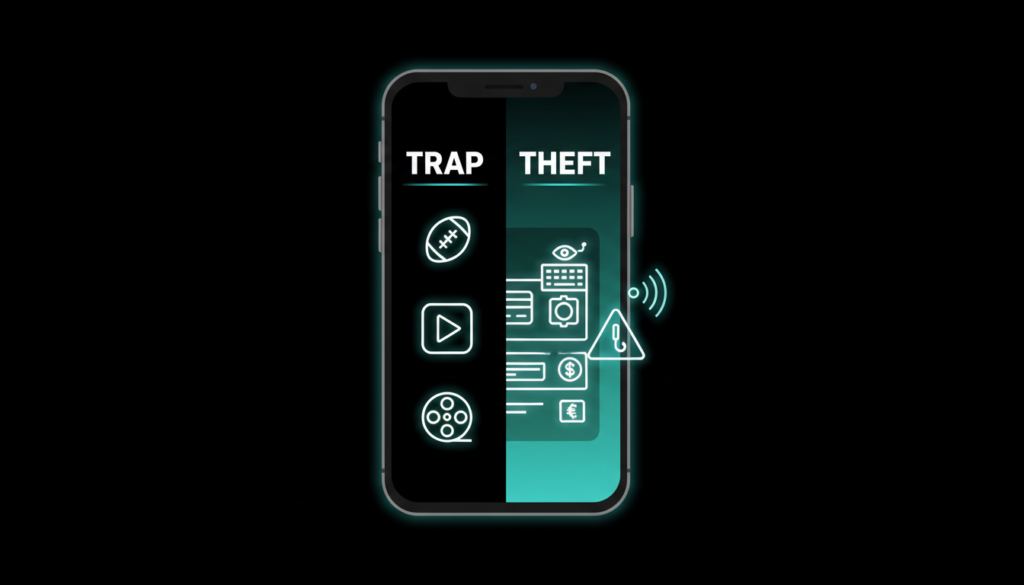
Cybersecurity experts have uncovered a sneaky new Android malware called Massiv, lurking inside fake IPTV apps that promise free streaming TV. This trojan targets mobile banking users, enabling full device hijacking for theft through advanced remote control tactics.
Massiv’s Core Threats
Massiv excels at device takeover (DTO) attacks, letting hackers remotely operate infected phones for fraudulent bank transactions. Dutch firm ThreatFabric first detected it in Portugal and Greece campaigns this year, with test versions from early 2025. Though currently limited, its banking focus makes it highly dangerous.
It deceives users seeking online TV by mimicking harmless apps. Key tactics include screen streaming via Android’s MediaProjection API, keystroke logging, SMS snatching, and phony overlays that mimic banking logins to harvest credentials and card info.
Attacks on Official Apps
Massiv zeroes in on Portugal’s gov.pt app for ID storage and Digital Mobile Key (CMD). Fake prompts trick users into entering phone numbers and PINs, evading KYC to fraudulently open bank accounts for laundering or unauthorized loans.
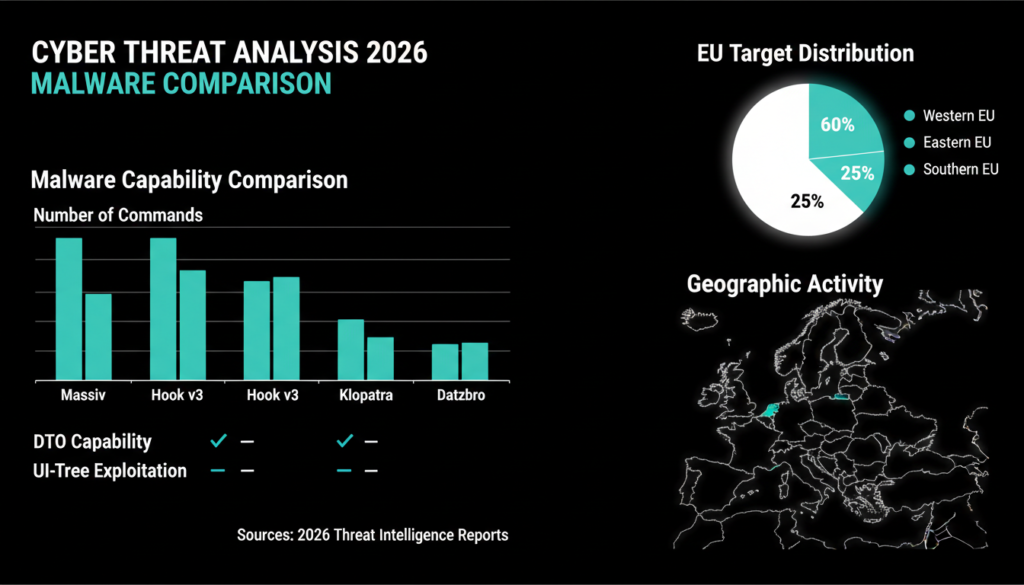
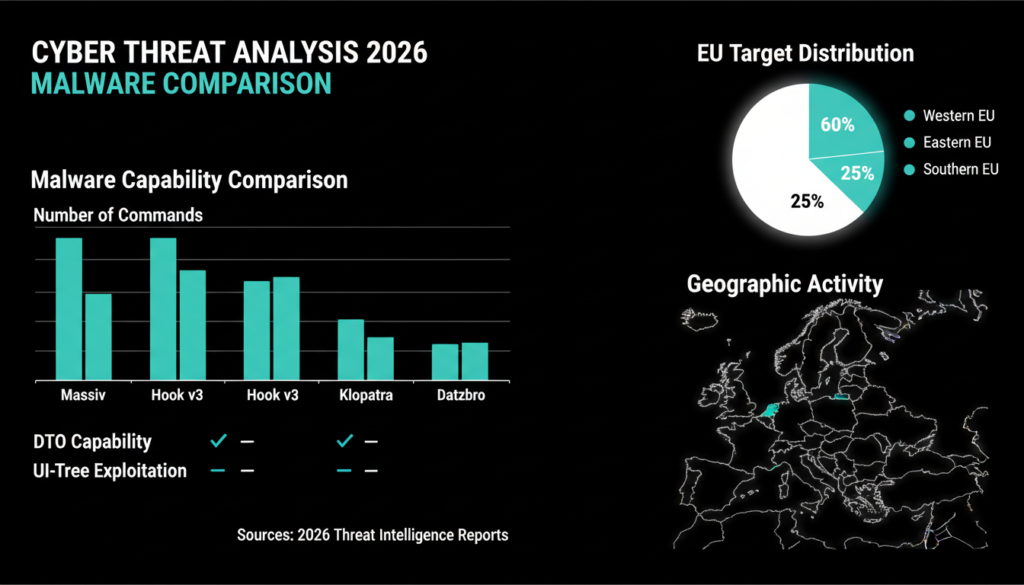
Similar to trojans like Crocodilus, Datzbro, and Klopatra, it abuses accessibility services for stealth. Attackers overlay a black screen, mute device sounds, and hide while controlling the phone.
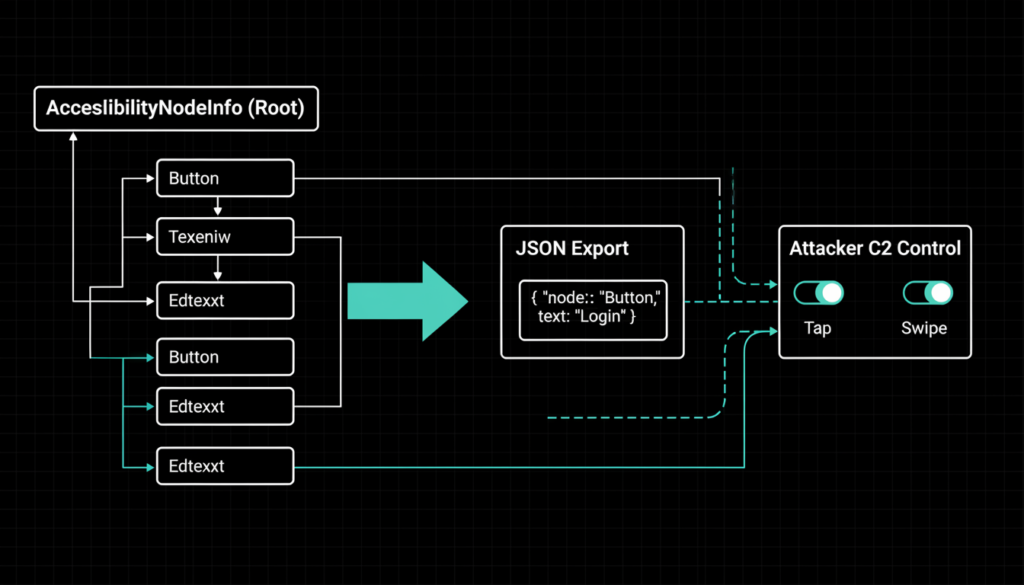
To dodge screen capture blocks in secure apps, Massiv uses “UI-tree mode.” It maps the interface via AccessibilityWindowInfo, creating JSON of texts, coordinates, buttons, and states only sending visible elements for precise remote clicks.
Full Malware Capabilities
Massiv’s toolkit is extensive, supporting over 20 commands for total domination:
- Black screen overlay with sound/vibration mute
- Device info dump (model, apps, location)
- Clicks, swipes, pattern unlocks
- Clipboard hijacking for phishing text
- Screen streaming toggle
- Custom overlays for apps, PINs, locks
- APK downloads/installs from C2
- Opens battery optimization, admin, Play Protect screens
- SMS access, log wiping
Kaspersky’s 2025 reports note banking trojans like this evolved with 25% more features, fueling 1.5 million global DTO incidents last year Europe hardest hit.

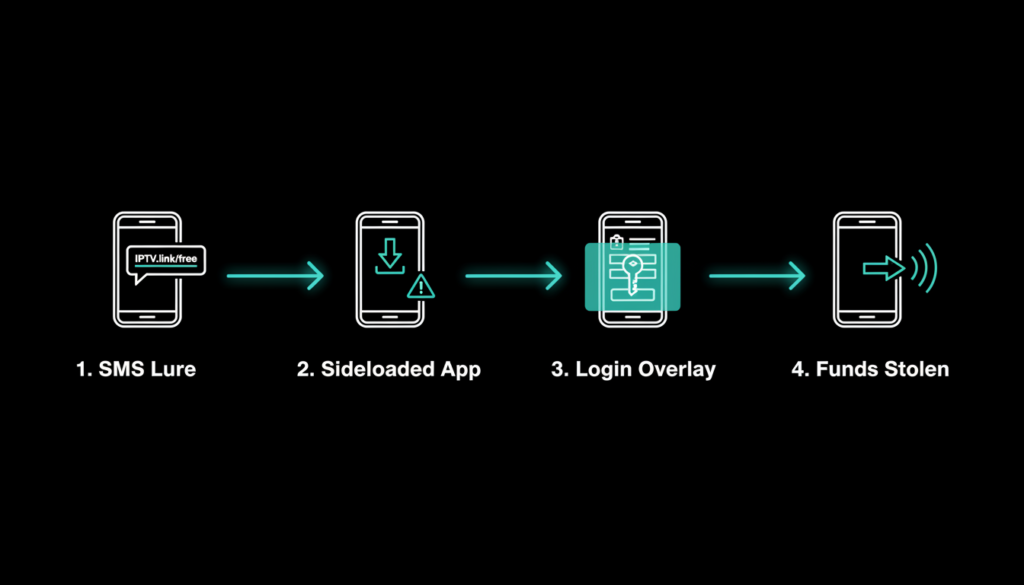
Distribution Tactics
Spread via SMS phishing as droppers like IPTV24 (hfgx.mqfy.fejku) or fake Google Play (hobfjp.anrxf.cucm), it requests external install permissions under “update” guise. No real IPTV just a WebView smokescreen while malware runs.
Campaigns spike in Spain, Portugal, France, Turkey 40% of recent TV droppers per Zimperium Q4 2025. In India, CERT-In logged 30% rise in sideloaded streaming malware via WhatsApp, tying to UPI fraud amid 16 billion monthly transactions.
Google’s bulletins flag MediaProjection abuse in 18% of 2025 trojans; side-loading risks 75% of Indian Android devices.
Emerging Trends and Comparisons
Massiv hints at Malware as a Service (MaaS) with API keys for C2 comms and active code updates. SentinelOne sees prototypes adding AI overlays; Hook v3 (Zimperium) mirrors with 107 commands, ransomware fakes, NFC skimmers, GitHub spreads.
Android’s 72% global share (StatCounter 2026) draws crowds ENISA reports 350% EU DTO surge since 2024. IPTV bait hooks 20-40 age group; in Maharashtra, resin art creators like you juggle crafts with UPI banking, heightening sideloading temptations from “free tool” lures.
Related threats: Hook’s transparent gestures, Klopatra’s SMS floods. BleepingComputer notes Massiv’s UI-tree beats banking capture blocks better than predecessors.
India-Specific Risks and Stats
For Ratnagiri users, local UPI boom (RBI: 18B txns Jan 2026) meets rising fakes CERT-In’s Feb 2026 alert flags 28% Android malware jump, many IPTV/OTT disguised. Maharashtra phishing SMS doubled YoY, per NCRB cybercrime data.
Your blogging on AI/cybersecurity aligns perfectly similar to FluBot waves, Massiv could hit video tutorial seekers with “free editing apps.”
Advanced Prevention Strategies
Beat Massiv proactively:
- Google Play only enable Play Protect auto-scans.
- Deny unknown sideloading; use ADB for crafts/tools.
- Audit accessibility services weekly no strangers.
- Banking apps: biometrics, transaction alerts, app locks.
- Tools: Malwarebytes, Bitdefender scans; Android 15 Private Space.
- SMS filter unknowns; verify IPTV via official stores.
ENISA urges VPNs for public WiFi; Kaspersky adds NFC disable for skims. For creators, isolate work profiles.
Post-install flags: Battery drain, pop-ups, odd permissions nuke and restore
Future Outlook
Massiv’s polish signals MaaS boom expect geo spreads, AI evasion. Android 16 rumors: hardened APIs. Stay ahead: follow ThreatFabric, CERT In alerts.
Check out more on our blog page now → AI, Tech, Cybersecurity