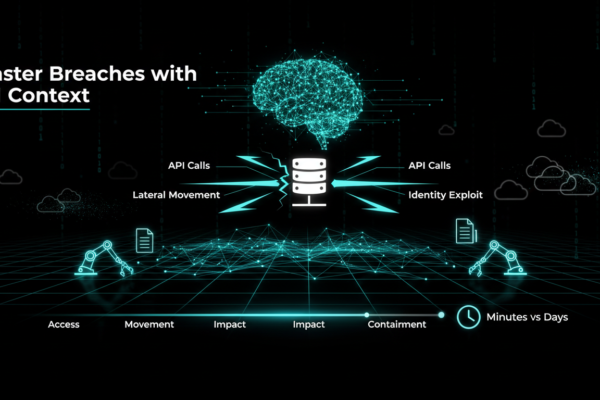
AI Powered Cloud Forensics for Faster Breaches
Discover how AI powered cloud forensics revolutionizes SOC teams, reconstructing breaches in minutes. Overcome traditional IR failures with context aware tools.Cloud attacks strike swiftly, outpacing traditional incident response teams. Unlike on premises setups where teams had days to collect disk images and review logs, cloud environments feature ephemeral infrastructure that vanishes in minutes, with rotating…