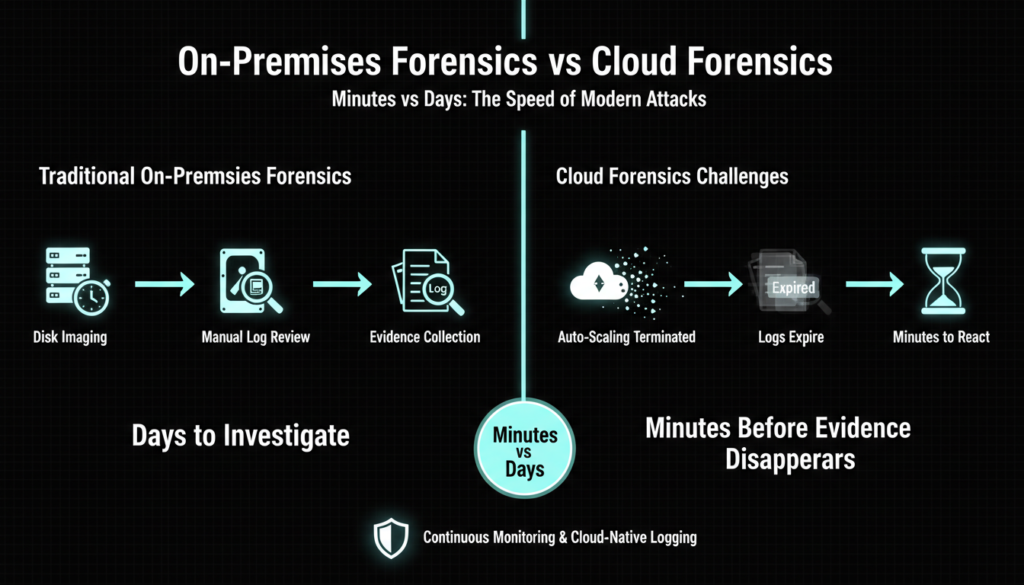
Discover how AI powered cloud forensics revolutionizes SOC teams, reconstructing breaches in minutes. Overcome traditional IR failures with context aware tools.Cloud attacks strike swiftly, outpacing traditional incident response teams. Unlike on premises setups where teams had days to collect disk images and review logs, cloud environments feature ephemeral infrastructure that vanishes in minutes, with rotating identities and expiring logs erasing evidence rapidly. This shift demands new strategies, as attackers exploit the cloud’s elasticity to pivot quickly across regions, services, and accounts.
Why Traditional Response Fails in Cloud
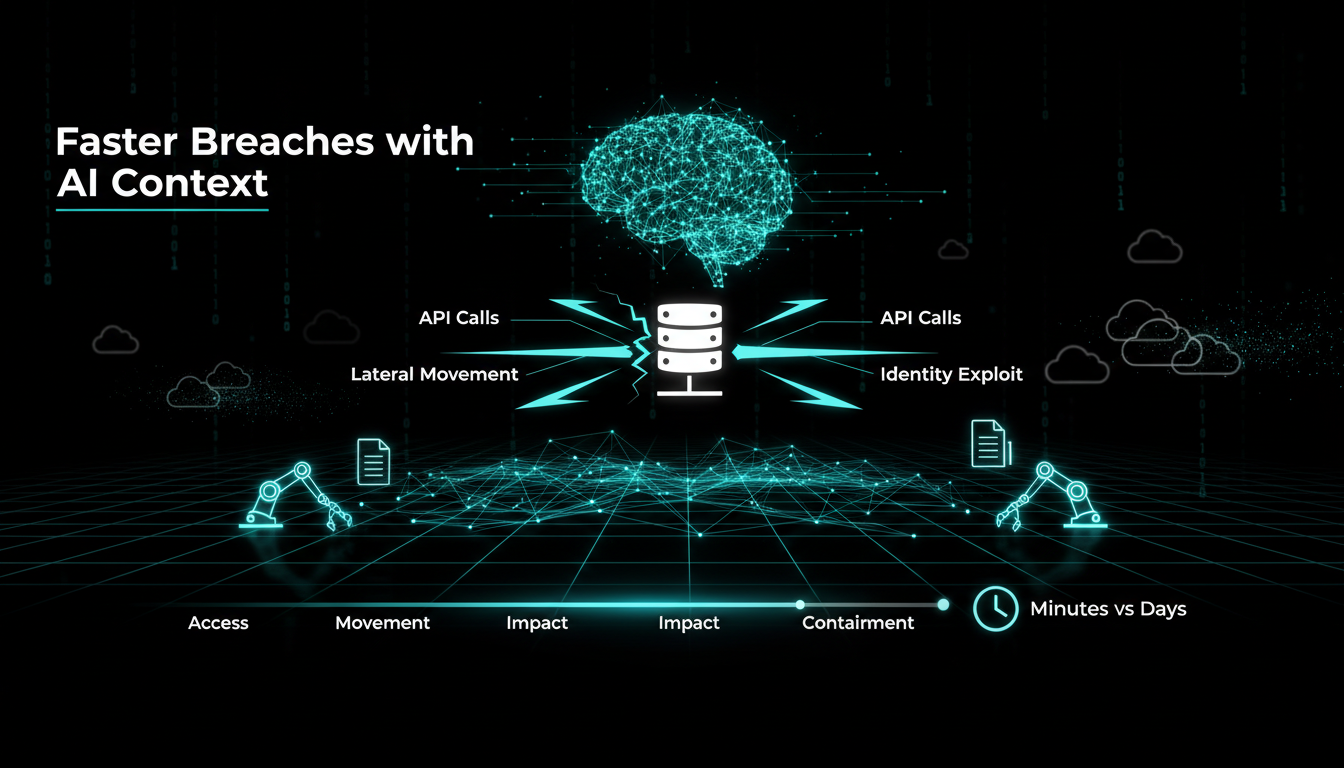
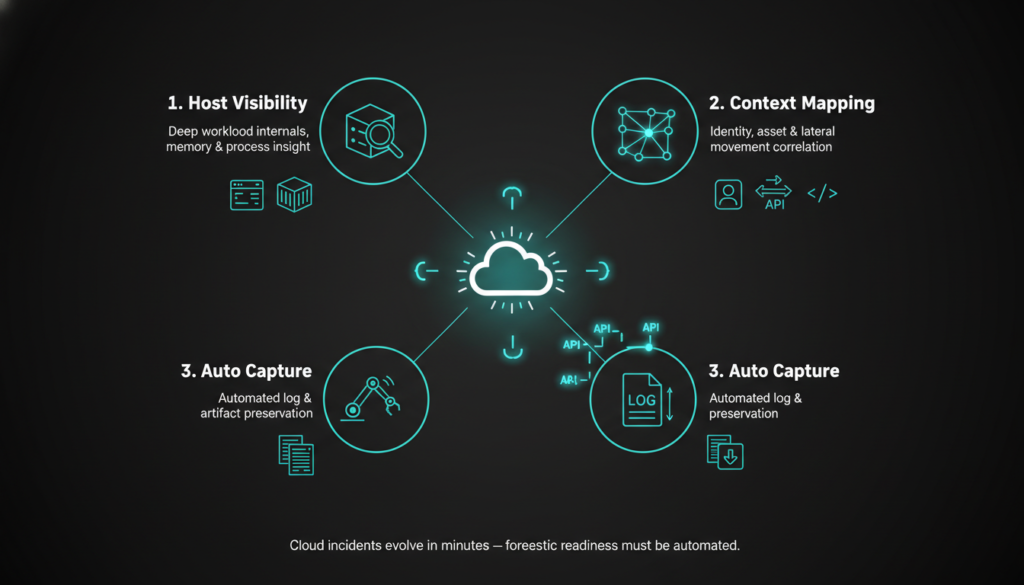
Teams often get isolated alerts like suspicious API calls or unusual logins without full context, leaving attack paths hidden. Attackers exploit this by moving laterally and escalating privileges before responders connect the dots. Effective cloud investigations demand host level visibility into workloads, context mapping of identities and assets, and automated evidence capture to avoid manual delays.
Traditional methods, rooted in static on premises environments, struggle with cloud’s dynamic nature. Incident response phases preparation, detection, containment, eradication, recovery, and lessons learned become chaotic without proactive forensic data, as logs from providers like AWS or Azure are retained briefly and can be deleted by attackers. Multi cloud and hybrid setups compound issues, with data siloed across AWS CloudTrail, Azure Monitor, and Google Cloud Audit Logs, forcing analysts to chase ephemeral metadata across incompatible formats.
In 2026, breaches like the recent exposed S3 buckets and misconfigured Kubernetes clusters underscore these gaps, where 60% of incidents involve identity based attacks via stolen tokens or over-privileged IAM roles. Without runtime visibility into runtime behaviors such as container escapes or serverless function injections teams miss subtle persistence tactics like backdoor Lambda functions.
Modern AI Driven Cloud Forensics
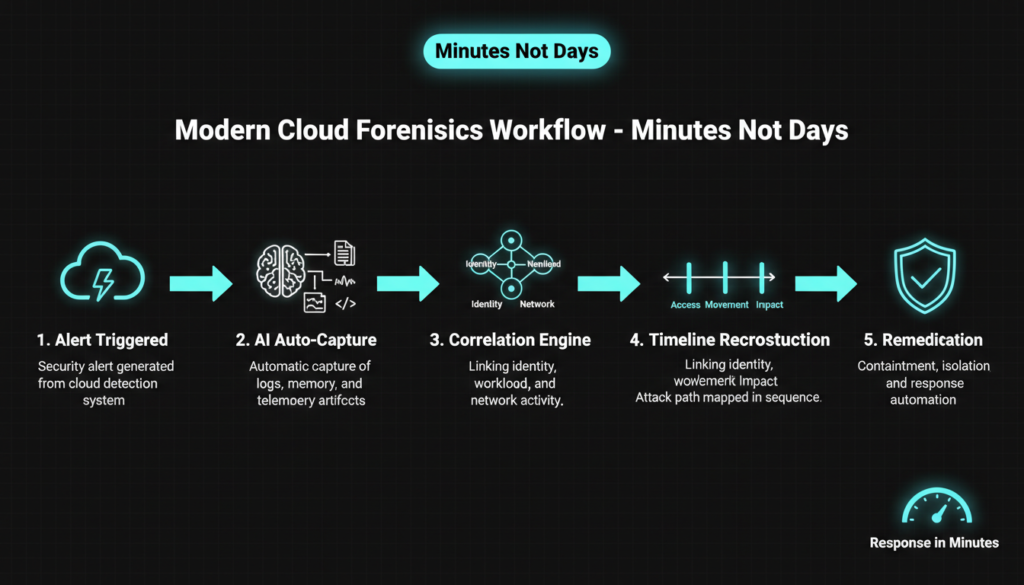
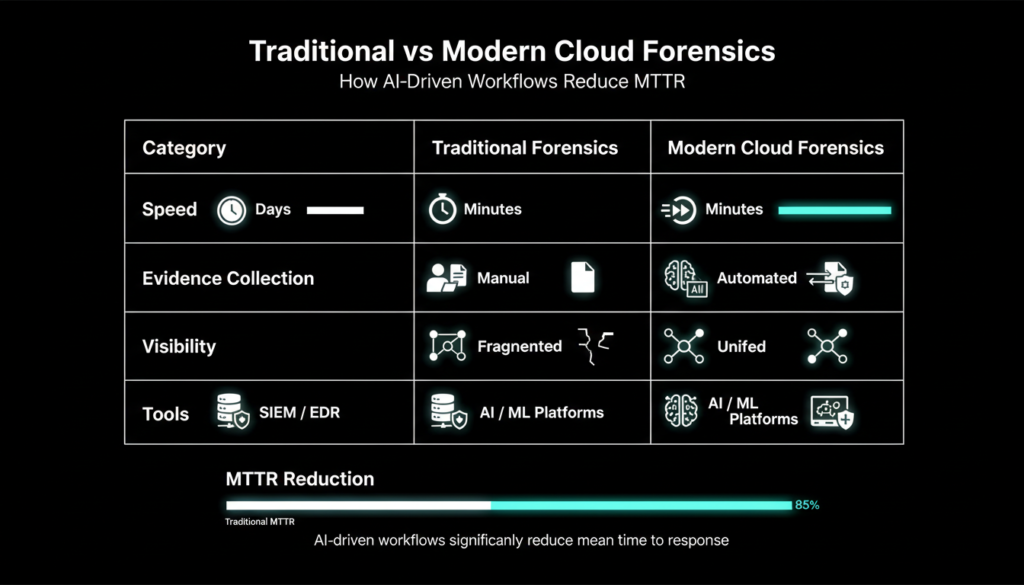
Modern SOC teams use AI and context to reconstruct incidents from correlated signals like workload telemetry, identity activity, API ops, network flows, and asset links, building attack timelines in minutes. This unified layer ends tool pivoting across consoles, shifting from reactive reviews to structured reconstructions with contextual steps for faster scoping and remediation.
Tools like Darktrace’s Forensic Acquisition automate evidence from ephemeral resources, triggered by detections, delivering root cause analysis rapidly. Wiz Forensics employs AI for contextual collection at runtime, tackling evidence disappearance. Best practices include comprehensive logging, MFA/RBAC, regular backups, cloud specific IR plans, and CSP collaboration. Platforms such as Microsoft Sentinel integrate AI-driven UEBA (User and Entity Behavior Analytics) to flag anomalous Graph API calls, while Splunk and Elastic use ML for log anomaly detection.
Investigation methods emphasize preserving volatile data, using provider APIs, timeline analysis, and cross-source correlation. In 2026, with rising breaches (e.g., exposed storage incidents) and regulations complicating response (74% report privacy rules hinder IR), AI bridges the gap for proactive hunting via UEBA, ML detections, and Sentinel like platforms. Emerging trends include generative AI for hypothesis generation simulating attack paths from partial evidence and federated learning across CSPs to detect novel threats without data sharing.
Real-world examples abound: In a 2025 AWS breach simulation, AI tools reduced MTTR from 48 hours to under 30 minutes by auto correlating GuardDuty alerts with VPC flow logs and EBS snapshots. Similarly, Azure’s Defender for Cloud now embeds forensic snapshots in incident timelines, enabling rewind and replay analysis.
Essential Best Practices
Enable full logging across services, implement strict access controls, and develop incident plans tailored to cloud. Maintain chain of custody, validate findings multiply, and train regularly. Proactive forensic readiness cuts mean time to respond (MTTR), vital as 89% of orgs suffer damage pre containment in cloud.
- Preserve volatile data immediately via APIs like AWS Instance Metadata or Azure Instance Metadata Service.
- Correlate artifacts from identity (Okta, Entra ID), network (VPC flows, NSG logs), workloads (Falco, Sysdig).
- Use AI tools for pattern detection and link analysis, integrating with SOAR platforms like Palo Alto Cortex XSOAR.
- Document meticulously for compliance and lessons learned, leveraging immutable storage like S3 Object Lock.
Argus like platforms exemplify AI correlating chats, banks, devices for suspect links, geospatial tracking enhancing investigations. Additional steps include chaos engineering for IR drills, zero trust segmentation to limit blast radius, and threat hunting with tools like Chronicle or Panther for retroactive queries on petabyte-scale logs.
For SOC maturity, adopt the NIST Cybersecurity Framework tailored for cloud: Identify critical assets via CSPM (Cloud Security Posture Management), Protect with encryption at rest and runtime protection, Detect via continuous monitoring, Respond with playbooks automating isolation (e.g., quarantining EC2 instances), and Recover through orchestrated snapshots and blue green deployments.
Overcoming Cloud Challenges
Fragmented evidence across systems stalls probes; AI unifies it for behavioral anomaly detection and fusion rules. Talent gaps in cloud/security expertise amplify issues, but automation empowers smaller SOCs. Recent 2026 trends highlight AI’s role in proactive forensics amid expanding attack surfaces and compliance pressures.
Preparation reigns: Know log retention (e.g., AWS 90-day default for CloudTrail), prep data pulls via subscriptions to event buses, store backups off-provider in air gapped vaults. Post incident, analyze for systemic weaknesses, retaining evidence per policy like GDPR or PCI-DSS. This evolves SOCs from reactive to resilient against fast-evolving threats.
Challenges persist in serverless and edge computing, where functions execute in milliseconds without persistent storage. AI counters with ephemeral forensics, capturing memory dumps and invocation traces. Cost management is key optimize logging to avoid ballooning bills during attacks, using sampling and aggregation. Integration with EDR like CrowdStrike Falcon or SentinelOne ensures endpoint cloud convergence.
Future proofing involves quantum resistant crypto for logs, AI explainability for legal defensibility, and collaborative ecosystems like FS-ISAC for shared IOCs. With President Trump’s 2026 executive orders emphasizing critical infrastructure security, SOCs investing in AI forensics gain competitive edges in audits and insurance premiums.
Check out more on our blog page now → AI, Tech, Cybersecurity