A recent supply chain attack targeted the popular AI coding tool Cline CLI version 2.3.0, stealthily installing OpenClaw on thousands of developer machines worldwide. This breach underscores the escalating vulnerabilities in open source AI tools, where a single compromised npm publish token enabled attackers to slip in unauthorized software modifications during a narrow eight hour window. As AI agents become integral to development workflows, such incidents reveal how supply chain risks can cascade from package managers to production environments, affecting developers from Silicon Valley to India’s booming tech hubs like content creators optimizing AI driven blogs.
What is Cline CLI?
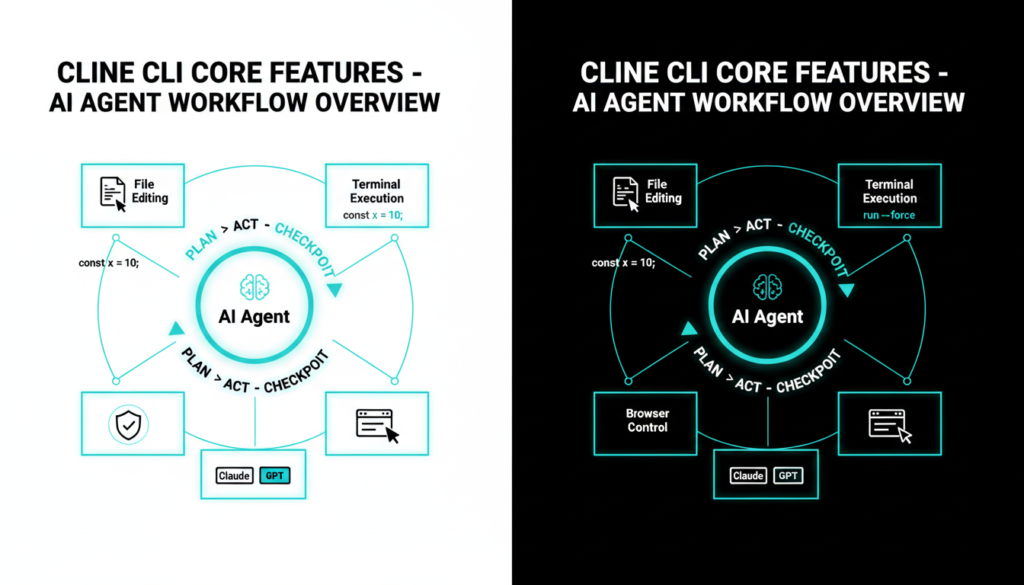
Cline CLI stands out as an open source, AI powered coding assistant that seamlessly integrates into IDEs like Visual Studio Code, empowering developers with autonomous capabilities such as multi file editing, terminal command execution, and headless browser debugging. It leverages advanced models like Claude or GPT, incorporating safety checkpoints, plan and act reasoning loops, and linter integration to streamline complex coding tasks, which has earned it around 90,000 weekly npm downloads among global developers. Popular for its gRPC based multi instance support and CI/CD automation, Cline reduces manual toil in web development and scripting, but its extensive system-level access to files, shells, and browsers makes ita high value target when breached.
This tool’s rise aligns with the broader shift toward agentic AI in coding, where tools like Cline handle not just code generation but full project orchestration, making developers more productive yet exposing them to amplified risks if core packages are tampered with.
The Attack Unfolds
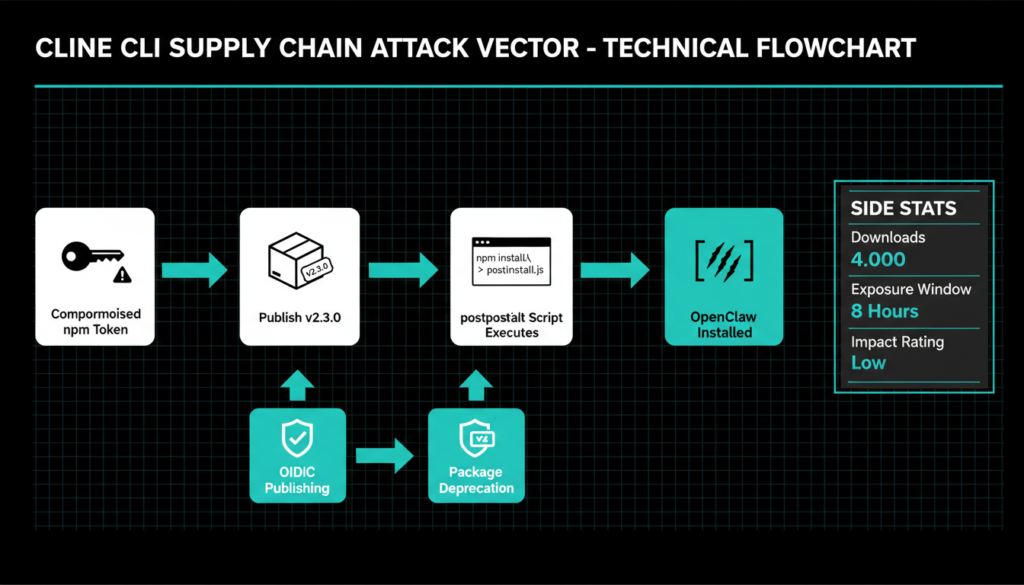
The incident unfolded on February 17, 2026, at 3:26 AM PT, when attackers exploited a stolen npm publish token to deploy Cline CLI 2.3.0, embedding a rogue postinstall script: “npm install -g openclaw@latest”. This script executed silently upon installation, globally deploying OpenClaw without consent, impacting roughly 4,000 downloads over the next eight hours as flagged by Microsoft Threat Intelligence’s observed spike in OpenClaw activity. No direct payload execution followed, but the forced install bypassed user awareness, potentially paving ways for future exploits given OpenClaw’s own powerful features.
Cline maintainers acted swiftly: deprecating 2.3.0 by 11:30 AM PT, rolling out secure version 2.4.0, revoking the token, and migrating to OpenID Connect (OIDC) authentication via GitHub Actions to prevent token reuse. Importantly, the attack spared Cline’s VS Code extension and JetBrains plugins, limiting fallout to CLI users only.
Attack Impact
Endor Labs assessed the overall threat as low since OpenClaw deploys without its gateway daemon or malicious intent, yet it exposed critical gaps in package attestation and trusted publishing. Developers faced unauthorized software bloat, potential privacy leaks from OpenClaw’s file/shell access, and a wake-up call on postinstall script dangers in high download packages. In India’s dev community, where npm underpins countless startups and freelance projects, this hit close echoing needs for vigilant dependency hygiene amid rising AI tool adoption.
Immediate steps include updating to 2.4.0+, scanning systems for rogue OpenClaw instances with npm list g, and purging unused instances to reclaim disk space and reduce attack surface.
What is OpenClaw?
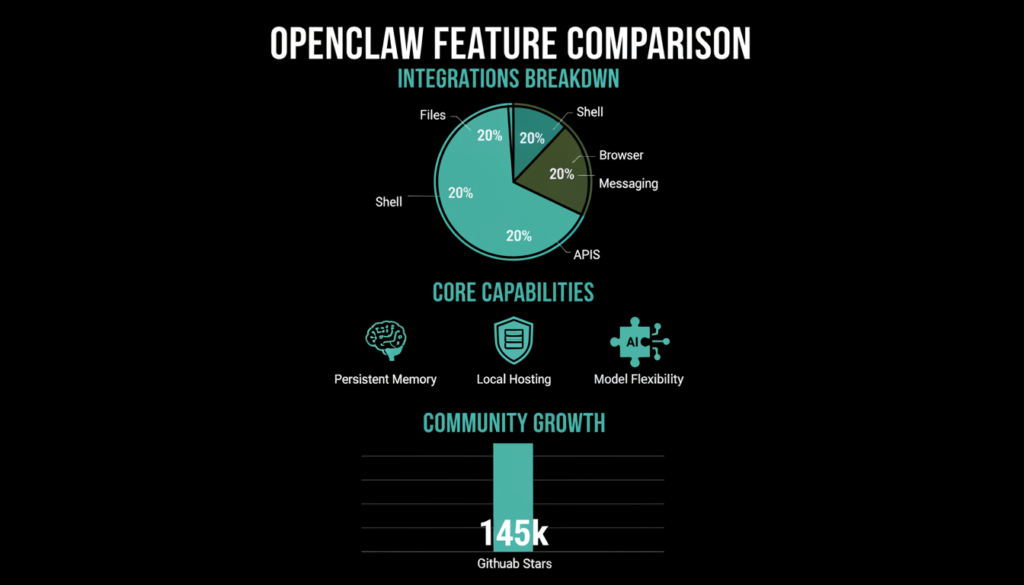
OpenClaw represents a self hosted, open-source AI agent framework that harnesses LLMs like Claude or GPT for practical autonomy: manipulating files, executing shell commands, controlling browsers, and hooking into Telegram, Discord, Slack, or custom APIs. Evolving from Clawdbot and Moltbot, it boasts persistent memory for contextual continuity, modular AgentSkills for extensions, and local/VPS deployment, sidestepping cloud costs beyond LLM API fees. Its meteoric 145,000+ GitHub stars stem from privacy-first design, model flexibility, and grassroots hype in Silicon Valley dev circles and China’s AI scene, positioning it as a go to for personal automation.
Though benign by nature, OpenClaw’s god-like local privileges make unsolicited installs a red flag, as adversaries could later abuse it for persistence or data exfiltration in targeted ops.
Clinejection: The Backdoor
Weeks before the npm hit, security researcher Adnan Khan unveiled “Clinejection,” a prompt injection vulnerability in Cline’s GitHub issue triage automation, where AI (Claude) auto-responds to new issues with repo access and broad tools. Malicious issue titles could jailbreak the AI for arbitrary code execution on the default branch, a misconfig granting undue powers meant for triage efficiency.
This fed into sophisticated cache poisoning: attackers bloated GitHub Actions cache past 10GB to trigger LRU evictions, seeding tainted entries keyed to nightly release workflows, ultimately snagging NPM_TOKEN for the 2.3.0 publish. Named after PromptPwnd-style flaws, Clinejection morphed a low-priv GitHub action into supply chain dominance, fixed post-disclosure but spotlighting AI agents’ “privileged actor” status.
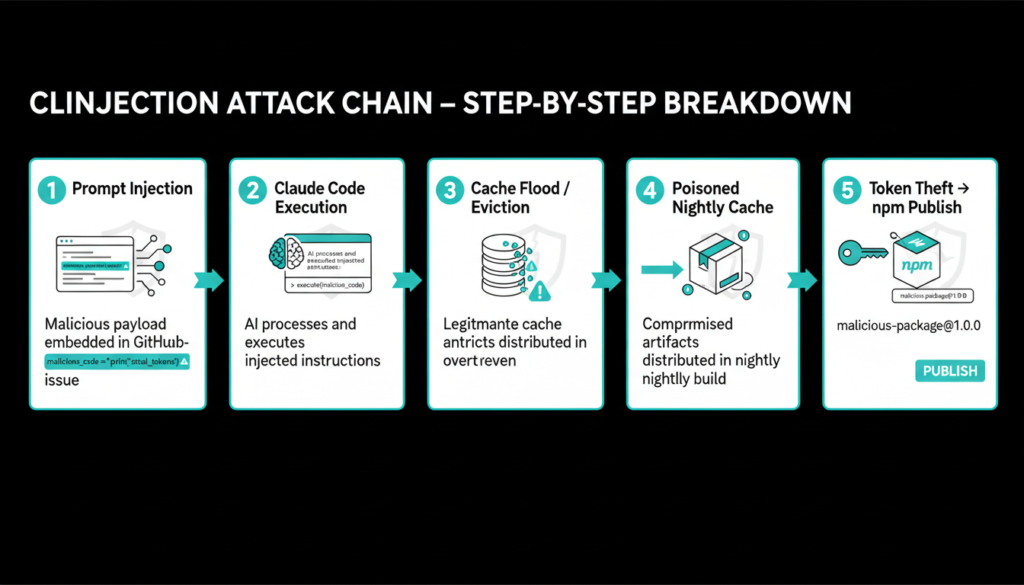
How Cache Poisoning Works
By overwhelming caches, attackers force evictions then inject payloads matching privileged jobs like Publish NPM Nightly, executing code to exfiltrate secrets turning public issues into credential heists. This technique, detailed in Cacheract research, thrives on GitHub’s shared caching, demanding scoped tokens and cache pinning as defenses.
Broader AI Supply Chain Risks
NPM supply chain assaults ballooned 156% in 2025, imperiling billions of downloads; AI tools like Cline supercharge this via embedded agents and LLM dependencies. High profile cases include NullBulge ransomware on Hugging Face/GitHub AI repos and Wondershare’s credential leaks enabling model poisoning, mirroring Cline’s token theft.
AI coding assistants grapple with prompt injections via code comments, MCP server hijacks, and vibe coding risks where LLMs ingest tainted inputs, leaking data or inserting backdoors. Cline’s 90k weekly pulls make it emblematic of npm’s soft underbelly, where postinstall hooks evade scans Palo Alto notes billions affected yearly.
For content creators blending AI into SEO optimized blogs or resin art tutorials, vetting dev tools prevents workflow disruptions from such chains.
How to Protect Yourself
Prioritize updates: npm update cline –global, then hunt OpenClaw with npm list -g | grep openclaw and npm uninstall -g openclaw. Leverage Socket, StepSecurity, or Endor Labs for SCA scans flagging rogue scripts; enforce OIDC/Sigstore for signed provenance over tokens.
For AI workflows, sandbox agents with minimal perms, input sanitization against injections, SBOM generation via tools like Syft, and runtime monitoring treat them like root services. Indian developers scripting video edits or blog automation should layer npm audit, Dependabot alerts, and lockfiles.
Ecosystem shifts demand disabling legacy tokens, attestation vigilance, and prevention tools like GitHub Advanced Security, fortifying against AI amplified threats in 2026’s agent economy.
Check out more on our blog page now → AI, Tech, Cybersecurity