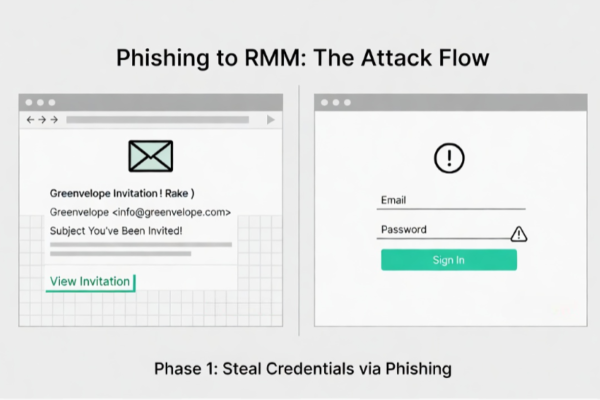
How Phishing Leads to LogMeIn RMM
A new cybersecurity campaign shows how attackers are skipping custom malware altogether and instead abusing trusted tools like Remote Monitoring and Management (RMM) software to gain long term access to victim systems. In this dual phase attack, hackers first steal email credentials through a phishing campaign, then use those logins to silently install and control…
