so the service can actually come back up after an attack.
- Run board‑level cyber exercises Organisations should be running realistic tabletop or live cyber exercises at the board level, so leadership understands how to respond during a crisis, not just IT teams.

NHS cybersecurity expectations: Key actions
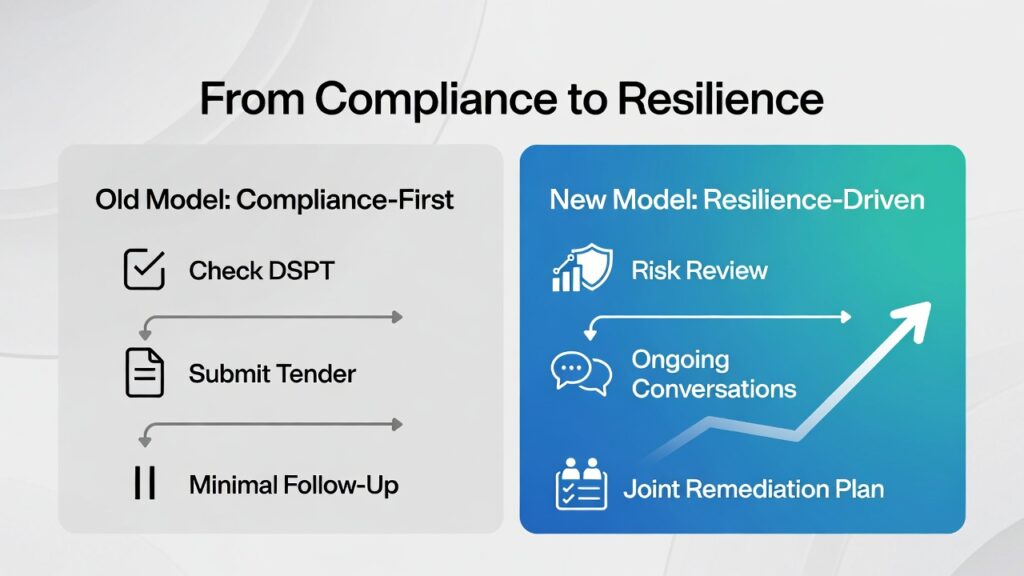
Historically, many suppliers treated cybersecurity as a “check the box” exercise for tenders or compliance. The NHS now wants to move beyond that.
The new approach is more about meaningful risk reduction than ticking boxes. When the NHS contacts a supplier, the discussion will focus on:
- What systems are connected to NHS networks or hold NHS data?
- How well are those systems updated and protected?
- What controls are in place to detect, respond, and recover from an attack?
- Where are the biggest gaps that could directly impact patient care or operations?
The goal is not to scare suppliers, but to build a more resilient, collaborative ecosystem where both the NHS and its vendors understand the risks and work together to fix them.
What this means for healthcare organisations
If you work in an NHS trust, hospital, or social care body, this letter is a clear reminder that your own security posture is now under the spotlight. Leadership, boards, and IT teams need to:
- Make sure their systems meet the DSPT “Standards Met” level.
- Ensure all NHS‑facing systems use MFA and are fully patched.
- Maintain strong, tested backups and recovery plans.
- Plan and run regular cyber exercises, including board level scenarios.
At the same time, organisations must also take responsibility for their suppliers. That means:
- Understanding which vendors have access to NHS data or networks.
- Checking that those suppliers are taking security seriously, not just claiming to.
- When the NHS contacts a vendor, being ready to share relevant information and support the risk discussion.
What this means for suppliers and tech vendors
For any company that sells software, cloud services, or IT support to the NHS, this open letter is a strong signal: cybersecurity is now a core part of the relationship, not just a nice to have.
Suppliers should:
- Review their current security controls, especially patching, MFA, logging, and backups.
- Ensure they are meeting DSPT requirements where relevant.
- Document how they handle NHS data and manage access.
- Be ready for direct contact from NHS England or contracting authorities about specific risks and possible improvements.
If a vendor is still relying on old, unsupported software, weak or no MFA, or poorly tested backups, those will be serious red flags when the NHS comes knocking.
A partnership approach to a national threat
The NHS is not proposing a punitive or adversarial scheme. It is very clear: this is about working together, not blaming or cutting off suppliers overnight. The letter explicitly thanks suppliers who are already making “substantial effort” to strengthen security.
By focusing on risk, proportionality, and partnership, the NHS hopes to:
- Reduce the overall cyber risk across health and care.
- Protect essential services and patient care from disruption.
- Build more trust and confidence in the entire sector.
This proactive, supplier facing effort is a major step toward making the UK’s health ecosystem more resilient in an age of relentless cyber threats.
The NHS is now demanding that all suppliers step up their cybersecurity game to protect patients and services. If this is a topic that matters to your organisation, do visit our other blog posts on our page under the tags AI, TECH, and CYBERSECURITY, where we break down the latest security standards, real‑world threats, and practical steps to stay safe in today’s connected world.