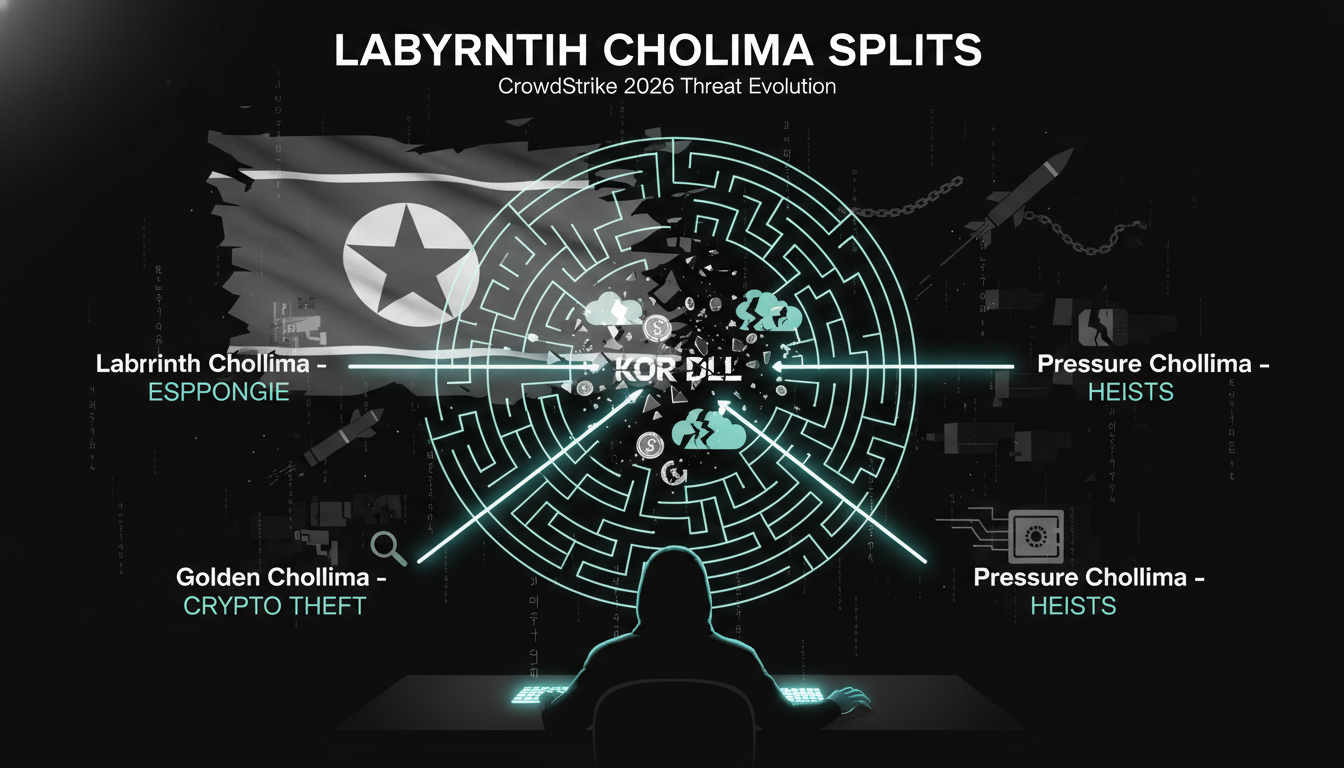
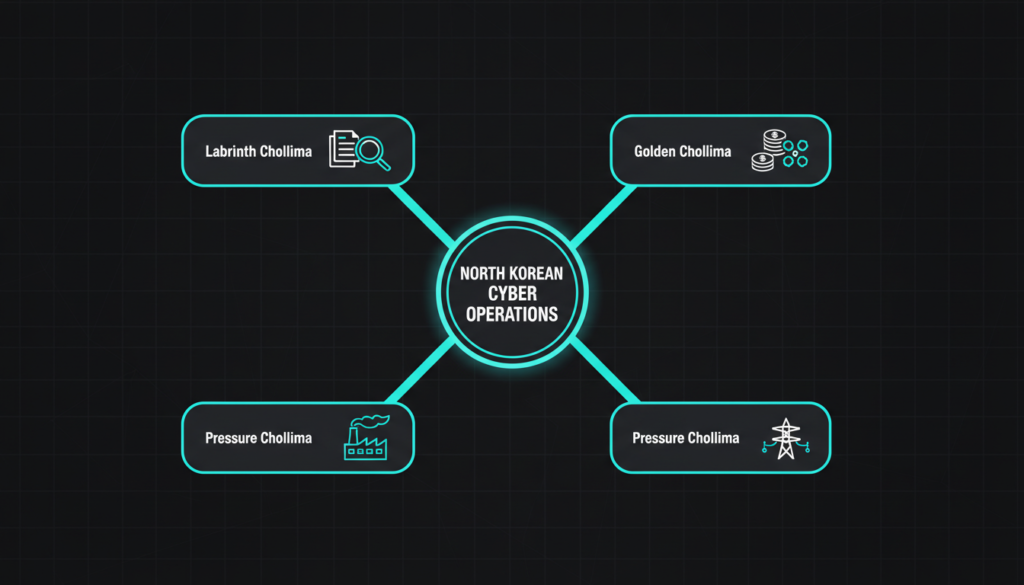
North Korea’s Labyrinth Chollima, one of the regime’s most active cyber threat actors, has recently been reclassified by researchers into three distinct but related hacking groups. This restructuring, identified by cybersecurity firm CrowdStrike, shows how North Korea is professionalizing and specializing its offensive cyber operations. What was once tracked under a single name is now separated into Labyrinth Chollima, Golden Chollima, and Pressure Chollima, each with its own targets, tools, and objectives.
How Labyrinth Chollima Evolved
One of the core findings from the new research is that the original Labyrinth Chollima continues to focus on cyber espionage. Its primary targets include industrial, logistics, manufacturing, defense, and critical infrastructure organizations. In contrast, Golden Chollima and Pressure Chollima have increasingly shifted towards attacking cryptocurrency and digital asset ecosystems worldwide. Despite operating as separate units in terms of operations and toolsets, analysts observe that these three groups still share infrastructure and certain tooling, suggesting centralized planning and resource management within North Korea’s broader cyber program.
Labyrinth Chollima: Beyond the Lazarus Label
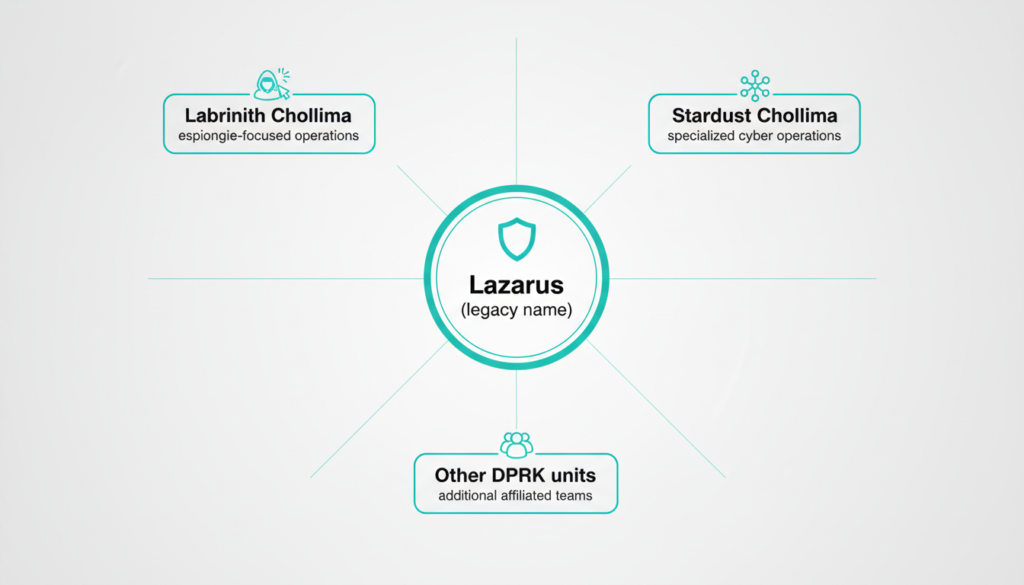
Labyrinth Chollima itself has a long and notorious history. Also known under aliases such as UNC4034 and Temp.Hermit, it has been attributed to some of North Korea’s most impactful operations, including destructive attacks against organizations in South Korea and the United States, as well as involvement in the global WannaCry ransomware incident in 2017. For years, many of these activities were grouped under the broad “Lazarus Group” label, a name used by many Western researchers as a catch-all for multiple North Korean threat actors. Over time, however, intelligence gathering and analysis improved, revealing that “Lazarus” was too broad and actually encompassed many distinct teams with different missions and tooling. This pushed vendors and research bodies to move away from the single Lazarus label and instead classify more precise sub-groups such as Labyrinth Chollima, Stardust Chollima, and others, making tracking and defense more accurate.
Origins: The KorDLL Framework
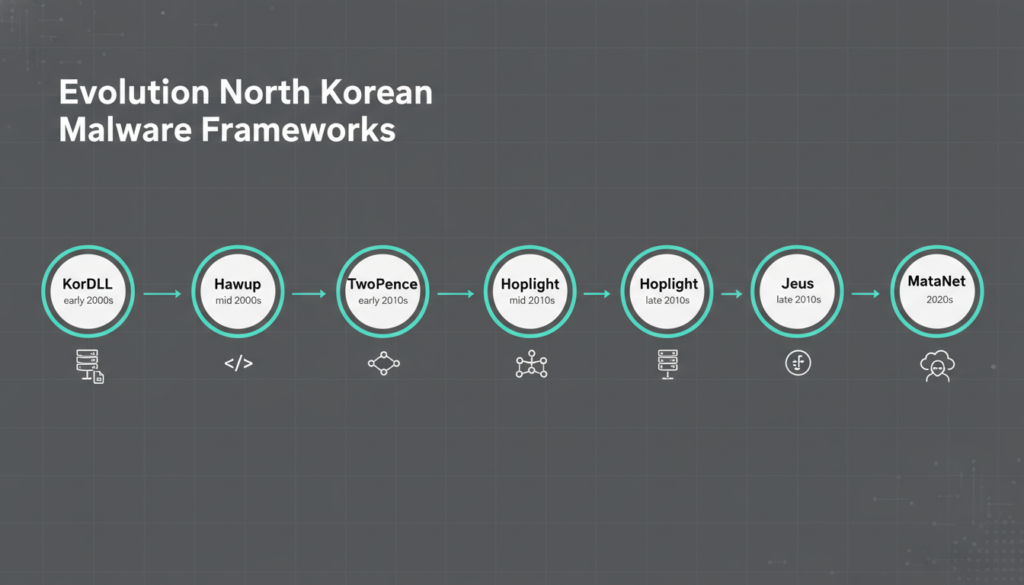
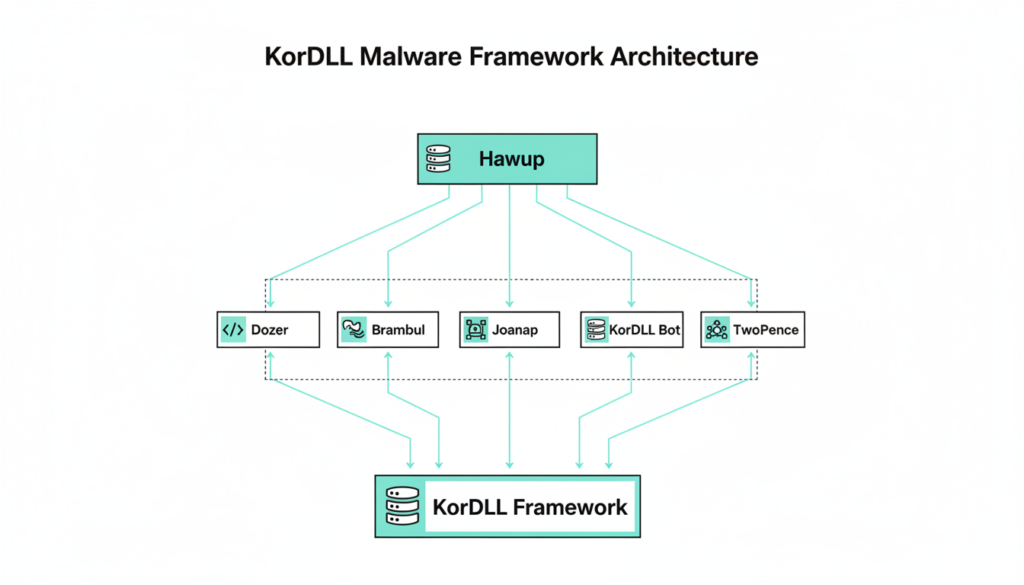
The technical roots of Labyrinth Chollima go back to a shared malware framework known as KorDLL, observed in the wild between 2009 and 2015. KorDLL operated like a development toolkit for North Korean operators, offering implant templates, built in command and control (C2) communication protocols, reusable libraries for common attacker tasks, and code for obfuscation and evasion. From this base, several well known malware families emerged, such as Dozer, Brambul, Joanap, KorDLL Bot, and Koredos. These families played key roles in early North Korean campaigns against financial institutions, governments, and critical infrastructure around the world. Over time, KorDLL evolved into more advanced frameworks named Hawup and TwoPence, which represented generational upgrades. This evolution led researchers to distinguish two related clusters: Labyrinth Chollima, associated mainly with the Hawup framework, and Stardust Chollima, associated with TwoPence and its descendants.
The New Split: Labyrinth, Golden, and Pressure Chollima
In its most recent analysis, CrowdStrike identifies a further branching of these frameworks that maps neatly onto the three newly defined groups. The Hawup line has now evolved into Hoplight, Jeus, and MataNet. Hoplight is used by Labyrinth Chollima, Jeus is used by Golden Chollima, and MataNet is used by Pressure Chollima, often in combination with TwoPence. All three frameworks share design principles: they are modular, support multiple C2 methods, and can be updated quickly to adapt to new targets, platforms, and security controls. This flexibility makes them powerful tools for long-term campaigns and for pivoting between espionage and financial theft.
Golden Chollima: Focused Crypto Theft
Golden Chollima focuses on steady, smaller-scale cryptocurrency theft operations rather than single, dramatic mega heists. It frequently targets regions with strong fintech and crypto activity. The group’s operations often rely on cloud focused tradecraft, such as attacks on virtual machines, containers, and misconfigured cloud services. It is also known to use recruitment and job themed phishing emails, especially targeting developers, engineers, and IT professionals who might have privileged access. By leveraging stolen credentials, remote access tools, and cloud misconfigurations, Golden Chollima aims for consistent, medium-value thefts that collectively generate significant revenue while staying under the radar.
Pressure Chollima: High Value Crypto Heists
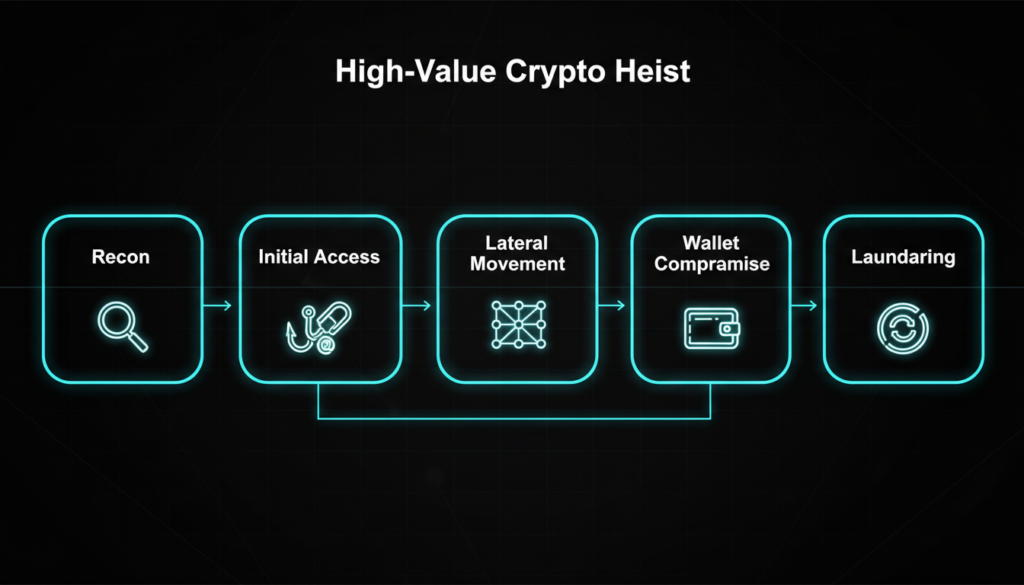
Pressure Chollima, by contrast, goes after large, high value cryptocurrency targets with more complex and tailored operations. This group is associated with advanced, low prevalence implants and carefully customized malware that is not widely distributed, making detection harder. It often targets major exchanges, DeFi platforms, and entities holding large volumes of digital assets. Campaigns may involve extended reconnaissance, exploiting supply-chain relationships, and multi-stage intrusions where initial access is followed by lateral movement, privilege escalation, and careful exfiltration of private keys or hot wallet credentials. Analysts believe that operations like these are crucial for North Korea’s strategy to evade international sanctions, as stolen crypto can be laundered through mixers, nested wallets, and over-the-counter brokers before being converted to usable funds or goods.
Labyrinth Chollima: Espionage and Critical Infrastructure
The original Labyrinth Chollima continues to operate with a more traditional state espionage mission. Its key targets are defense contractors, aerospace companies, manufacturing firms, logistics providers, and critical infrastructure operators such as energy and transport organizations. The group is known for leveraging zero day vulnerabilities, especially in widely deployed software, and using highly convincing spear-phishing lures themed around job offers, contracts, or corporate communications. Labyrinth Chollima also deploys kernel level and low level malware designed specifically to bypass or disable endpoint security tools, giving it persistent, stealthy access to sensitive networks. The aim here is not just intelligence gathering but also strategic advantage, intellectual property theft, and potentially establishing footholds that can be used for sabotage in times of heightened geopolitical tension.

What This Means for Organizations
For organizations around the world, this evolution of Labyrinth Chollima into three more clearly defined units is a strong signal that state backed cyber programs are becoming more specialized and professional. Defense, manufacturing, and infrastructure companies must assume that zero day exploitation and bespoke spear-phishing are persistent threats. Crypto exchanges, DeFi projects, and fintech startups should operate on the assumption that they are attractive and active targets for both Golden and Pressure Chollima. From a defensive standpoint, relying on broad labels like “Lazarus” is no longer sufficient. Security teams need to track the specific tactics, techniques, and procedures, as well as the malware frameworks Hoplight, Jeus, MataNet, and TwoPence associated with each cluster. This more granular understanding supports better threat modeling, more accurate detection rules, and prioritized patching and monitoring strategies in an era where financially motivated and espionage-driven campaigns often come from the same state-backed ecosystem.
CrowdStrike has reclassified the prolific North Korean threat group Labyrinth Chollima into three specialized units: Labyrinth Chollima (espionage against defense, manufacturing, and critical infrastructure), Golden Chollima (smaller-scale crypto theft via cloud attacks and job phishing), and Pressure Chollima (high-value crypto heists with advanced implants). These groups evolved from the KorDLL malware framework (2009-2015), which spawned families like Dozer and Brambul, progressing to Hawup, TwoPence, Hoplight, Jeus, and MataNet. While distinct in TTPs, they share infrastructure, indicating centralized control. The shift reflects North Korea’s maturing cyber program blending espionage and financial crime to evade sanctions. Defenders must track group-specific tools beyond broad “Lazarus” labels for better protection.
Ready to dive deeper?
Explore our latest blogs on AI, TECH, and CYBERSECURITY for cutting edge insights that keep you ahead of the curve. From AI powered threat detection to emerging tech trends and real world cyber defense strategies your next must read is just one click away!
Check out more on our blog page now → AI, TECH, and CYBERSECURITY