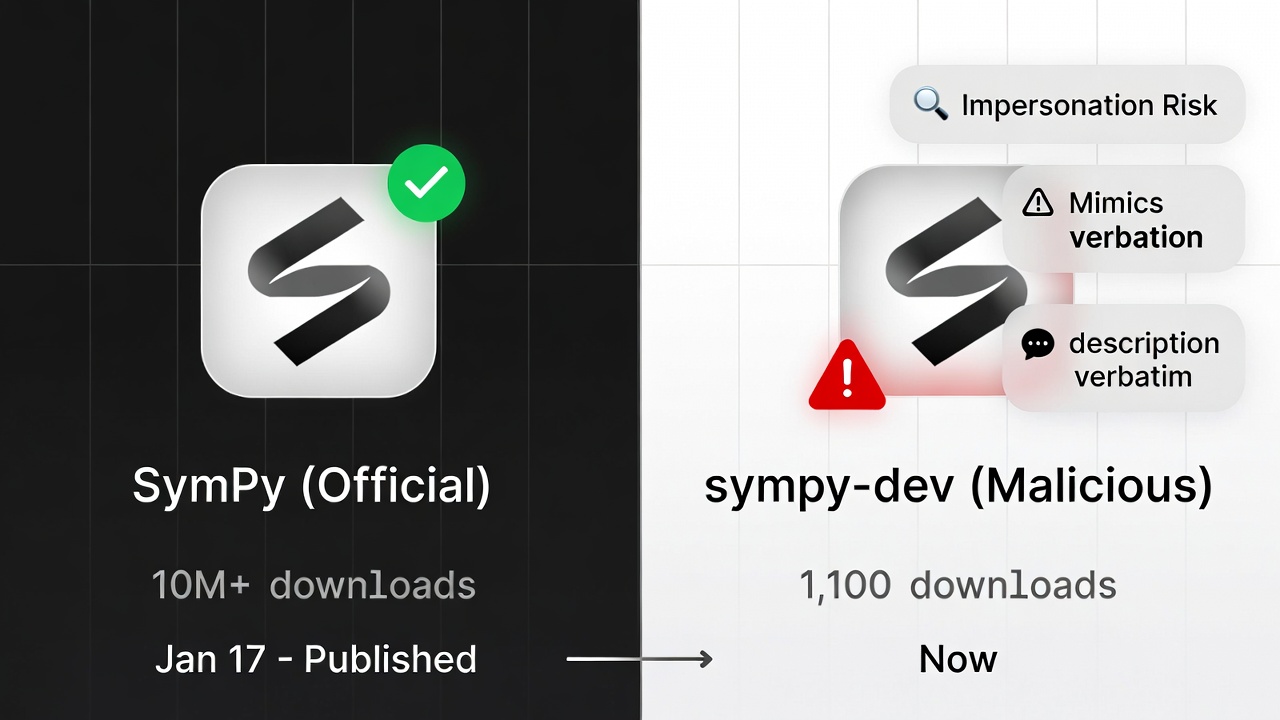
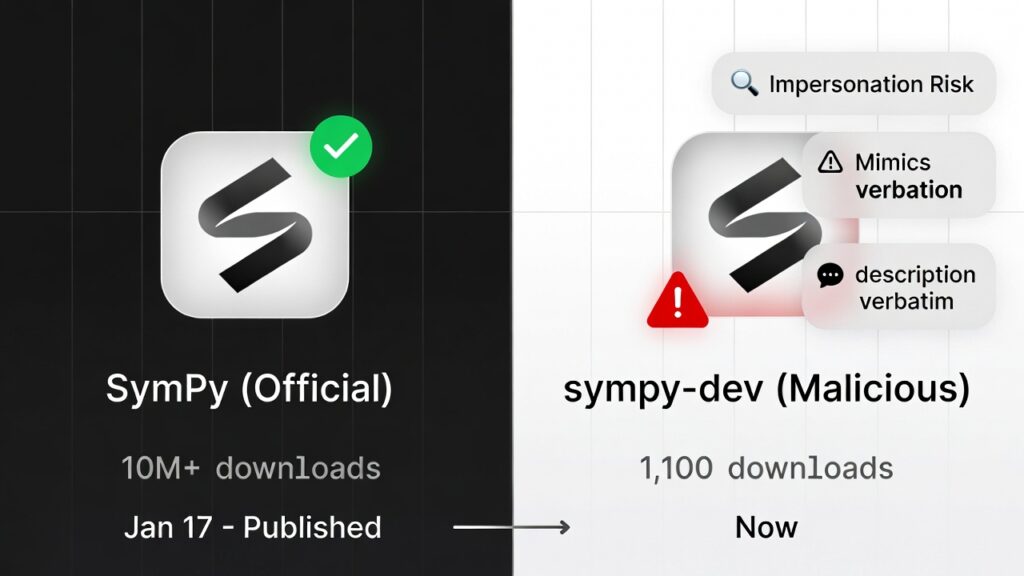
A freshly discovered strongmalicious PyPI package strong is impersonating SymPy, the go-to library for symbolic math in Python. This sneaky upload deceives developers into installing it, unleashing an XMRig cryptocurrency miner on Linux machines. Dubbed sympy dev and uploaded January 17, 2026, it has snagged over 1,100 downloads in days. Such strong malicious PyPI tactics exploit trust in repositories, turning routine pip installs into hidden threats
Download tallies aren’t foolproof infection metrics, but they flag potential victims among hasty coders eyeing a supposed “dev” build. The strong, malicious PyPI package strongly mirrors SymPy’s description exactly, boosting its credibility. It lingers online, underscoring PyPI’s scale over 500,000 packages strong, yet ripe for abuse. In 2025, security firms like Checkmarx flagged 1,200+ strong malicious PyPI entries, a 40% yearly spike.
Unpacking the Malicious Payload Mechanics
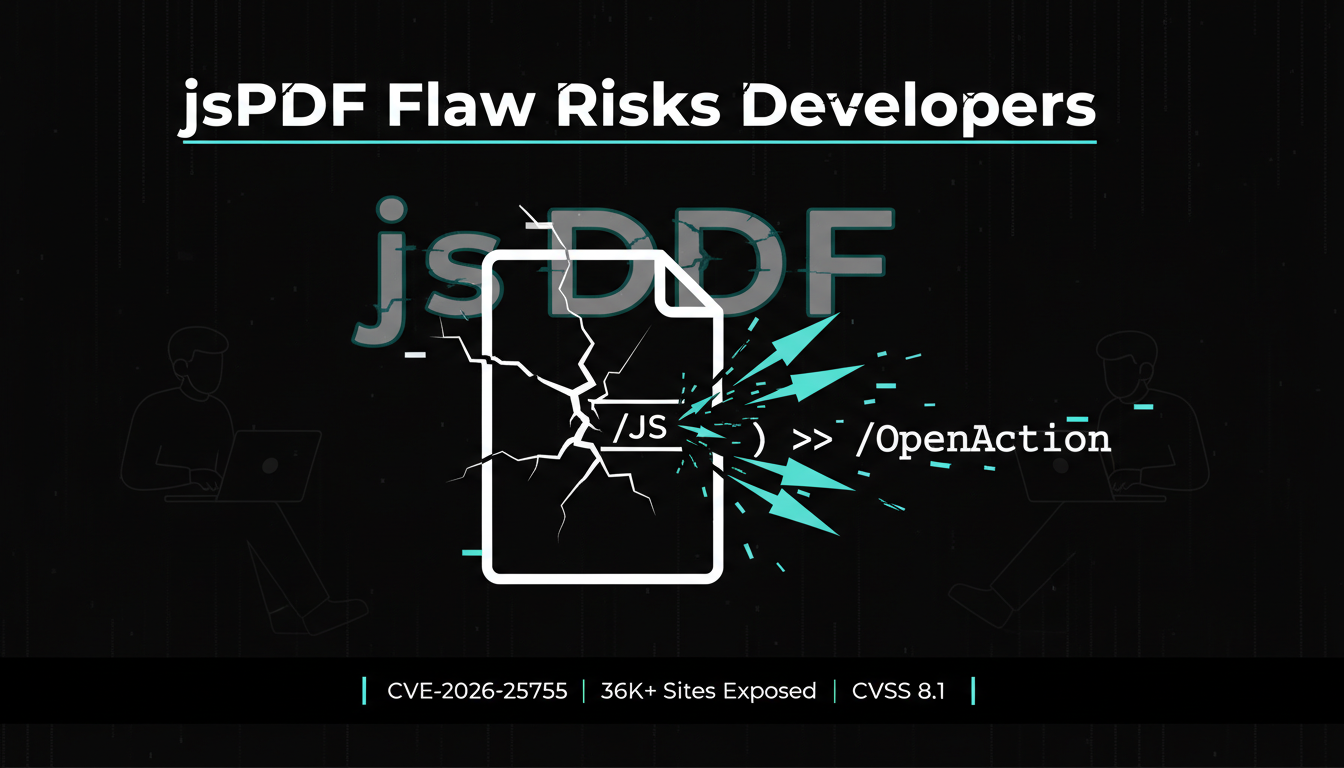
This strong malicious PyPI package strong embeds malware in SymPy’s polynomial functions, activating only on specific calls. This conditional trigger lets it masquerade as legit code, dodging antivirus and sandboxesa hallmark of sophisticated strong malicious PyPIstrong campaigns. Once tripped, it fetches a JSON config from attacker IP 63.250.56.54, grabs an ELF binary, and executes it in memory via Linux’s memfd_create and /proc/self/fd, erasing disk footprints.
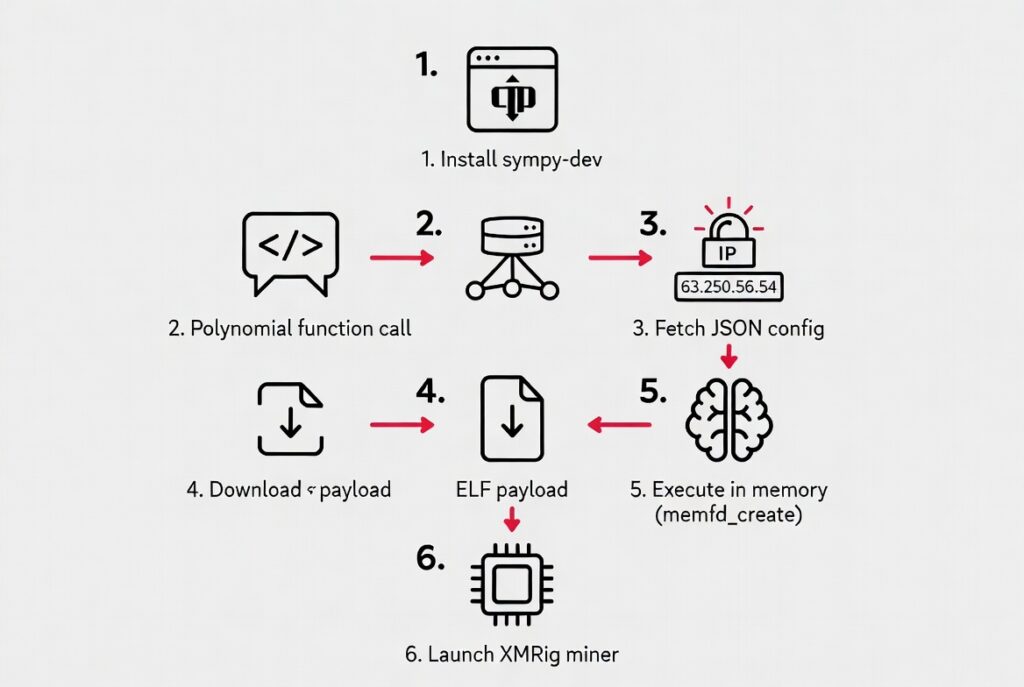
Socket researcher Kirill Boychenko dissected it: the loader stage downloads two ELF miners configured for XMRig. They prioritize CPU mining, disable GPUs, and tunnel via Stratum TLS on port 3333 to the attacker’s servers. More alarmingly, this strong malicious PyPI package strong serves as a universal dropper able to inject any payload under Python’s user privileges. Echoes of FritzFrog (2024 Log4Shell exploits) and Mimo (2025 Magento hits) show evolving strong malicious PyPI strong patterns
Cryptojacking via XMRig thrives on Monero’s untraceability. Attackers hijack server CPUs silently, inflating cloud bills by 20-50% undetected. On Linux, where 70% of servers run, this strong malicious PyPI package strong could persist for months, evading tools without behavioral monitoring.
Rising Tide of Malicious PyPI Threats
PyPI’s openness fuels innovation but invites strong malicious PyPI packages strong. Typosquatting sympy-dev vs. SymPy is rampant; Sonatype’s 2025 report tallied 2,500 cases, up 60%. The 2024 XZ Utils near backdoor, which infiltrated Linux distros via a trusted maintainer, proves nation state actors eye these repos. strong Malicious PyPI strong uploads often blend legit code with loaders, as in the 2023 requests pypi scam hitting 100,000 devs.
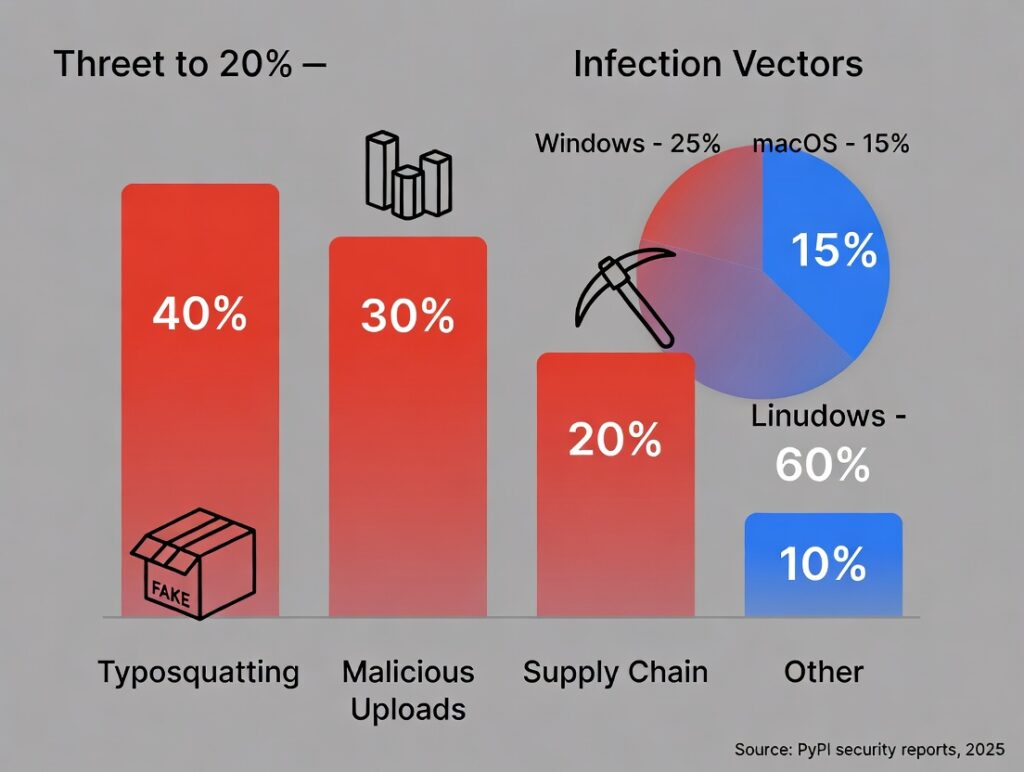
Broader stats: 15% of PyPI packages harbor risks per Safety CLI scans. strong Malicious PyPI packages strong like this one amplify supply chain woes, akin to SolarWinds or Log4j. Devs face pressure from deadlines, skipping verifications yet one slip compromises entire pipelines.
Shielding Against Malicious PyPI Packages
Combat these with proactive defenses:
- Scrutinize packages—review stats, activity, maintainers.
- Scan with pip-audit, Safety CLI, or Socket.dev.
- Lock PyPI accounts with 2FA; favor verified publishers
- Containerize code to quarantine malicious effects.
- Watch for CPU spikes or odd outbound traffic.
For enterprises, adopt SBOMs via CycloneDX or SPDX to map risks. Tools like Sigstore verify package signatures. If hit by a strong malicious PyPI package strong, kill processes (pkill -f xmr), hunt ELFs with Volatility, and notify security@python.org. Python’s PSF now enforces stricter uniqueness checks, but user habits drive real security.
This malicious PyPI package saga reminds us: pip’s convenience hides perils. Vet every install, monitor relentlessly, and report suspicious activity. In an era of rampant malicious PyPI threats, vigilance turns potential disasters into footnotes
Key Takeaways: Shield Against Malicious PyPI Threats
In summary, the sympy dev malicious package exemplifies the dangers lurking on PyPI impersonating SymPy to stealthily deploy an XMRig miner on Linux via memfd_create and in-memory execution. With over 1,100 downloads since January 17, 2026, it highlights typosquatting and supply chain vulnerabilities that have surged, with 1,000+ malicious uploads last year alone.
Core risks include hidden polynomial triggers, ELF payloads from suspicious IPs like 63.250.56.54, and versatile loaders beyond just cryptojacking. But you can fight back: verify packages rigorously, scan dependencies with tools like pip audit, enforce 2FA, containerize environments, and monitor for anomalies.
Adopting SBOMs and trusted publishers fortifies your workflow. Stay vigilant, report suspicious packages to PyPI, update habits, and turn potential disasters into secure codebases. Your next pip install could be a malicious trap; make security your default.
Stay ahead of evolving threats like this malicious PyPI attack. Dive into our other blogs on AI, TECH, and CYBERSECURITY. covering everything from machine learning breakthroughs to cutting-edge defenses. Visit our page now for expert analysis and actionable tips!