CISA added CVE 2024 37079, a severe VMware vCenter Server vulnerability, to its Known Exploited Vulnerabilities catalog on January 23, 2026, confirming active real world attacks. This heap based buffer overflow allows unauthenticated remote code execution, posing major risks to enterprise virtualization environments.
What Makes CVE 2024 37079 Dangerous
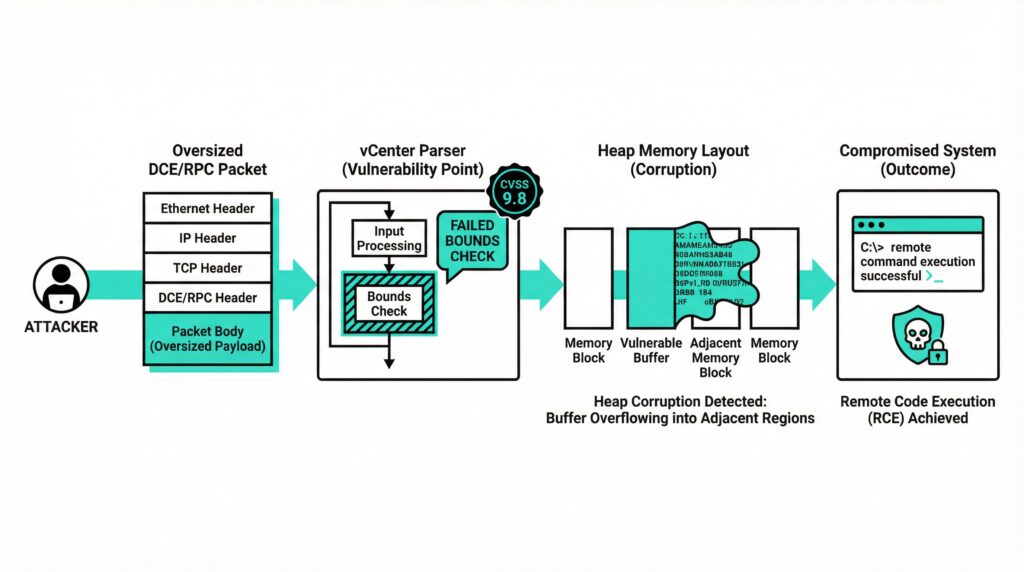
This critical flaw carries a CVSS v3.1 score of 9.8 due to its heap overflow in vCenter Server’s DCE/RPC protocol handling. Attackers only need network level access to send malicious packets that bypass authentication and trigger arbitrary code execution on the server.
DCE/RPC serves as the backbone for vCenter’s core functions including authentication, certificate management, and directory services. The vulnerability occurs during packet parsing where insufficient bounds checking allows buffer overruns, corrupting adjacent heap memory and enabling control flow hijacking.
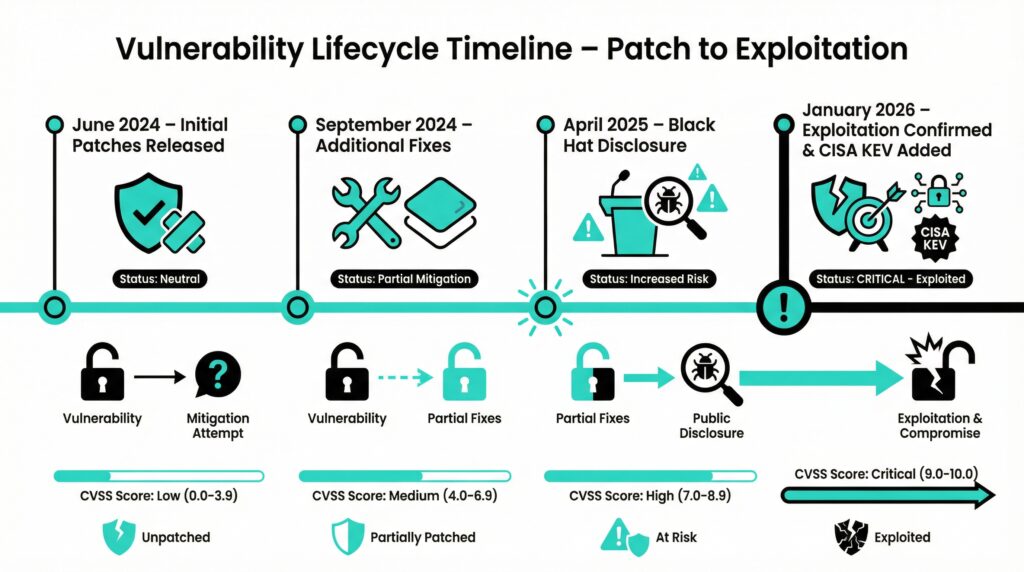
Broadcom addressed it through security advisory VMSA 2024 0012 in June 2024, simultaneously patching CVE 2024 37080 (another identical heap overflow) and CVE 2024 37081 (local privilege escalation). Credit goes to QiAnXin LegendSec researchers Hao Zheng and Zibo Li.
Complete Vulnerability Family Exposed
Black Hat Asia 2025 presentation revealed four interconnected DCE/RPC vulnerabilities: three heap overflows (CVE 2024 37079, CVE 2024 37080, CVE 2024 38812) and one privilege escalation bug (CVE 2024 38813). The final two received patches in September 2024 via VMSA 2024 0024.
Attackers can chain an initial heap overflow with the privilege escalation flaw to achieve full root access on underlying ESXi hypervisors. This combination transforms network access into complete domain domination over virtualized infrastructure.
vCenter Server manages ESXi hosts running production VMs across enterprises, clouds, and data centers. Compromise provides attackers with visibility and control over thousands of virtual machines simultaneously.
Affected Products Summary
Evidence of Active Exploitation
Broadcom updated VMSA 2024 0012 to version 1.1 on January 23, 2026, explicitly stating: “Broadcom has information suggesting CVE 2024 37079 exploitation has occurred in the wild.” Specific attack details, threat actor attribution, and compromise scope remain undisclosed.
The vulnerability provides high value footholds for lateral movement within networks. Attackers gaining vCenter access can pivot to hypervisors, extract VM configurations, deploy persistent malware, or exfiltrate sensitive virtualization data.
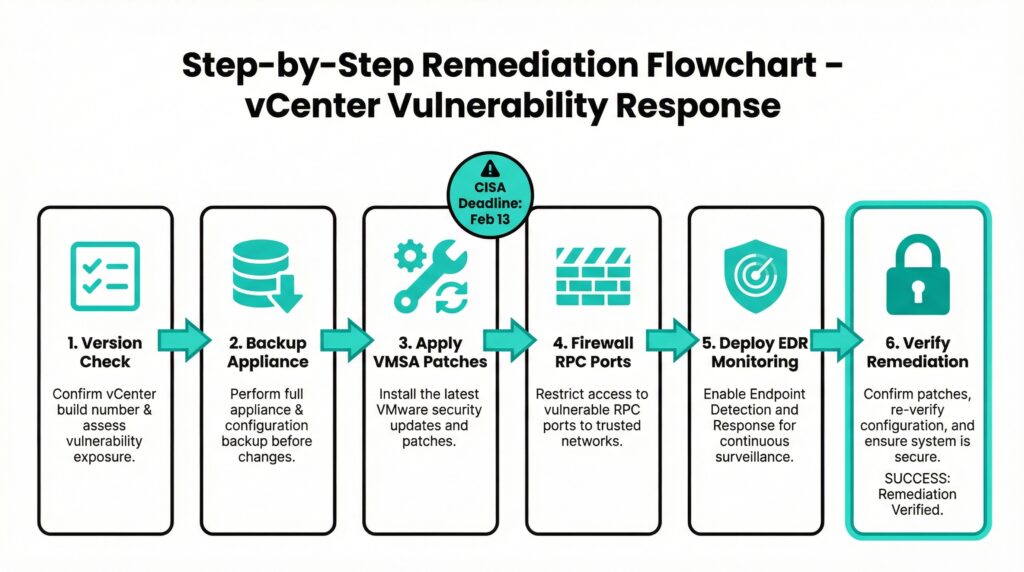
CISA’s KEV catalog inclusion triggers BOD 22 01 requirements: Federal Civilian Executive Branch agencies must apply mitigations by February 13, 2026. Private organizations should treat this as equal priority given proven exploit reliability.
Enterprise Risk Assessment
Virtualization layers represent crown jewels in modern IT infrastructure. vCenter compromise enables attackers to disrupt business operations, steal intellectual property from VMs, deploy ransomware across managed hosts, or establish persistent footholds for future operations.
Heap buffer overflows prove particularly attractive to sophisticated actors because they offer reliable memory corruption without requiring local access or user interaction. Traditional signature based defenses struggle against these low level exploits.
Organizations maintaining internet facing vCenter instances face elevated risk. Default configurations often expose management interfaces, amplifying threat exposure across exposed enterprise perimeters.
Immediate Remediation Roadmap
Step 1: Inventory Assessment
Audit all vCenter deployments against Broadcom’s affected version matrix. Cross reference build numbers through vCenter’s administration interface.
Step 2: Controlled Patching
Download VMSA 2024 0012 patches from Broadcom Support Portal. Apply updates via VAMI interface or appliance CLI, ensuring full backups exist beforehand.
Step 3: Hardened Configuration
Immediately restrict DCE/RPC port 135/TCP access through firewalls. Implement network segmentation isolating vCenter from production traffic.
Step 4: Continuous Monitoring
Deploy EDR solutions monitoring for anomalous RPC traffic patterns, heap memory anomalies, or unexpected process creation on vCenter appliances.
Beyond Patching: Defense in Depth
Implement principle of least privilege by disabling unused DCE/RPC endpoints within vCenter. Enable comprehensive audit logging and forward events to centralized SIEM platforms for behavioral analytics.
Regular vulnerability management incorporating SBOM analysis prevents recurrence of protocol level flaws. Automated patch management systems ensure timely deployment across distributed virtualization environments.
Given virtualization’s foundational role in hybrid cloud architectures, treat vCenter security with the same rigor as Active Directory or database platforms. Delayed response amplifies breach consequences exponentially
Key Takeaways & Action Plan
Urgent Patching Required: CVE 2024 37079’s addition to CISA’s KEV catalog confirms active exploitation, giving attackers reliable remote code execution against unpatched VMware vCenter Servers. Federal agencies face a February 13, 2026, deadline, but all organizations must prioritize immediate remediation to protect virtualization infrastructure.
Comprehensive Risk: This heap overflow vulnerability part of a four flaw DCE/RPC chain threatens complete ESXi hypervisor takeover, exposing thousands of production VMs to ransomware, data theft, or persistent footholds. vCenter’s central role amplifies breach consequences across enterprises and clouds.
Execute Now:
- Verify versions against Broadcom’s matrix and apply VMSA 2024 0012 patches
- Lock down DCE/RPC port 135/TCP with firewalls
- Deploy EDR monitoring for anomalous RPC traffic
- Segment vCenter networks and enable audit logging
Stay Proactive: Heap buffer overflows bypass traditional defenses, underscoring the need for continuous vulnerability management, SBOM analysis, and defense in depth strategies. Treat virtualization security as mission critical delays invite inevitable compromise.
Virtualization remains a prime target. Patch today, monitor relentlessly, and secure your infrastructure before exploitation escalates.
Stay Secure & Explore More
Act Now on CVE 2024 37079: With confirmed exploitation and CISA’s KEV deadline looming, patch your VMware vCenter immediately, segment networks, and deploy monitoring to safeguard your virtualization infrastructure from devastating attacks.
Virtualization security demands constant vigilance heap overflows like this exploit central management systems, risking entire enterprise environments.
Discover More Insights: Visit our blog page for other expert articles tagged AI, TECH, and CYBERSECURITY. Stay ahead of emerging threats and innovations!
Thanks for reading. Secure your systems today.