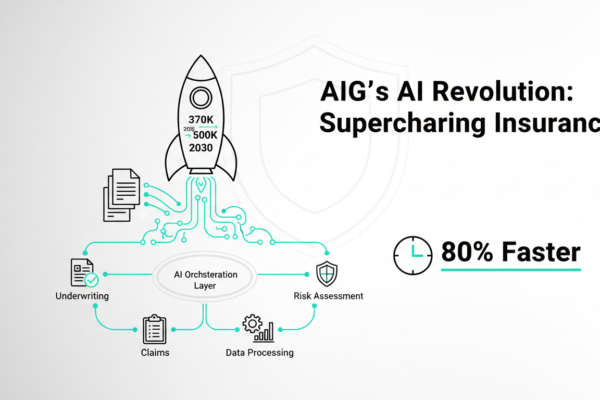
AIG’s AI Breakthrough: Faster Gains in Insurance
American International Group (AIG), a global insurance powerhouse, is seeing explosive results from generative AI far quicker than anticipated. At their recent Investor Day, AIG shared hard data on boosted underwriting capacity, slashed operating costs, and seamless portfolio integration. For AI leaders in finance and insurance, this isn’t hype; it’s proof of measurable workflow overhauls…