In the fast evolving world of AI tools, cybercriminals are getting craftier. A new SmartLoader campaign trojanizes a popular Oura MCP server designed to link AI assistants with Oura Ring health data to sneak in the StealC infostealer. This steals credentials, browser passwords, and crypto wallet info from victims. Cybersecurity firm Straiker’s AI Research (STAR) Labs uncovered this, revealing how attackers cloned the legit server and built fake credibility on GitHub.
What Fuels SmartLoader’s Rise
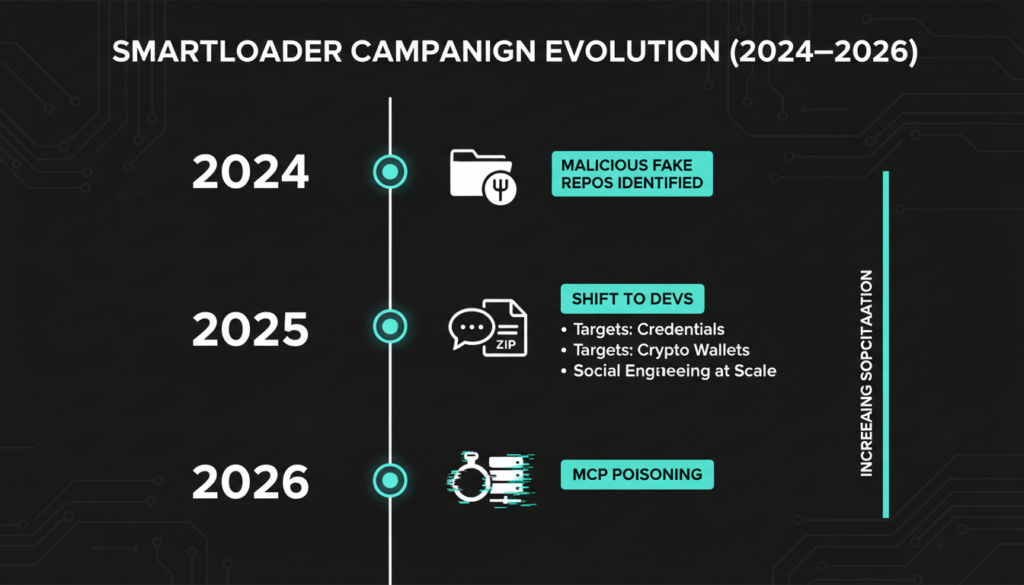
SmartLoader first surfaced in early 2024, spotted by OALABS Research as a loader hiding in fake GitHub repos baited with AI generated lures. These mimic game cheats, cracked software, or crypto tools, tricking users into downloading ZIPs that unleash the malware. Trend Micro’s March 2025 report expanded on this, noting how attackers use AI to craft convincing repo descriptions and READMEs, blending them seamlessly with real projects. The loader then deploys stealers like StealC, which has evolved to target not just consumers but high value developer machines packed with API keys and cloud creds.
This Oura twist marks a pivot: attackers spent months faking legitimacy instead of rushing opportunistic hits. They poisoned MCP registries like MCP Market still listing the rogue server by submitting trojanized versions amid legit ones. MCP, or Model Context Protocol, lets AI models securely access external data sources, but its open ecosystem invites abuse, much like early supply chain attacks on npm or PyPI packages.
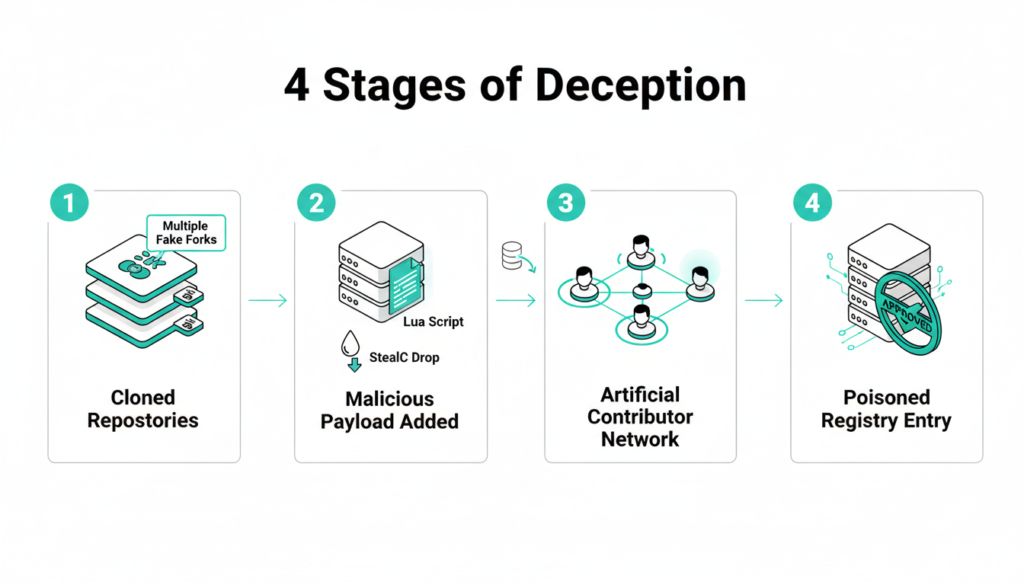
How the Attack Unfolds Step by Step
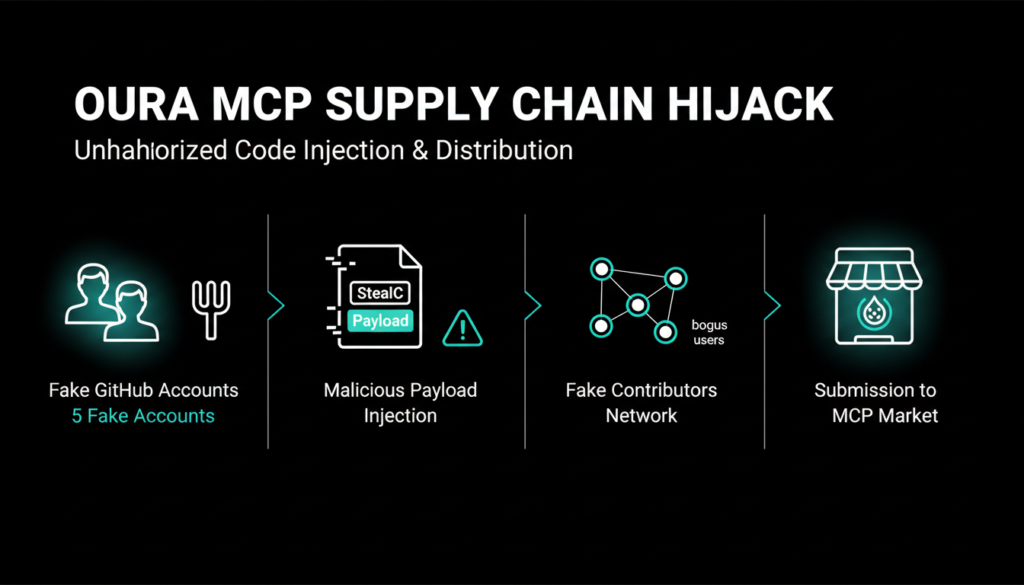
The campaign breaks into four calculated stages, showcasing attackers’ patience. First, they spun up at least five fake GitHub accounts YuzeHao2023, punkpeye, dvlan26, halamji, and yzhao112 to fork the original Oura MCP server repo. This created a web of “legit” activity. Next, under a new account “SiddhiBagul,” they built a fresh repo embedding the malicious payload: an obfuscated Lua script that drops SmartLoader upon ZIP extraction.
Building Fake Trust
Stage three ramped up deception by listing those fake accounts as contributors, while ghosting the real author. This mimics organic collaboration, fooling GitHub’s trust signals. Finally, they submitted it to MCP Market, where it lingers among safe options. Developers hunting Oura integrations might grab it unwittingly, launching the chain: SmartLoader injects StealC, which exfiltrates data via encrypted channels.
Additional intel from cybersecurity trackers like MITRE ATT&CK frames this as a classic supply chain compromise (T1195.001), akin to SolarWinds but targeted at AI devs. StealC itself, per 2025 analyses, grabs data from 50+ browsers and 20+ wallet types, including MetaMask and Exodus, then phones home to attacker C2 servers.
Why Developers Are Prime Targets Now
SmartLoader’s shift from pirate-hunters to devs exploits goldmines: source code with secrets, prod access, and crypto holdings. Straiker notes this “patient approach” nets higher rewards, as devs rarely vet AI tools deeply. Broader context from Anthropic’s MCP docs highlights its promise for agentic AI letting models query real time data like health metrics but warns of unvetted servers risking persistence via cron jobs or outbound traffic spikes.
Trend Micro’s 2025 deep dive adds that SmartLoader variants now fingerprint systems for dev tools (VS Code, Docker) before payloading, evading sandboxes. In India, where AI adoption surges (per NASSCOM 2025 reports), this hits home local devs building health AI could lose Oura-linked prototypes to such chains, fueling ransomware or espionage.
Smart Defenses Against MCP Threats
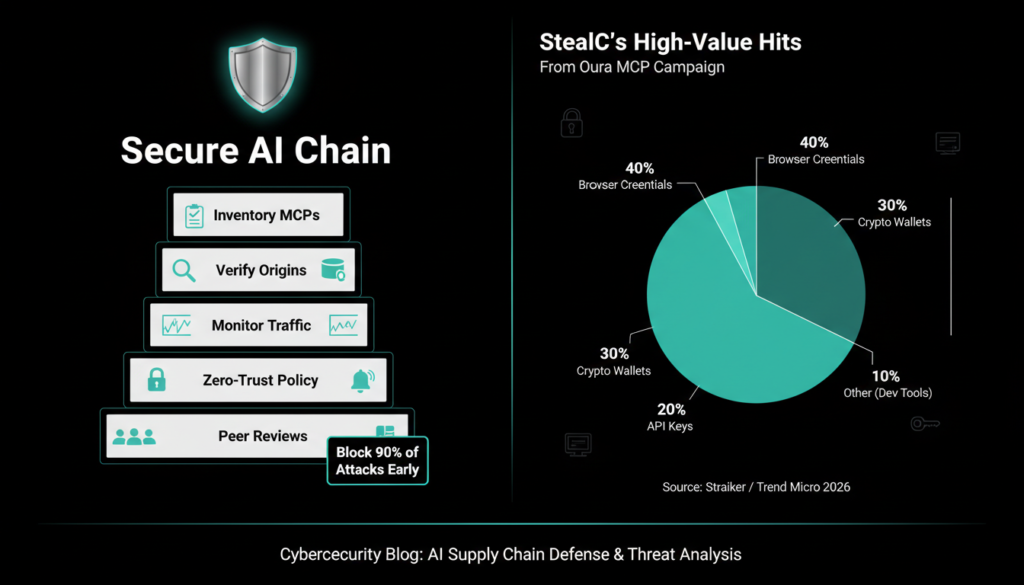
Fight back with these steps: Inventory all MCP servers on your systems, enforce peer reviews before installs, and verify repos via original authors. Monitor for odd Lua executions, C2 beacons, or wallet drains using EDR tools like CrowdStrike or open source Sigma rules. Block known IOCs fake GitHub handles and StealC hashes from Straiker’s report.
Organizations should bake MCP into supply chain policies, scanning for anomalies like sudden contributor surges. As AI surfaces grow (think A2A protocols), adopt zero trust: sign tools cryptographically and limit AI agent scopes. This campaign spotlights AI tooling’s blind spots trust no repo at face value.
This attack underscores AI’s double edge: powerful integrations breed new vectors. Stay vigilant as MCP like protocols boom.
Check out more on our blog page now → AI, Tech, Cybersecurity