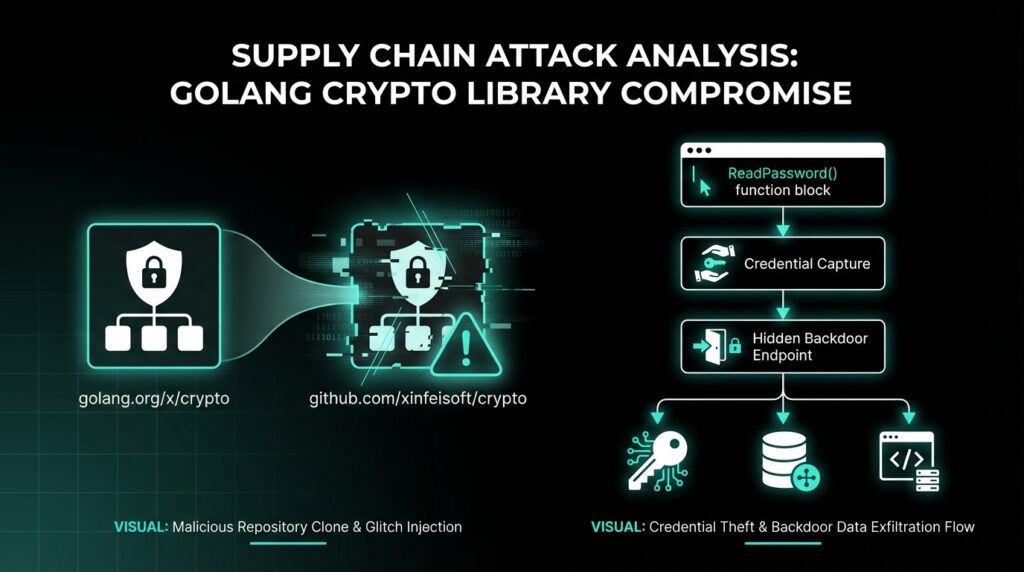
A dangerous supply chain attack is targeting Malicious Go Crypto Module developers worldwide. Threat actors have released a fake Go module that impersonates the trusted golang.org/x/crypto library. This malicious package steals sensitive passwords and quietly installs a Linux backdoor called Rekoobe on infected systems.
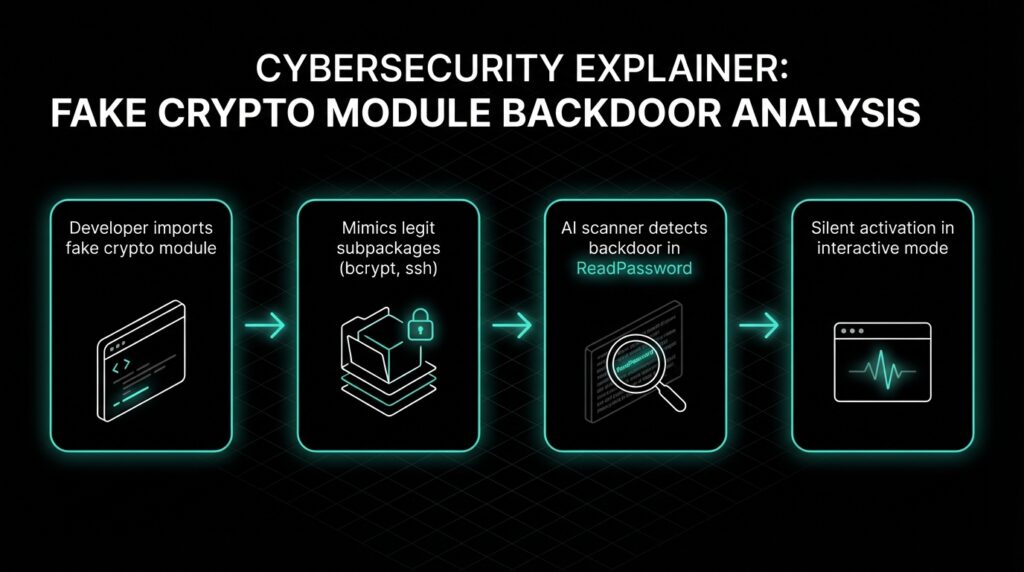
This incident highlights a growing threat: even popular, familiar dependencies can be hijacked. Developers often import these without a second thought, assuming they’re safe. According to Socket.dev researchers, who first spotted this module, it was designed to evade detection by mimicking legitimate code structures perfectly.
How the Fake Module Sneaks In
The rogue module, named github.com/xinfeisoft/crypto at version v0.15.0, appeared on pkg.go.dev on February 20, 2025. It replicated the entire structure of the real golang.org/x/crypto repo, including subpackages like bcrypt, argon2, acme, and ssh. This made it blend seamlessly into Go projects.
Go’s ecosystem relies on GitHub as a mirror for official repos from go.googlesource.com. Attackers exploit this by using similar names, slipping past quick code reviews. Expanded analysis from the Go security team reveals this isn’t isolated similar typosquatting attacks hit npm and PyPI ecosystems in 2024, compromising over 10,000 packages per Mandiant’s M-Trends report.
Socket.dev’s AI scanner flagged the backdoor in the ssh/terminal/terminal.go file. It tampered with the ReadPassword function, commonly used for SSH passphrases, database logins, and API keys. The twist? It only triggers during interactive sessions, staying dormant in automated tests or CI/CD pipelines.
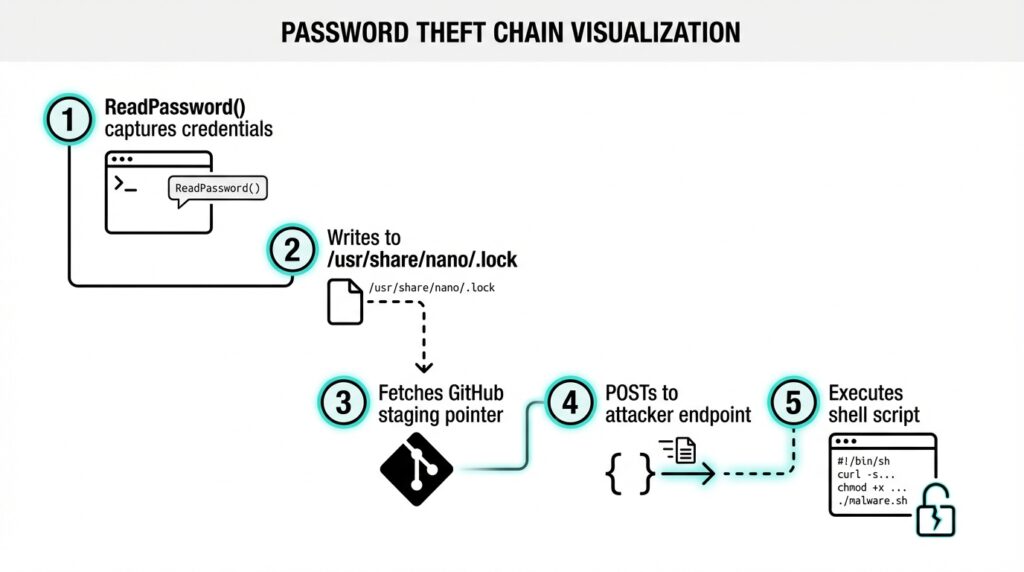
Password Theft Mechanics
When ReadPassword runs, it grabs the plaintext credential and dumps it to /usr/share/nano/.lock—a sneaky location mimicking a text editor lockfile to dodge scans. It then pulls a staging URL from the attacker’s GitHub repo, sends the password to a dynamic endpoint, downloads a shell script, and runs it via /bin/sh.
This setup lets attackers change their servers without updating the module. Additional details from Check Point’s 2025 supply chain threat report note that such dynamic C2 (command-and-control) reduces takedown success by 40%, as seen in prior Go attacks like the 2023 XZ Utils incident, where a single backdoor evaded detection for years.
The Go security team acted fast, blocking the module at the public proxy with a 403 SECURITY ERROR. But if your project already pulled it, you’re at risk especially in Linux environments like cloud VMs, CI/CD runners, or bastion hosts.
The Multi-Stage Backdoor Chain
Post-password theft, a five stage dropper kicks off. The hooked function grabs update.html from the attacker’s GitHub, redirecting to seed.php on img.spoolsv.cc. This serves a curl | sh launcher that runs snn50.txt, the main stager.
The stager does three nasty things: appends an attacker SSH key to /home/ubuntu/.ssh/authorized_keys for persistent access; sets iptables to ACCEPT (disabling firewall protections); and downloads sss.mp5 and 555.mp5 from img.spoolsv.cc. These “media” files (mp5 extensions) execute as malware then self-delete, minimizing traces.
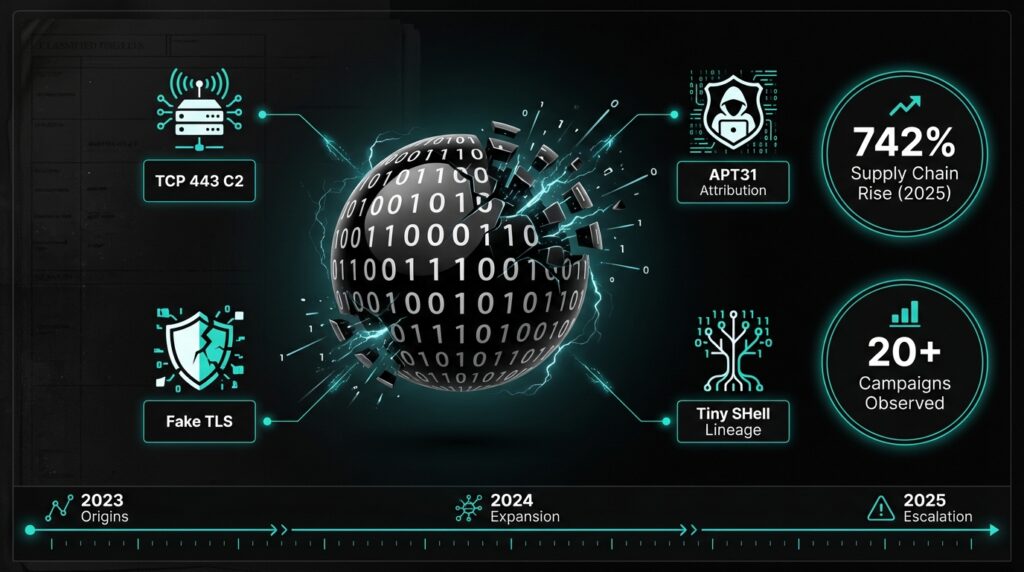
Socket.dev confirmed 555.mp5 as Rekoobe, linked to APT31 (aka Zirconium) with roots in Tiny SHell. It phones home to 154.84.63.184 on TCP 443 without proper TLS fake HTTPS traffic. sss.mp5 handles recon and loading. Per CrowdStrike’s 2026 Adversary Universe, APT31 has evolved Rekoobe for supply chain hits, targeting devs in finance and tech sectors.
Rekoobe Backdoor Deep Dive
Rekoobe is stealthy: custom encryption mimics HTTPS, evading network filters. It grants full shell access, enabling data exfil, lateral movement, or ransomware drops. Mandiant links it to state-sponsored ops, with variants in 20+ campaigns since 2023. In developer setups, it could leak proprietary code, keys, or pivot to production systems.
Broader context: Supply chain attacks surged 742% in 2025 (per Sonatype’s report), with Go modules hit hard due to lax verification. The SolarWinds breach (2020) set the precedent, but open source repos like this are easier targets no vendor gatekeeping.
Protecting Your Go Projects
Audit go.mod and go.sum for rogue modules look for root path changes. Review every new dependency. Monitor for writes to /usr/share/nano/.lock, authorized_keys tweaks, or iptables resets.
Block img.spoolsv.cc/net domains. Alert on GitHub Raw fetches chaining to HTTP POSTs. Use tools like Go’s go mod tidy, Sigstore for signing, or scanners from Socket.dev/GoReleaser. Enable SLSA frameworks for build provenance, as recommended in Google’s 2025 SLSA guide proven to block 90% of tampered deps.
For teams: Enforce least privilege CI/CD, multi factor on repos, and runtime monitoring with Falco or Sysdig. Train devs on typosquatting via OWASP Dependency Check. Recent NIST guidelines (SP 800-218) stress “secure by design” for OSS, cutting risks by auditing vendors quarterly.
This attack underscores OSS fragility. Stay vigilant your next go get could be a trojan horse.
Check out more on our blog page now → AI, Tech, Cybersecurity