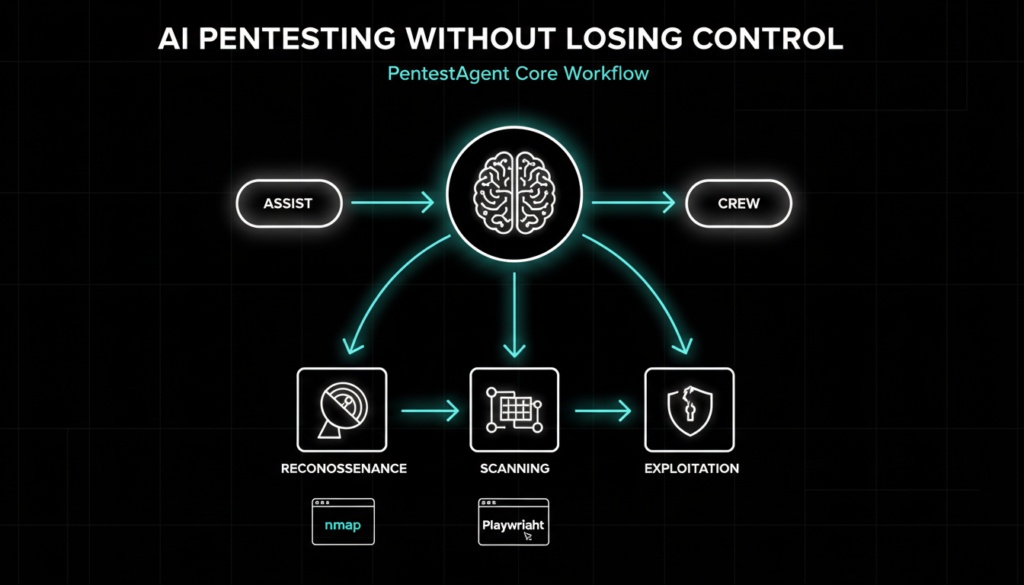
PentestAgent is shaking up cybersecurity testing with its open source AI agent framework. Developed by researcher Masic (aka GH05TCREW), this tool hit GitHub recently and packs prebuilt attack playbooks plus smooth integration with HexStrike. It taps into powerful large language models like Claude Sonnet or GPT-5 through LiteLLM for smart, black box security checks think automated scans that mimic real hacker tactics without needing constant hand holding.
What sets it apart? It’s built for pentesters who want AI smarts but full control. Run it via a slick terminal interface with chat, solo agent, or team modes. A big caveat: stick to authorized systems only unauthorized poking around breaks laws like the U.S. Computer Fraud and Abuse Act or India’s IT Act, 2000. According to a 2025 SANS Institute report, 68% of breaches stem from unpatched web apps, making tools like this crucial for proactive defense.
Key Features at a Glance
At its heart, PentestAgent shines with structured attack playbooks ready made workflows for web app tests inspired by THP3 challenges. Fire one up with a simple command like “pentestagent run
-t example.com –playbook thp3_web.” It walks the AI through recon, scanning, and exploitation, pulling in specialized knowledge via a Retrieval Augmented Generation (RAG) system. Notes from sessions (credentials, vulns, findings) save to loot/notes.json and build a “shadow graph” in Crew mode, where a boss agent spins up worker bots for deeper analysis.
The three modes make it versatile:
- Assist (default): Chat interactively you steer the ship.
- Agent: “/agent <task>” for hands-off single jobs.
- Crew: “/crew <task>” for multi-agent teamwork.
Built-in tools cover nmap and sqlmap in a terminal, Playwright browser control, note taking, and web searches (needs Tavily API). TUI shortcuts like /target <host>, /tools, /report, or Esc to halt keep things intuitive, with /memory showing resource use.
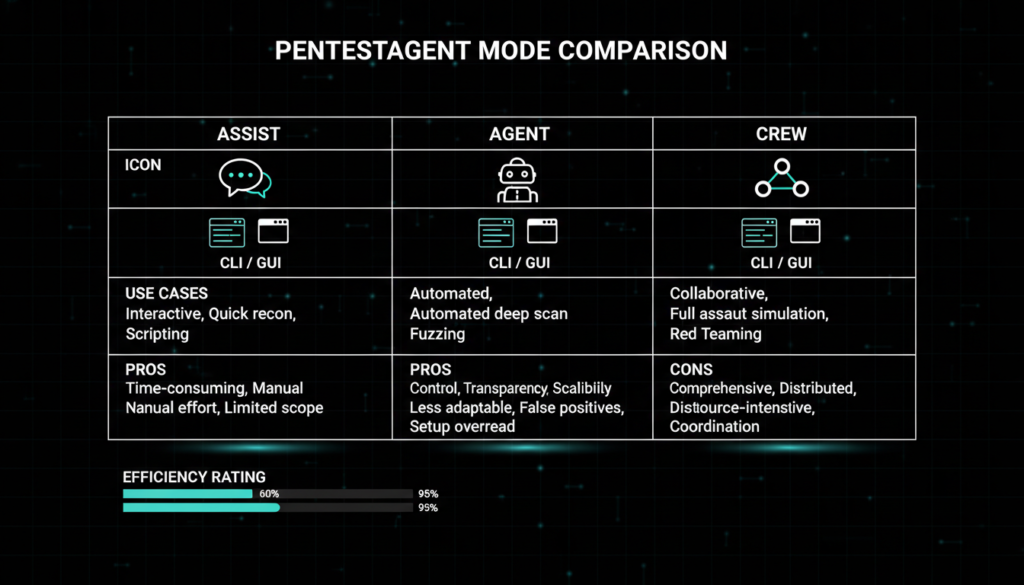
Expanding on this, PentestAgent addresses a gap in traditional tools. Unlike static scanners like Nessus, it adapts dynamically using LLMs Gartner’s 2025 AI Cybersecurity report predicts AI agents will handle 40% of pentests by 2027. It’s especially handy for red teamers simulating advanced persistent threats (APTs), where human oversight prevents false positives that plague fully automated tools.
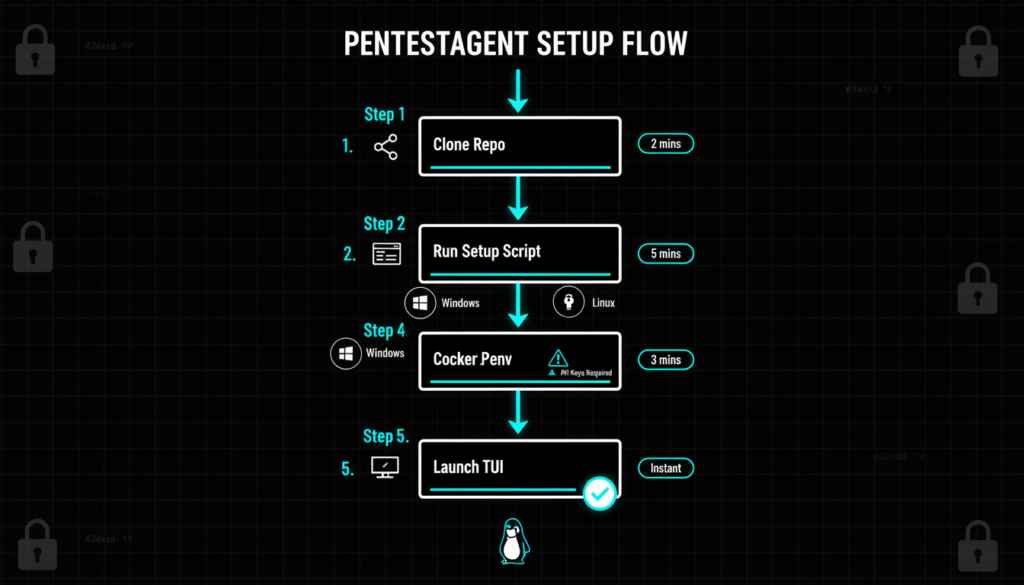
Easy Setup for Any Environment
Getting started is a breeze on Python 3.10+. Clone the repo, run setup scripts (.\scripts\setup.ps1 for Windows, ./scripts/setup.sh for Linux/macOS), and tweak .env with your API key like ANTHROPIC_API_KEY=sk-ant-… and PENTESTAGENT_MODEL=claude-sonnet-4-20250514. Grab Chromium with “playwright install chromium.”
Prefer isolation? Docker images like ghcr.io/gh05tcrew/pentestagent:kali come preloaded with Metasploit and Hydra. Spin it up: docker run -it –rm -e ANTHROPIC_API_KEY=your-key ghcr.io/gh05tcrew/pentestagent:kali. Or build locally via docker compose.
Recent tweaks fixed TUI stability for marathon sessions, making it reliable for enterprise scale tests.
For context, setup mirrors tools like ZAP or Burp Suite extensions but adds AI flair. A 2025 OWASP survey found 72% of devs struggle with LLM configs PentestAgent’s LiteLLM simplifies this, routing to multiple providers for cost savings (e.g., cheaper open models during spikes).
HexStrike Boosts the Arsenal
The killer update? HexStrike integration, baked into third_party/hexstrike. This Model Context Protocol (MCP) framework unlocks pro pentesting tools scoring engines, workflows via mcp_servers.json. Install deps with scripts/install_hexstrike_deps.sh, then add via “pentestagent mcp add nmap ‘npx’ ‘-y’ ‘gc-nmap-mcp’.” Manage with CLI like “pentestagent tools list” or “mcp test.”
HexStrike exposes endpoints for dynamic tool chaining, like feeding nmap output straight to exploitation modules. It’s extensible, letting you plug in custom MCP servers for niche needs, such as cloud specific scans (AWS S3 buckets or Azure AD).
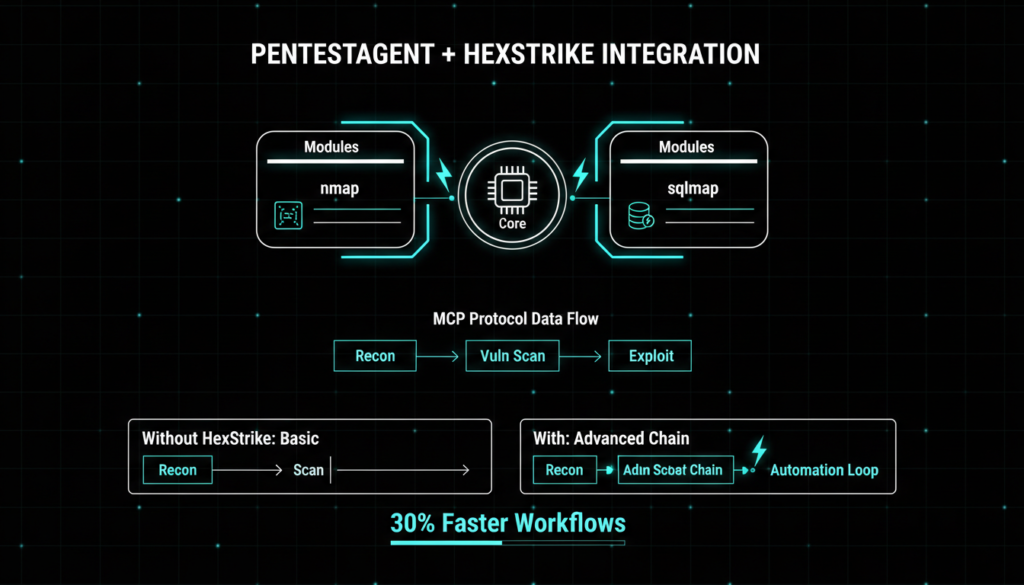
This integration echoes trends in AI cyber fusion. Per a MITRE 2025 eval, MCP like protocols cut tool switching time by 50%, vital as attacks evolve think Log4Shell style chains. Compared to rivals like AutoPentest DRL, PentestAgent’s open source edge (no licensing fees) appeals to indie researchers and SMBs.
Real World Impact and Best Practices
In practice, PentestAgent excels for bug bounties or compliance audits (SOC 2, PCI-DSS). Picture hunting XSS in a dev site: Launch thp3_web playbook, let Crew mode graph findings, export /report as Markdown/PDF. Ethical hackers praise its RAG for injecting OWASP Top 10 context, reducing hallucination risks common in raw LLMs.
But wield it wisely. Pair with human review AI misses context like business logic flaws (seen in 25% of real breaches per Verizon’s 2025 DBIR). Start small: Test on DVWA or Juice Shop. For teams, Crew mode scales to simulate zero days, aligning with NIST’s AI RMF for trustworthy automation.
Future proofing? GH05TCREW hints at vision model support for screenshot analysis and Burp Suite bridges. With AI pentesting projected to grow 35% YoY (IDC 2026 forecast), tools like this democratize elite skills.
Why PentestAgent Matters Now
As cyber threats surge ransomware up 150% in 2025 (Chainalysis) AI agents like PentestAgent level the playing field. It’s free, flexible, and future ready, blending human intuition with machine speed. Grab it from GitHub, test ethically, and stay ahead.
Check out more on our blog page now → AI, Tech, Cybersecurity