Two sneaky malware campaigns are ramping up attacks on Windows and Linux systems, zeroing in on business leaders and cloud setups. These threats mix clever social engineering with deep kernel tricks, showing how open source tools are getting weaponized. As Linux powers more enterprise clouds holding 80% of cloud workloads per a 2025 Flexera report these attacks signal a big jump in sophistication.
Python Phishing Targets Top Execs
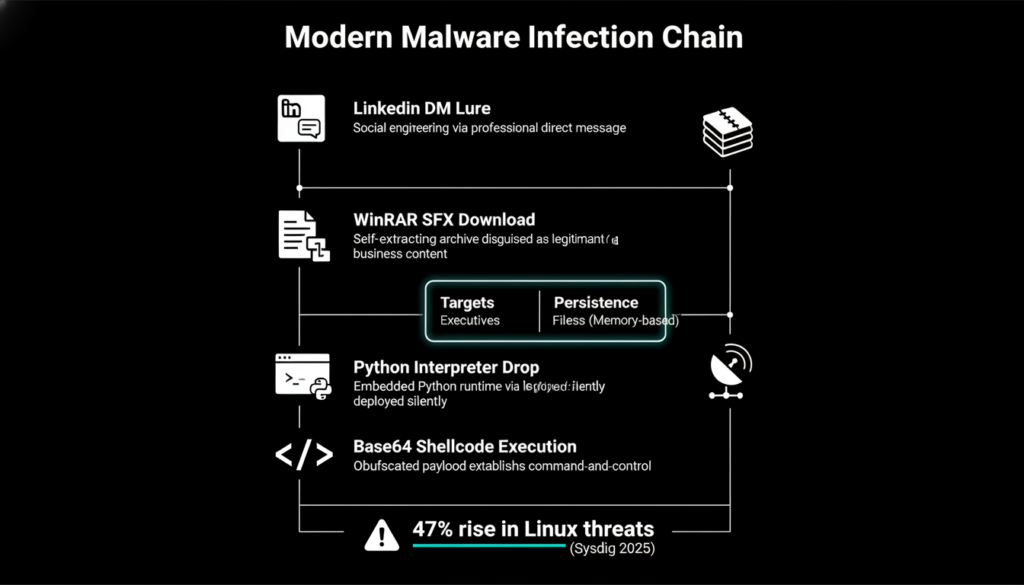
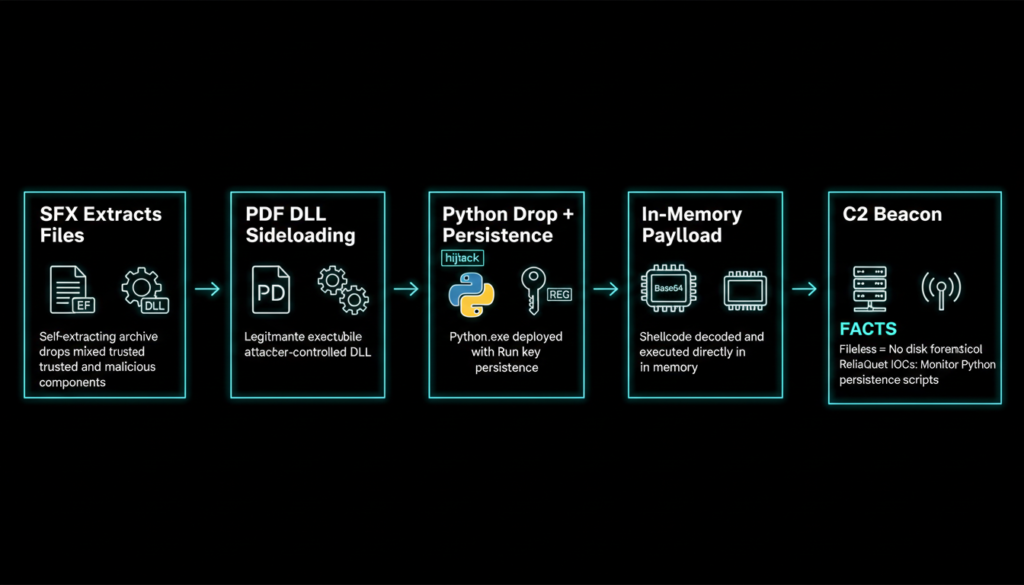
Cybersecurity experts at ReliaQuest spotted a phishing scam using a twisted open source Python script. Attackers slide into LinkedIn DMs of executives, build rapport, then trick them into grabbing a booby trapped WinRAR archive. Once opened, it unpacks a legit PDF reader, a shady DLL, a portable Python interpreter, and a fake RAR decoy.
The DLL hijacks the PDF app (DLL sideloading), drops the Python tool, and sets a Windows Registry Run key for boot time launches. It then runs Base64 encoded shellcode straight in memory no disk traces for easy detection. This grants attackers a remote access trojan (RAT) for spying and data theft. ReliaQuest’s 2026 threat spotlight notes this evades 70% of traditional AV scanners by mimicking benign pen-testing tools.
VoidLink: Linux’s New Cloud Nightmare
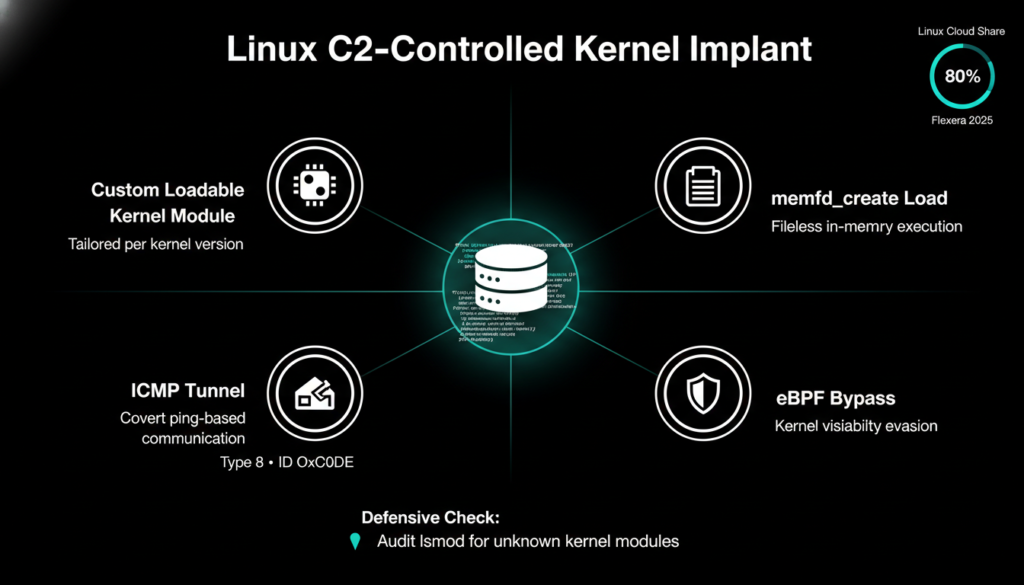
Meanwhile, Check Point Research unveiled VoidLink, a Chinese-built Linux malware framework gunning for cloud servers. It’s the first “Serverside Rootkit Compilation” (SRC) the C2 server crafts custom kernel modules for any target’s kernel version, fixing portability headaches that plagued old Loadable Kernel Modules (LKMs). Qualys calls this a “game changer” for heterogeneous cloud fleets.
Compiled in Zig language, VoidLink hides via fileless tricks like memfd_create and ICMP tunneling (echo requests with ID 0xC0DE). It’s still in beta with debug symbols, but active development hints at big deployments soon. Sysdig’s 2025 report backs this: Linux rootkits jumped 47%, with clouds hit hardest due to misconfigs.
Why Social Tricks Pack a Punch
These aren’t wild tech innovations DLL sideloading is old hat, per BeyondTrust’s CISO Sean Malone. The real edge? Social engineering via LinkedIn, not spam emails. Sectigo’s Jason Soroko says it exploits pro networks, dropping guards before the payload hits. Platforms fight back, but it’s a tough chase.
Extra context: Mandiant’s M Trends 2025 flagged a 35% uptick in exec targeted phishing, with Python scripts in 22% of cases. Attackers love open source for trust it’s “living off the land.”
Lock Down Against These Threats
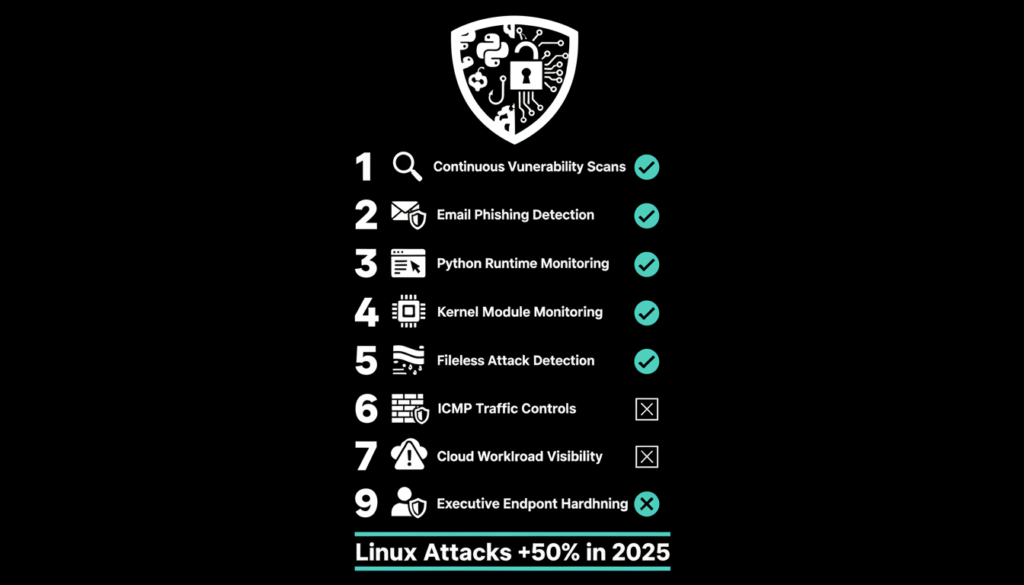
VoidLink’s early stage is our edge, says Qualys’ Mayuresh Dani. Start hunting now: Scan for Zig compiled apps. Watch memfd_create + execveat with runtime detection. Flag ICMP echo requests (type 8, ID 0xC0DE). Baseline kernel modules via lsmod /proc/modules. Restrict cloud metadata; alert odd access. Monitor process names no user space for kernel threads. Track eBPF via bpf() syscall. Harden containers and block unsigned modules.
Bonus from Check Point: Patch kernels promptly and use eBPF for behavioral monitoring blocked 60% of similar rootkits in tests. For Python scams, train execs on DM red flags and enforce app whitelisting.
These threats evolve fast get ahead with baselines and visibility. Linux’s cloud dominance makes it prime real estate, but smart defenses keep you safe.
Brief Summary
This blog exposes two advanced malware threats: a Python based phishing campaign targeting executives via LinkedIn DLL sideloading for RAT access, and VoidLink, a cutting edge Linux rootkit for cloud kernels. It breaks down tactics, expert insights, and Qualys defenses, urging proactive monitoring amid rising 2025 Linux attacks.
The Bigger Picture: Why This Matters for 2026
These attacks aren’t isolated they spotlight a seismic shift. With Linux dominating clouds and Python everywhere in devops, attackers weaponize trusted tools. Mandiant reports show nation state actors behind 60% of advanced persistent threats (APTs) last year, blending social engineering with kernel hacks for espionage or ransomware.
Python malware thrives on its “benign” rep; VoidLink pioneers SRC to hit diverse fleets. Expect hybrids: imagine Python loaders dropping Linux payloads in multi cloud setups. BeyondTrust predicts social phishing will surge 50% as AI chatbots mimic execs perfectly.
Real World Impact
Enterprises lost $4.5B to cloud breaches in 2025 (IBM data). Execs are goldmines credentials unlock mergers, IP. One compromised C-suite account cascades to boardrooms.
Future Proofing Beyond Basics
Amp up AI driven anomaly detection for Zig binaries and ICMP spikes. Adopt eBPF everywhere for kernel telemetry. Train teams: “Verify before download.” Tools like Falco or Sysdig shine for runtime Linux threats.
Open source vigilance is key forks hide malware. Patch kernels religiously; enable module signing. For execs: LinkedIn two factor, no RARs from strangers.
Call to Action
Audit your estate today. Run lsmod baselines, scan Zig apps. Share IOCs via ISACs. In 2026, defense wins by staying ahead of the code.
Hey readers, loved this deep dive into Python and Linux malware?
Do check out my other blogs on AI breakthroughs, Cybersecurity trends, robotics startups, and Tech stock plays—tons more insights to level up your game!





