The gap between identity and data security is shrinking fast, creating major headaches for cybersecurity teams. A recent Netwrix report warns that by 2026, attackers will scale identity attacks to breach data defenses, especially as agentic AI takes center stage. This convergence means identity workflows like provisioning, token checks, and privilege controls directly guard sensitive data. A single glitch here can expose vast troves of information. According to industry forecasts, 80% of breaches now start with identity compromises, up from 70% last year, as hackers exploit these interconnected systems.
Attackers are ditching single credential theft for bigger prizes: identity orchestration, federation trusts, and sloppy automation setups. Why? These are the gates to critical data stores. Experts like Netwrix VP Dirk Schrader note that compromising orchestration lets hackers create trusted sessions at scale, tweak policies, and hide in plain sight within logs. Multi factor authentication (MFA) might stop a stolen password, but it won’t block a hijacked workflow. Real-world data shows breakout times averaging 48 minutes, with some as fast as 51 seconds, making rapid detection essential.

Why the Blast Radius is Exploding
Identity failures now pack a massive punch. “Attackers target orchestration because it controls access who, when, and how,” Schrader explains. One breach can ripple across cloud and SaaS environments, mimicking legit activity. Michael Bell, CEO of Suzu Testing, adds that federation trust is a goldmine: hack one provider, and you inherit access everywhere it connects. Rushed automation often leaves service accounts and API tokens exposed. Reports indicate 65% of enterprises have misconfigured non human identities, creating low-hanging fruit for exploits. Non human identities, like those for AI agents and APIs, are projected to outnumber human ones 10:1 by 2027, demanding urgent governance.
This explosion in scale ties directly to modern cloud-native setups. Traditional perimeter defenses fail when identities federate across hybrid environments, from AWS to Azure. Attackers leverage misconfigs in OAuth apps or service principals, which grew 40% in vulnerabilities last year. Organizations without unified visibility face blind spots, where a single faulty automation script grants lateral movement akin to a worm propagating unchecked.

AI’s Role in Amplifying Risks
AI supercharges this risk. Agentic AI runs endless chains of non human identities, each touching data in workflows. A weak token or over permissioned agent? It cascades into data leaks at machine speed. Schrader calls it “workflow shaped lateral movement.” Ensar Seker of SOCRadar highlights how stale privileges and broad connectors amplify mistakes, not just malice. Gartner’s 2026 forecast predicts non-human identities will dominate risks, with AI agents needing lifecycle governance like regular attestations and just-in-time access.
AI agents transform data continuously, needing real time access granted via identity systems. Nathan Vega of Starburst warns a compromised service identity enables instant exfiltration or model poisoning faster than humans can react. Industry stats show AI driven phishing surged 1,265% by late 2025, with Microsoft blocking 600 million identity attacks daily. Automated pipelines grant “broad, real time data access” without guardrails, turning small policy slips into data floods. Solutions include runtime controls and policy aware access that adapt dynamically, such as zero trust models enforcing context like device posture and behavior analytics.
Beyond agent chains, AI introduces synthetic identities fake profiles blending real and fabricated data. Projections estimate $40 billion in AI fraud losses by 2027, with 82% of fraud targeting authentication layers. This shift demands biometric-resistant auth, like passkeys adopted by 48% of top websites, slashing sign-in time by 73%.

Insurers Tighten the Screws
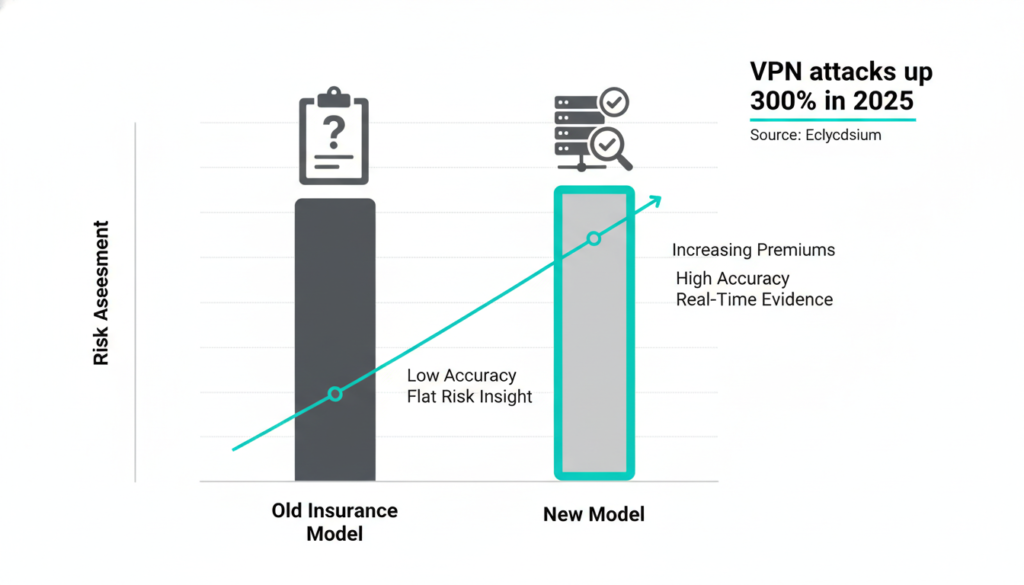
Cybersecurity insurers are overhauling risk models, ditching annual questionnaires for real time evidence like configs, patches, and backups. Schrader says ransomware and supply chain hits exposed self reported flaws. Paul Asadoorian of Eclypsium points to 2025’s VPN/firewall surge attacks demanding huge ransoms, up 300% in volume. Insurers now demand edge device audits and monitoring. Rich Seiersen of Qualys predicts moderate premium hikes and picky underwriting, but a systemic event like a cloud outage could spike it. Arvind Parthasarathi of Cygnvs agrees: no budget guarantees breach-proof status anymore.
Qualys anticipates no return to past harsh markets, influenced by macro factors like interest rates. Still, stronger controls pay off insurers favor telemetry proving identity data alignment, potentially improving terms for compliant orgs. World Economic Forum’s 2026 Outlook notes 94% of leaders see AI as the top cybersecurity driver, pushing evidence-based underwriting with metrics on vulnerability patching and incident response maturity.
Key Shifts for Security Teams
The big lesson? Treat identity and data as one unified front. Vega stresses hardening orchestration and federated governance first. Seker warns siloed teams lose to misconfigs and over permissions. Bell nails it: AI’s real danger is the ungoverned access it demands. Forward thinking orgs invest in lifecycle controls, vendor planning, and unified visibility.
Identity is now the “control plane” for security, per experts, collapsing IAM, PAM, and IGA into platforms sharing a single identity graph. By 2026, this convergence defines success: unified tools detecting human/non human risks equally. Practical steps include continuous validation of automation, self protecting data with metadata policies, and AI trust governance to counter slowdowns in unreliable models. With vishing up 442% and IoT expanding attack surfaces, resilience hinges on proactive identity data fusion.
Blog Summary
Cybersecurity teams face a mounting crisis as identity and data security converge, amplifying risks from AI driven attacks and flawed automation. Attackers target orchestration layers for massive blast radius impacts, while non human identities explode 10:1 by 2027. Insurers demand real time evidence over questionnaires, hiking premiums amid VPN surges and systemic threats. Key takeaway: unify visibility, harden workflows, and govern AI access to stay ahead in 2026’s threat landscape.
Explore More Insights
Dive deeper into cutting edge topics! Visit our other blogs on AI, TECH, and CYBERSECURITY for the latest trends, expert analysis, and actionable strategies tailored for tech enthusiasts and security pros.





