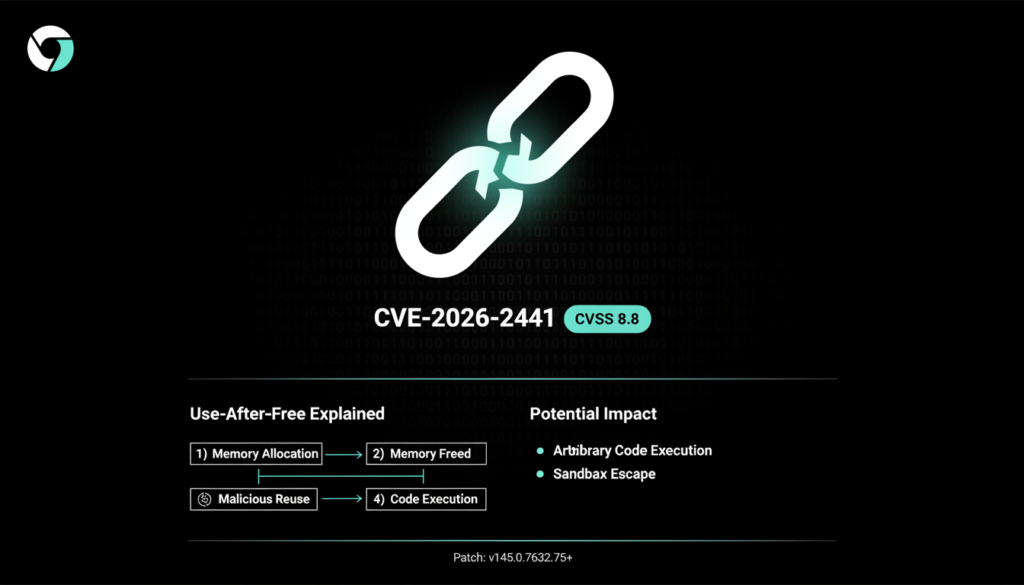
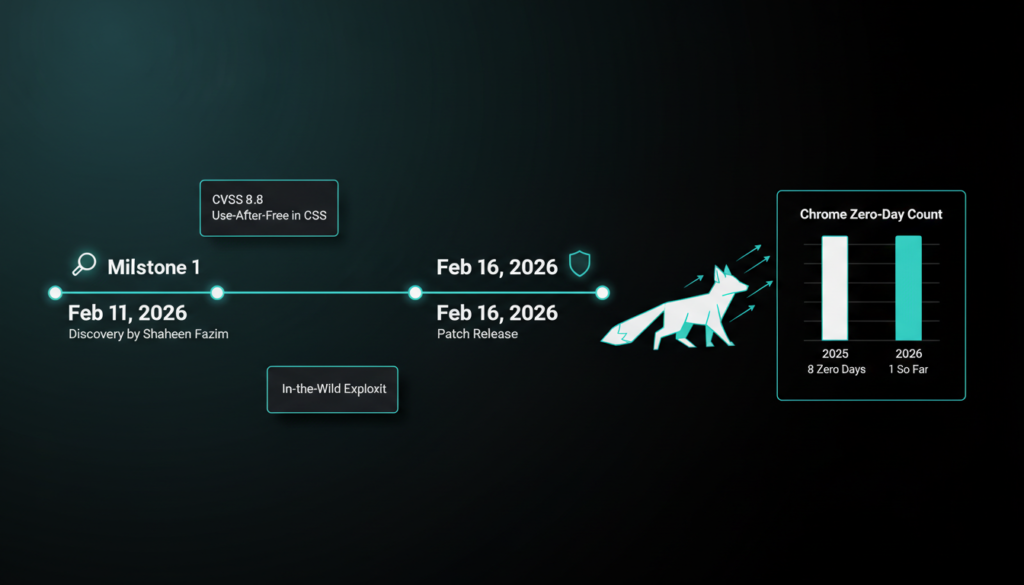
Google just dropped a critical security update for Chrome, tackling a zero day vulnerability that’s already being weaponized in realworld attacks. Tracked as CVE-2026-2441, this flaw has a CVSS score of 8.8, marking it high severity. Discovered by security researcher Shaheen Fazim on February 11, 2026, it’s a “use after free” bug in the browser’s CSS handling. In simple terms, this means attackers could craft malicious HTML pages to execute arbitrary code within Chrome’s sandbox, potentially bypassing protections and stealing data or installing malware.
What Makes This Zero Day So Dangerous?
Google confirmed an exploit for CVE-2026-2441 exists “in the wild,” but stayed tight lipped on specifics like attackers or targets. Use after free errors are notorious because they exploit memory management glitches programmers allocate memory for CSS objects, free it, but then accidentally reference it later, letting hackers inject code. According to NIST’s National Vulnerability Database, this affects Chrome versions before 145.0.7632.75, allowing remote attacks via booby trapped web pages. Browsers like Chrome process billions of web requests daily, making them prime targets; a single visit to a hacked site could compromise your device.
Historical data underscores the urgency. In 2025, Google patched eight Chrome zero days four actively exploited, per their security bulletin. This includes flaws like CVE-2025-2783 (another use after free) used in spyware campaigns. Security firms like Mandiant report that browser zero days spiked 30% in 2025, often tied to nation state actors targeting high value users in government and tech sectors. Early 2026 already mirrors this trend, with CVE-2026-2441 as the first confirmed Chrome exploit of the year.
Broader Browser Security Trends
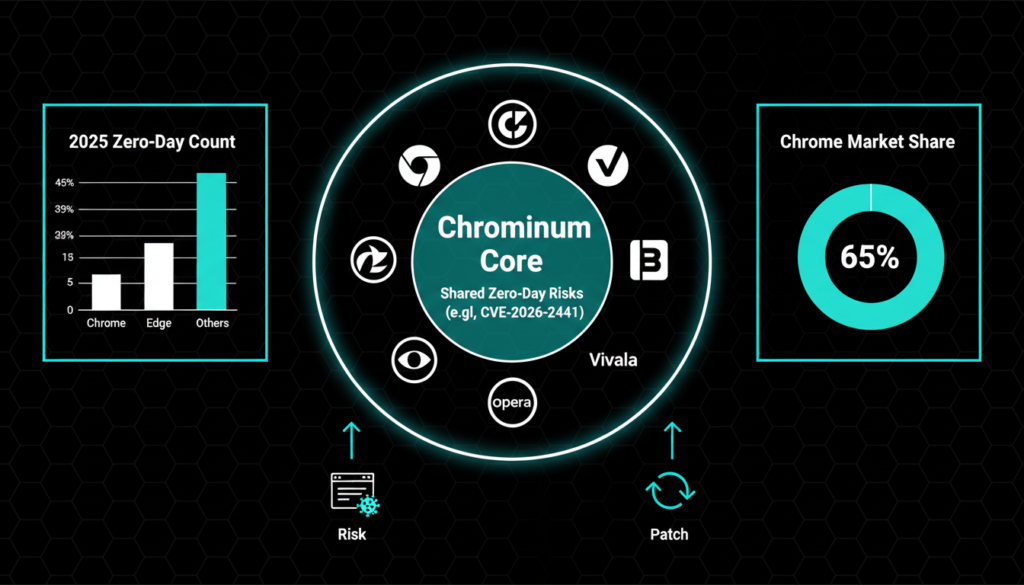
Chrome isn’t alone in the crosshairs. Last week, Apple rolled out patches for iOS, iPadOS, macOS Tahoe, tvOS, watchOS, and visionOS to fix CVE-2026-20700 (CVSS 7.8), a zero day enabling arbitrary code execution in sophisticated attacks on specific users pre-iOS 26. This wave of exploits highlights how browsers remain a vast attack surface: over 65% of global users run Chromium based browsers (Chrome, Edge, etc.), per StatCounter data from early 2026.
Why the focus on browsers? They’re everywhere desktops, mobiles, even embedded systems and handle untrusted web content. Attackers love them for “drive by downloads,” where no user interaction is needed beyond loading a page. Google’s Threat Analysis Group (TAG) noted in their 2025 report that state-sponsored groups exploited 10+ browser flaws for surveillance, often chaining zero days with social engineering. Chromium’s open source nature speeds fixes but also exposes code to scrutiny; forks like Brave and Vivaldi inherit the same risks until patched.
How to Patch and Stay Safe
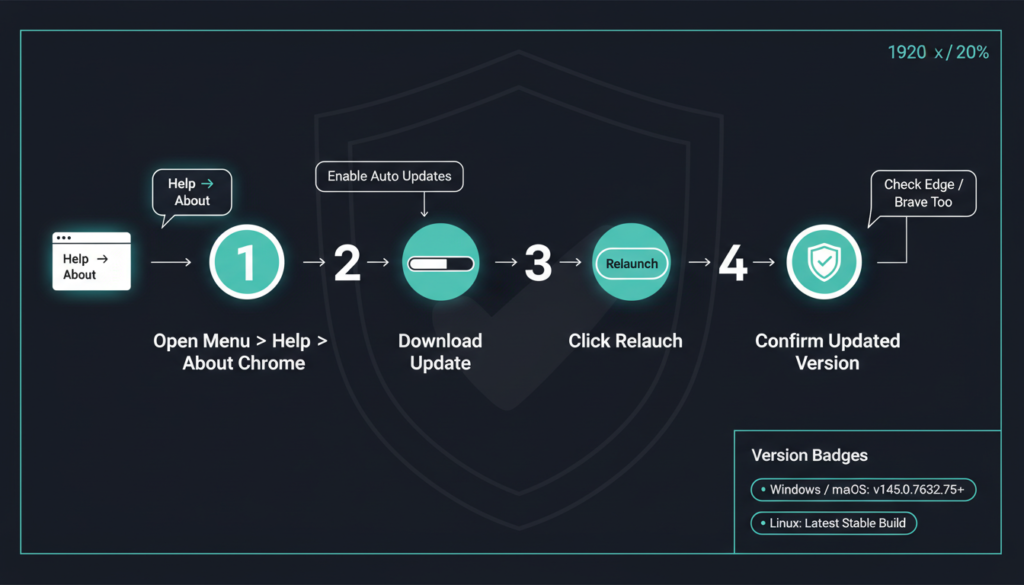
Act fast: Update Chrome to version 145.0.7632.75/.76 on Windows/macOS or 144.0.7559.75 on Linux. It’s simple head to the three dot menu, select Help > About Google Chrome, and hit Relaunch. The update auto-downloads if you’re online. Chromium users (Edge, Brave, Opera, Vivaldi) should check vendor sites for patches; Microsoft Edge, for instance, syncs closely with Chrome releases.
Beyond patching, harden your setup. Enable auto updates, use sandboxed profiles for risky browsing, and deploy endpoint detection tools like those from CrowdStrike or SentinelOne, which flag exploit attempts. Google’s Safe Browsing blocks known bad sites, but for zero days, it lags. Experts recommend hardware accelerated sandboxing and isolating browsers via VMs for high-risk work per CISA guidelines, this cuts exploit success by 70%.
Preventing Future Exploits
Zero days thrive on delayed patches, but proactive steps help. Google’s Project Zero has accelerated reporting Fazim’s quick disclosure exemplifies this. Broader defenses include memory safe languages like Rust, which Chrome is adopting for 20% more components in 2026, reducing use after free risks by design (per Google’s 2025 engineering blog). Users can contribute via bug bounties: this flaw earned Fazim up to $30,000. Track updates via Chrome’s stable channel blog for real-time alerts.
In summary, CVE-2026-2441 reminds us browsers are battlegrounds. With 2026 threats escalating projected 12+ zero days per Google’s TAG staying patched is non negotiable. Combine it with vigilance: avoid sketchy links, use VPNs on public Wi-Fi, and monitor tools like Have I Been Pwned for breaches.
Check out more on our blog page now → AI, Tech, Cybersecurity